Well, I have followed this step-by-step, exactly:
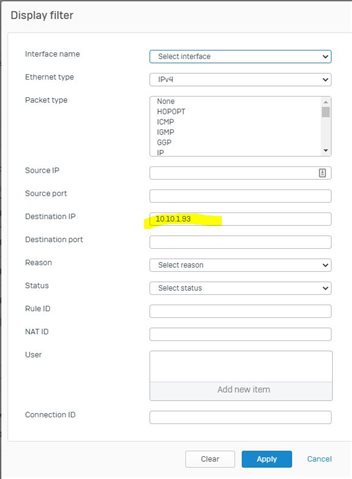
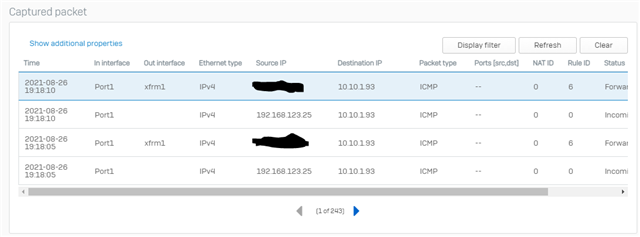
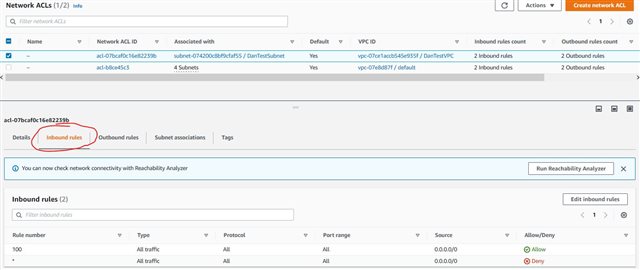
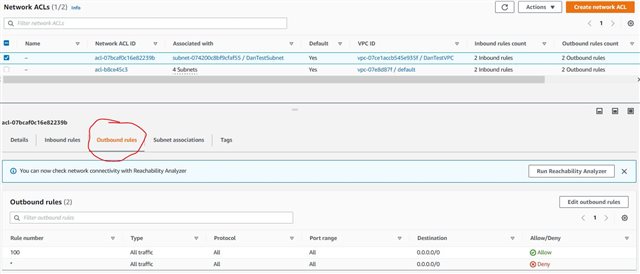
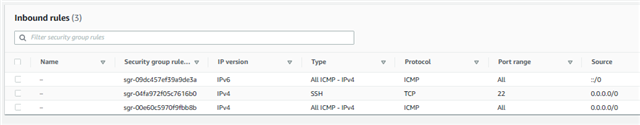
....and while the VPN shows "UP" in both AWS and my Sophos VPN section, I cannot PING or SSH to my test EC2 instance. In the bottom screenshot you'll see I have PING and SSH allowed from anywhere (0.0.0.0/0). I've been at it for hours, first because I mistakenly followed the v17. Even with the v17 how-to, my VPN said it was up in AWS and Sophos VPN section. Then I found v18 and thought for sure I would have success. No such luck.
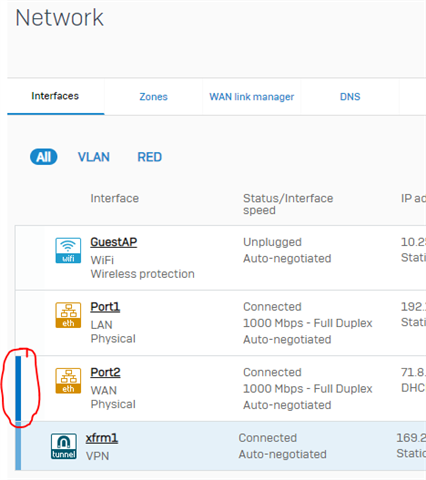
At one point I got stuck at the part where I couldn't find my "xfrm" interface until I realize that little vertical blue line meant I could expand my WAN interface, thanks to THIS ARTICLE. Again, I thought for sure I would have success. No such luck again, and now I'm at a loss.
The only difference I've noticed between my setup and the setup in the link above, is in Step 9 and Step 10, I have "xfrm1" not "xfrm2".
Anyone know where I should start with troubleshooting?
This thread was automatically locked due to age.