Greetings my sophisticated friends and a happy February to you all! As always, the Central platform is bustling with new features and early access programs. Attackers never cease to innovate and neither do we - take that badguys #boomheadshot. Yup, I'm as professional as ever... Moving swiftly on.
This month we have a huge number of truly awesome things to tell you about so kick back with a hot cup of cocoa and read on.
- General Availability
- Early Access Program
(Feel free to click on any of the numbered items above to jump straight to any item in particular.)
General Availability
By General Availability (GA), we mean that this functionality has been released and is ready for you to dive into and start using. Often, new products or features first start out as Early Access Programs (EAP) before they become Generally Available after we've had your insights and feedback, helping us deliver the best possible products.
XG Firewall Management
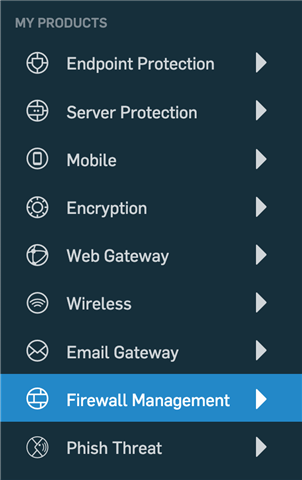 This is a landmark release - Sophos XG Firewall has now joined the Sophos Central platform! You can now connect your XG Firewall to your Central account and remotely manage it wherever you are - no complicated configuration required.
This is a landmark release - Sophos XG Firewall has now joined the Sophos Central platform! You can now connect your XG Firewall to your Central account and remotely manage it wherever you are - no complicated configuration required.
We've developed a secure and innovative way to provide full access to a connected XG Firewall's interface so that you can jump into the firewall right from within your Central account. This is fantastic for managing appliances that are all over the globe, in different offices or regions, without the need to expose the web admin to the internet or configure VPN tunnels.
This release marks a major milestone in our vision for the Sophos Central cybersecurity platform. All major pillars of effective cybersecurity can be orchestrated from a single platform, through a single console, completely redefining what it is to do security.
We couldn't be prouder!
Head on over to the Sophos Blog to learn more about this amazing release.
Threat Analysis Center
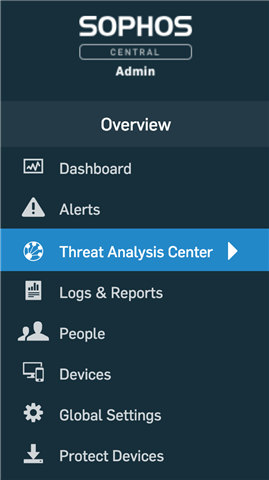 With the advent of bringing EDR to Intercept X for Server, and our exciting plans for our intelligent EDR solution over the course of 2019, we are launching a whole new section of the Sophos Central Admin dashboard - the Threat Analysis Center.
With the advent of bringing EDR to Intercept X for Server, and our exciting plans for our intelligent EDR solution over the course of 2019, we are launching a whole new section of the Sophos Central Admin dashboard - the Threat Analysis Center.
All Threat Cases, and Threat Searches, across all device types - endpoints and servers - will be unified into the Threat Analysis Center. As we evolve our EDR solution over the coming months, this new section will provide a single location for detection and remediation to be performed, as well as investigations and analyses of threats.
You can find the new Threat Analysis Center right in the Overview of the Sophos Central Admin dashboard as you log into Central.
More details can be found on our Community blog.
Sign In with Azure AD
We've extended the authentication options for Central Admin, Enterprise, and Self-Service to now support Microsoft Azure AD Federation.
This means you can leverage your existing Azure AD credentials to log into Central, as well as enabling the use of whatever 2FA/MFA you're using in Azure. And don't panic - your credentials aren't exposed to us - Azure AD handles the authentication on our behalf.
To get this working, you do need to authorize Sophos Central to access your Azure AD credentials via the Azure AD Admin.
For more info on the whole process, check out our knowledge base.
Global Policies for Enterprise and Partner
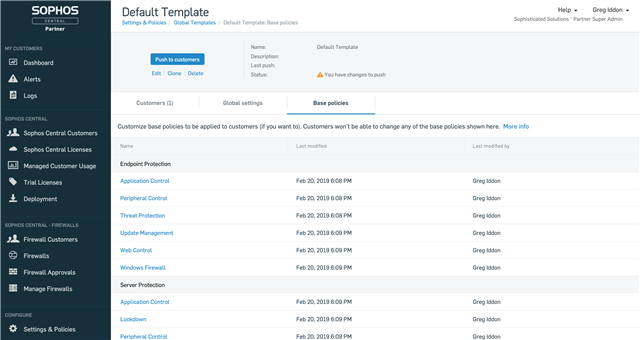 We're dedicated to ensuring the Central platform makes everyone's lives simpler and safer. This month, we're bringing the concept of Global Policies to our Enterprise and Partner dashboards.
We're dedicated to ensuring the Central platform makes everyone's lives simpler and safer. This month, we're bringing the concept of Global Policies to our Enterprise and Partner dashboards.
Global Policies make managing multiple sub-estates or multiple customers a breeze. You can now define policy "templates" then allow you to bundle up global settings and base policies. These templates can then be applied to one or more sub-estates or customers.
Setting up or changing policy configuration across numerous sub-estates or customers is now trivial and rapid!
Click either Partner or Enterprise(available next week) to learn more about these new features.
Sub-Estate Region Selection for Enterprise
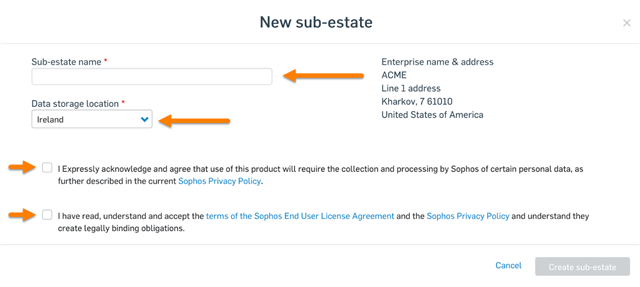 We understand that enterprises have offices all over the globe and, especially with different data protection laws in each region, it's sometimes needed to ensure that data from a region stays in that region.
We understand that enterprises have offices all over the globe and, especially with different data protection laws in each region, it's sometimes needed to ensure that data from a region stays in that region.
For that reason, we're introducing a new feature to enable the setup of a new sub-estate to be in a different region from that of the Enterprise dashboard. Your headquarters might be in the United States but your engineering team might be in Germany. Now you can keep your German colleague's data in Germany and your American colleagues' data in America.
Hop on over to our knowledge base to learn more about how to start making use of this great new feature.
Audit Logs for Partner
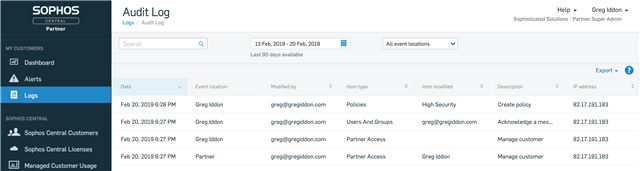 When your admins are hopping in and out of customers accounts, hunting down threats and remediating them, or making policy changes, it's good to have a trail of what they've been up to so that they are accountable for those changes.
When your admins are hopping in and out of customers accounts, hunting down threats and remediating them, or making policy changes, it's good to have a trail of what they've been up to so that they are accountable for those changes.
You can now find the Audit Logs in the Partner dashboard. Head on over to our documentation page to learn the ins and outs of.
Phish Threat Updates
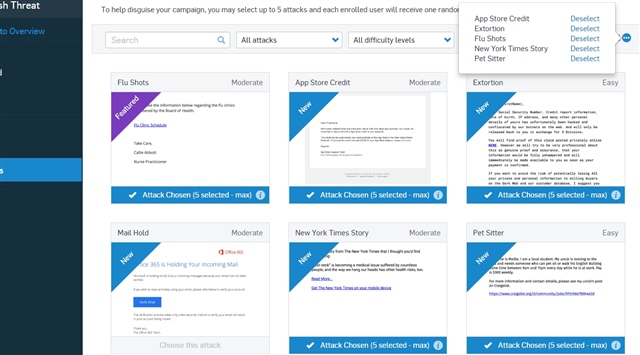 Our excellent user awareness, training, and phishing tool, Phish Threat, has received a couple of nifty updates this month too.
Our excellent user awareness, training, and phishing tool, Phish Threat, has received a couple of nifty updates this month too.
The first new addition is Randomized Attacks! You can now select up to five different attack email templates which will be served out in a random order to your users. This will save you time running multiple campaigns simultaneously as well as improve the effectiveness of the awareness training. More details can be found on our Community blog.
Our second addition is that Phish Threat is now available in Dutch. You'll now be able to carry out phishing simulations and a variety of cybersecurity awareness course in Dutch. Geweldig nieuws! More details can be found on our Community blog.
Email Content Control
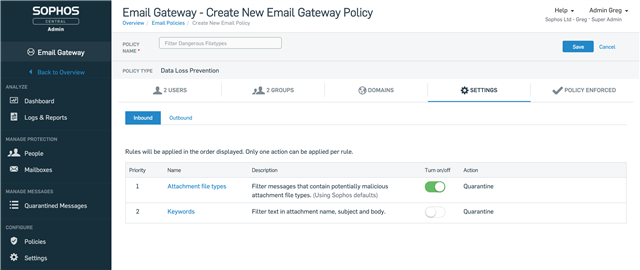 Our last feature being made Generally Available this month gives you the power to filter emails based on keywords and filetypes, both inbound and outbound. This is part of our new Data Loss Prevention policy.
Our last feature being made Generally Available this month gives you the power to filter emails based on keywords and filetypes, both inbound and outbound. This is part of our new Data Loss Prevention policy.
You can craft lists of keywords to look for in subject lines, body content, and file attachment names. When Email finds one of these keywords, an action is performed - pick between Quarantine, Strip attachments and deliver, or Delete.
Using Sophos' True File Type detection technology, define a list of file types to filter emails attachments by (or use Sophos' list of recommended file types to block) and perform an action - Quarantine, Strip attachments and deliver, or Delete.
The power of True File Type detection ensure that even if a file extension has been renamed, for example .zip to .jpg - a common tactic to circumnavigate email filters. We analyse the file and determine its true file type so that all you have to think about is what types of files you want to filter.
More detail can be found on this Community Blog post.
Early Access Programs
EAPs are our way of letting customers get access to upcoming products and features ahead of their release. This month we are launching two new EAPs which customers can join right away and get their hands on our latest innovations before they are released.
Intercept X for Server EDR EAP
 Our first, and perhaps most exciting bit of news, is EDR is coming to Server (I can hear your cheers of joy from here). As is customary, we will first have an Early Access Program for this new feature before we make it Generally Available. And EAP does not mean “beta” – this thing is ready to be put through its paces!
Our first, and perhaps most exciting bit of news, is EDR is coming to Server (I can hear your cheers of joy from here). As is customary, we will first have an Early Access Program for this new feature before we make it Generally Available. And EAP does not mean “beta” – this thing is ready to be put through its paces!
All of the tasty EDR goodness you know and love from Intercept X on the endpoint will be available for Windows Servers. Do note that the EAP will initially be of EDR v1.0 however the EAP will be updated in April with EDR v1.1. GA is currently planned for May.
The biggest takeaway is that this really strengthens our EDR offering and should make selling EDR, in general, much much easier. EDR + the best Protection around, for both endpoints and servers, all in the industry’s most advanced and featureful cybersecurity platform – Sophos Central. Gone are the awkward conversations where you have to explain we don’t have EDR for Server – HERE IT IS. BOOM. #micdrop. (Yikes, I really need to grow up…)
To join, simply log into Sophos Central > Select Early Access Programs > Select ‘Join’ > Accept the terms and get stated.
Email Encryption EAP
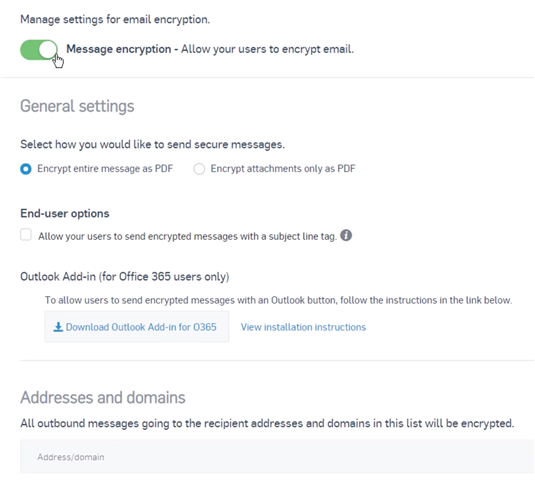 Rounding up our EAPs this month, we're bringing easy-to-use encryption to Email!
Rounding up our EAPs this month, we're bringing easy-to-use encryption to Email!
You'll be able to encrypt either the whole email or just the attachments with flexible policy control. Encrypting an email is as simple as adding a custom tag to the email subject line or using the Office 365 add-in button.
Recipients are prompted to create a password they use to receive encrypted email and are prompted to set this up before encrypted emails are delivered. All subsequent emails are encrypted using this password.
We have a portal that recipients can use to reply to emails securely, ensuring confidential communications remain encrypted at all times.
We are leveraging encrypted PDF technology to achieve this for the majority of file types and email body content however, if the document is a Microsoft Office document (.docx, .xlsx, .pptx, .???x), we will use the native encryption to Office to ensure encrypted documents are frictionless to use.
If you want to learn more, head to our Community blog.
Well that brings us to a close of this month's Central Update. I'll leave you with two fun facts:
- There are about 450 types of cheese in the world. 240 come from France (for which I am eternally grateful).
- England is smaller than New England yet England as 3.7 times the population of New England. Go figure!?