Hello everyone,
We are going to publish a HTTPS website through Cyberoam UTM. As you know, we always create a new Virtual Host for publishing a new service for internet users. But in this scenario, we have encryption considerations. In such scenarios, we need to generate a CSR and install issued certificate. The question is that, where to generate CSR and install certificate? Cyberoam or Server?
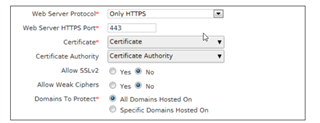
For the clarification: I've read if we are going to use WAF, we are supposed to generate CSR and install certificate on Cyberoam (Everything would be done on UTM). But if we use Virtual Host (Port Forwarding), everything (CSR and installation) must be done on Server.
Am I right? or...
This thread was automatically locked due to age.