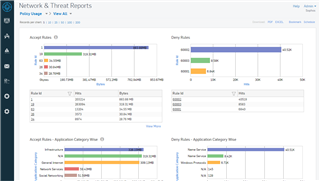
Am I right that in policy usage only deny rules are reported/visible?
In case you want to look for the best order of rules or if you're looking if rules are not needed anymore this report is completely useless...
I'm using UTM 9.3 OS.
This thread was automatically locked due to age.