Hello everyone
I am struggeling with the following:
The customer has microtik router that connects via wireguard VPN to a remote Windows Server in a Datacentre.
The Microtik router is the VPN Client, the Windows Server is the VPN Server.
The employees are supposed to print from the remote Windows Server to local LAN printers.
Setup:
Local LAN 192.168.5.0 /24
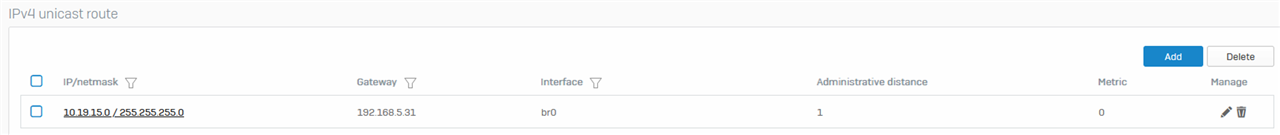
VPN: 10.19.15.0 /24
in SFOS 19 I only needed to set a static route 10.19.15.0/24 with Gateway (Microtik router) on br0 to make it work.
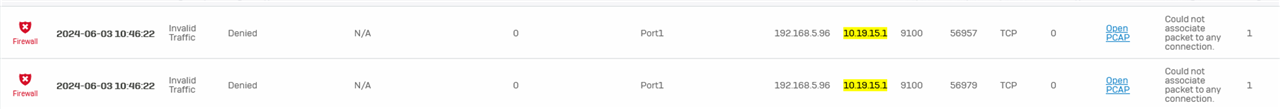
Since upgrading to SFOS 20 the VPN connection suddenly stopped working.
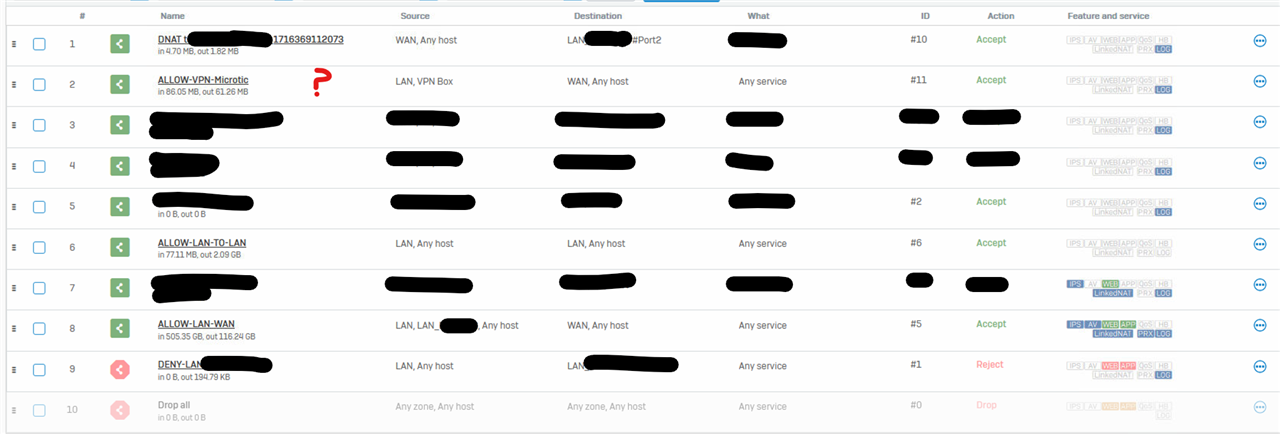
Which Rules do I need to set in place, to tell the XGS that:
- Data from the VPN 10.19.15.0 are okay to access the local LAN ( logs tell me that the XGS can't associate the Microtik VPN traffic with any connection ).
Thanks
This thread was automatically locked due to age.