We have XGS4500 active-passive cluster and i stubled across a pretty annoying issue.
In the past (with XG450 and others) we always set the peer administration address to something that allowed us no monitor the auxilary device via our monitoring solution. Usually that was just an IP higher then the primary device. On the same interface and on the same subnet as the primary management IP.
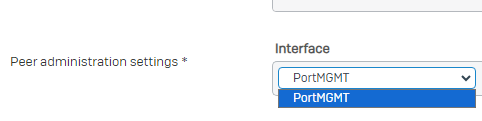
On XGS4500 this does not seem to work anymore. The only interface that i am able to select in peer administration settings is "PortMGMT". We do not use PortMGMT as we manage our devices through the primary interfaces/VLANs. However, if i set peer administration to PortMGMT and use an IP from a subnet that is accessible as well through the primary interfaces, the routing collapse, as it seems to prefer routing through physically connected interfaces (even its PortMGMT) instead of the static routes set.
This is a complete mess in my opinion!
- Why can't i select other ports then PortMGMT anymore for peer administration?
- Why does PortMGMT participates in routing? If it is meant to act as out-of-band MGMT, then it definately should not have any impact on routing!
This thread was automatically locked due to age.


