Hi everyone, I really need some help. I've already tried some KBs but no luck.
I'm having some trouble configuring my branch office users to connect to my Active Directory Server on the head office site.
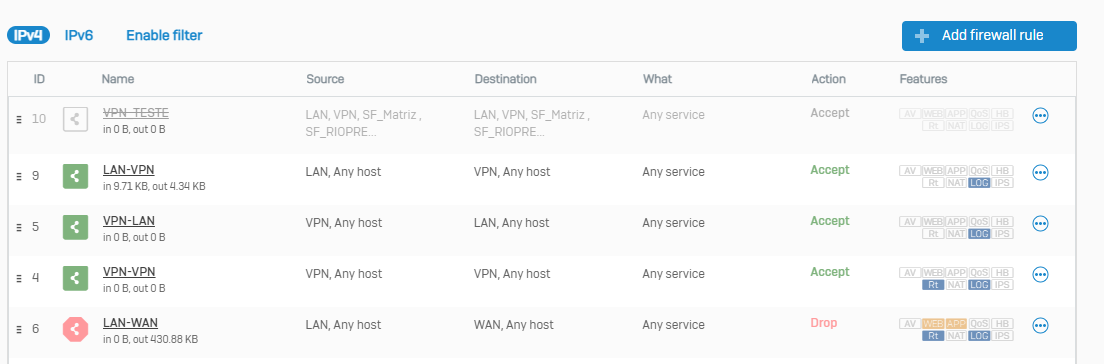
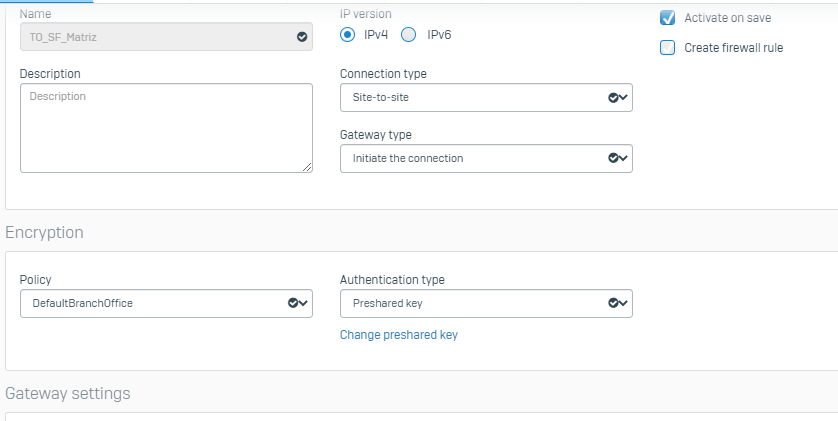
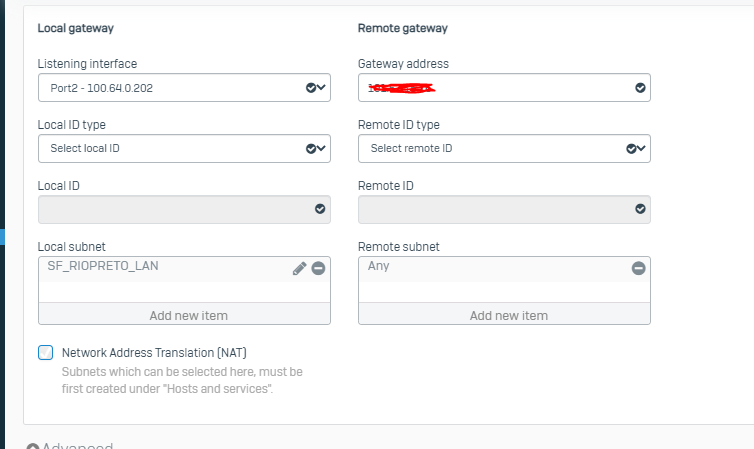
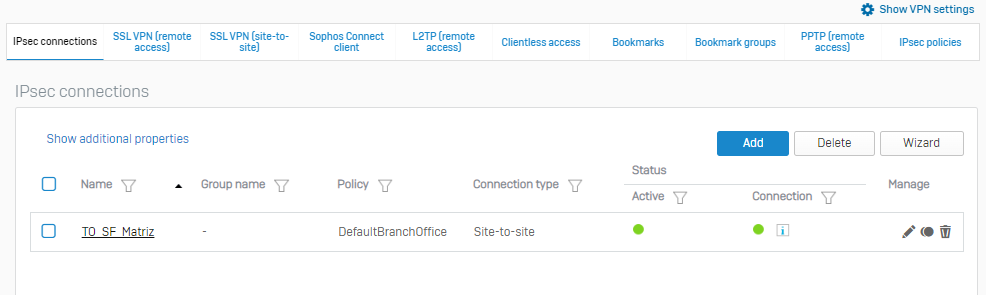
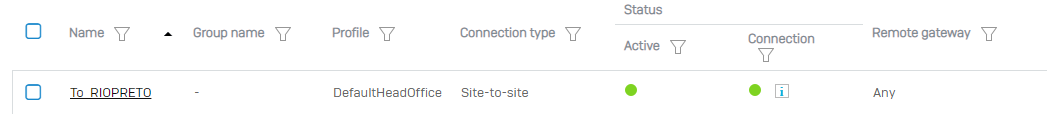
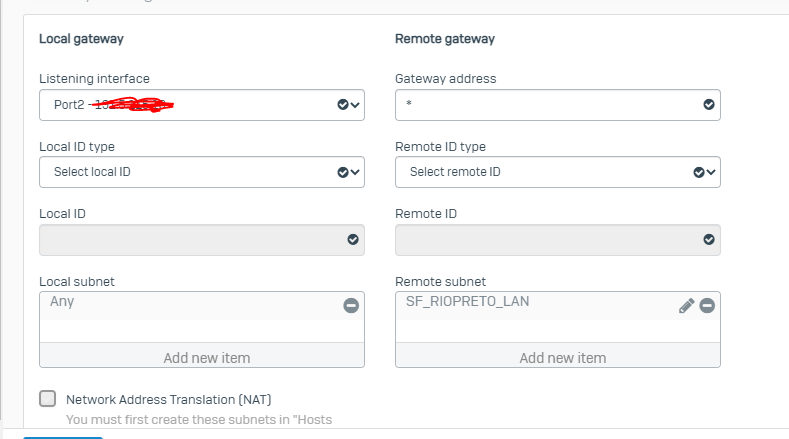
I have already set up IPSec VPN from Head Office (Sophos XG 115) to Branch Office (Sophos XG 105 without license).
I have already followed the KBs: https://docs.sophos.com/nsg/sophos-firewall/19.0/Help/en-us/webhelp/onlinehelp/AdministratorHelp/Authentication/HowToArticles/AuthenticationAllowSTASOverVPN/index.html#introduction
https://support.sophos.com/support/s/article/KB-000035839?language=en_US
What is happening:
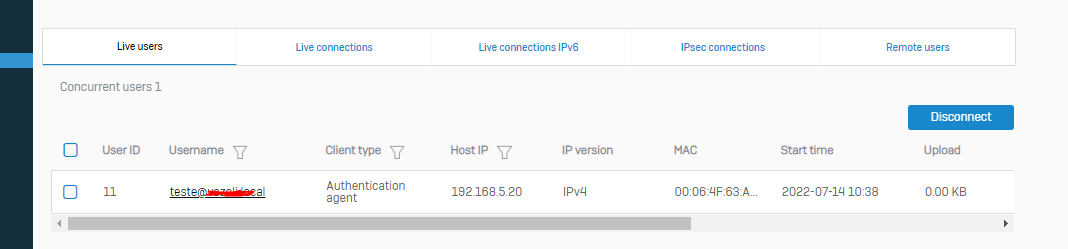
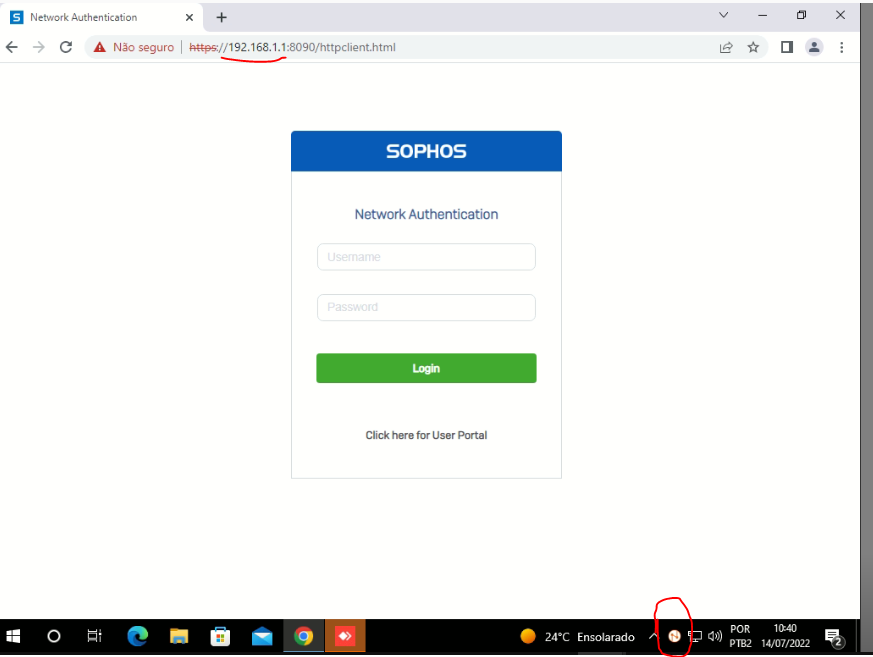
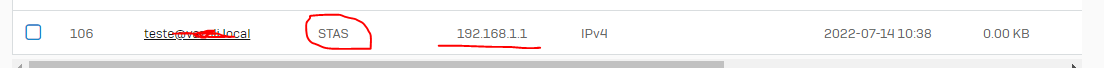
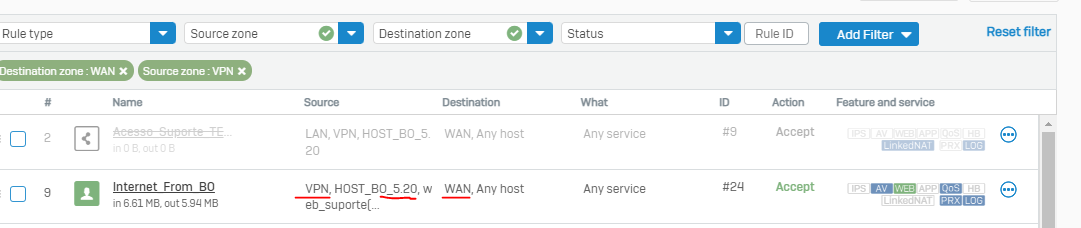
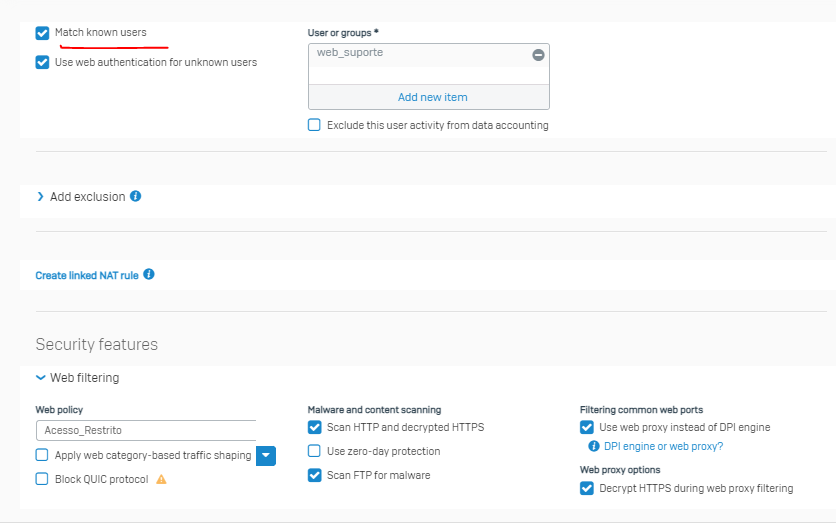
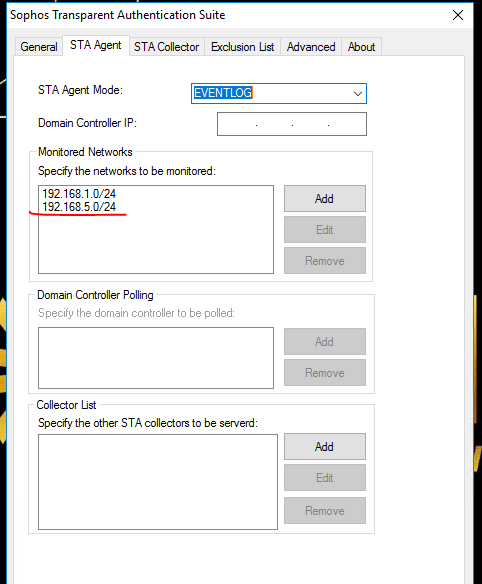
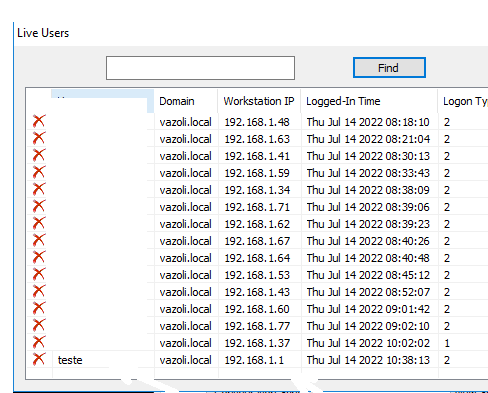
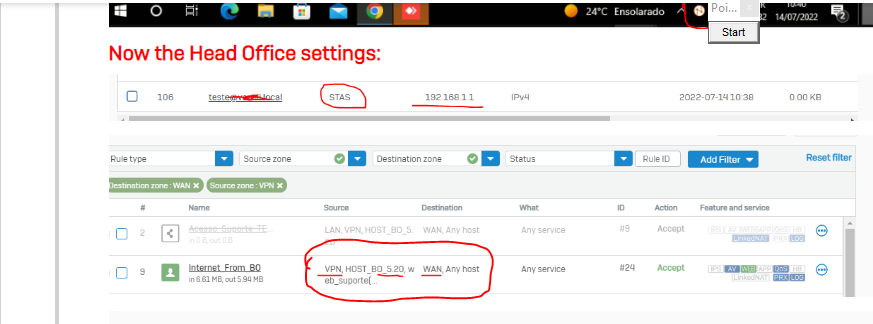
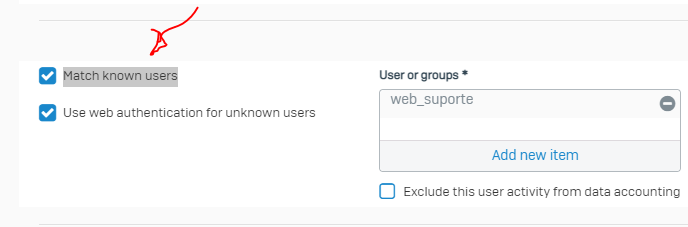
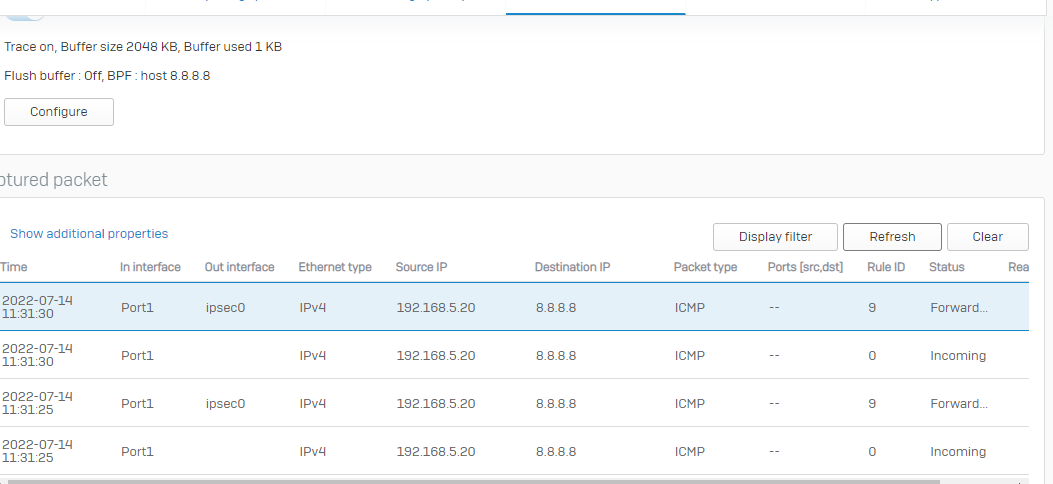
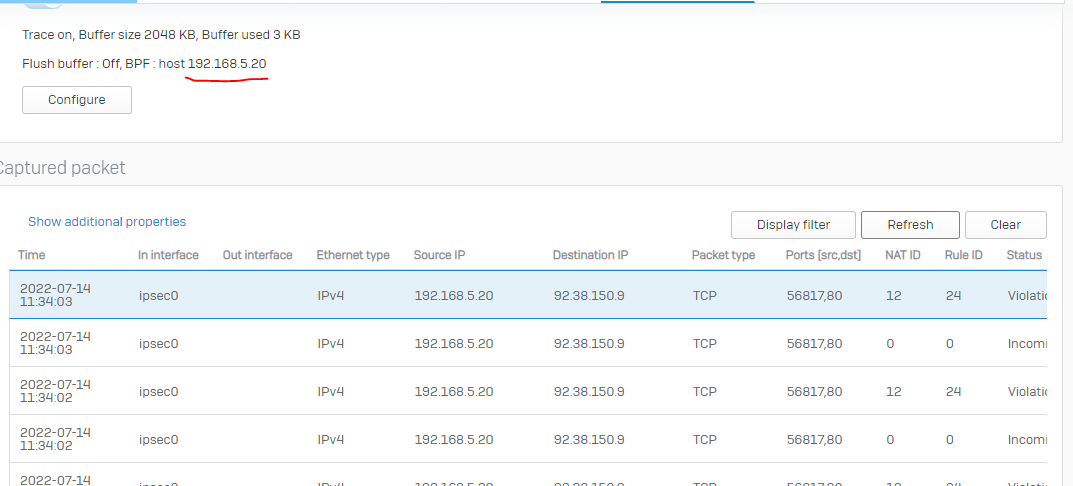
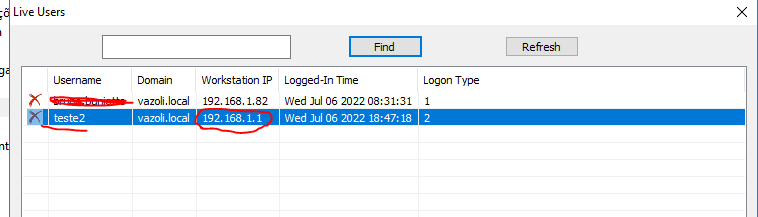
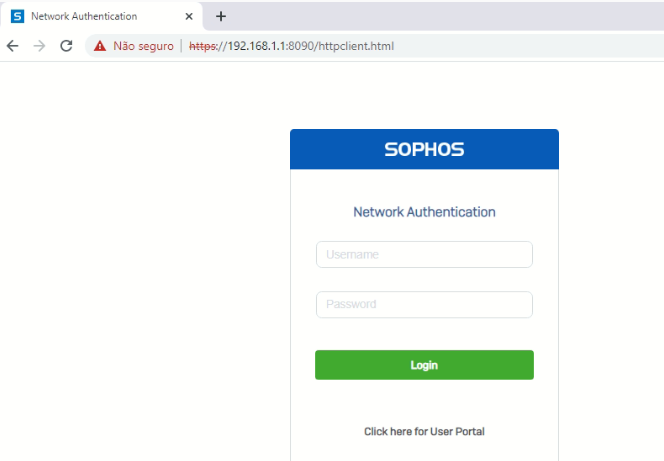
By the time I login in the computer on the branch office (using a domain user), Sophos Firewall at Head Office gets the IP from Sophos Firewall Branch Office and not the IP from the workstation. After logging in, the browser pops up the login page from sophos firewall from Head Office. I can log through it normally, but the transparent authentication won't work.properly.
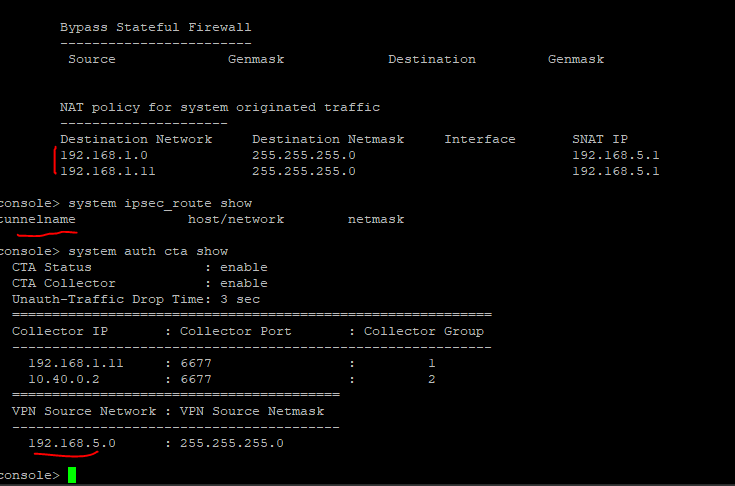
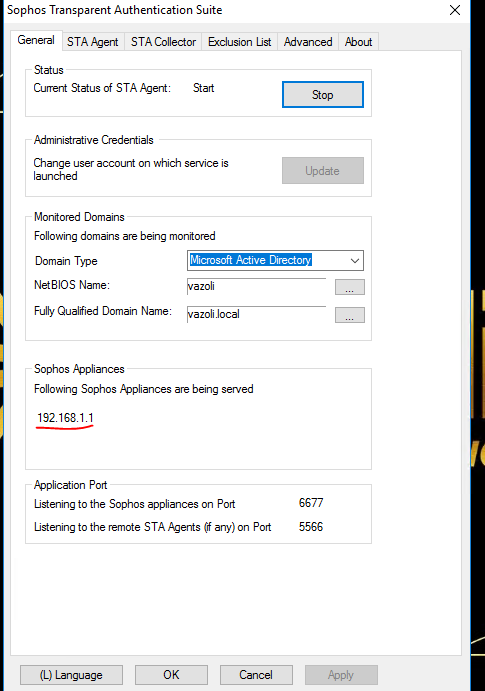
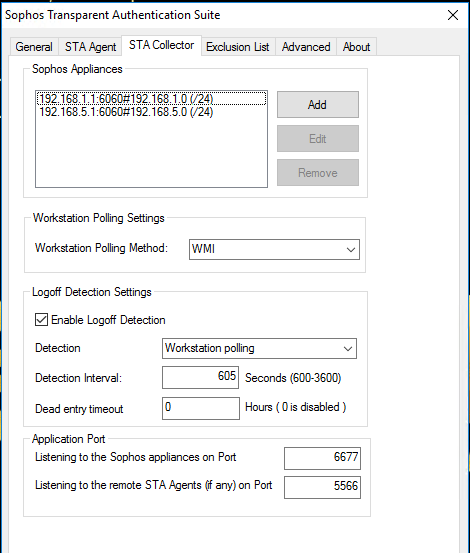
Sophos Firewall on the Head Office site: 192.168.1.1
Sophos Firewall on the Branch Office site: 192.168.5.1
Workstation on the Branch Office site: 192.168.5.20
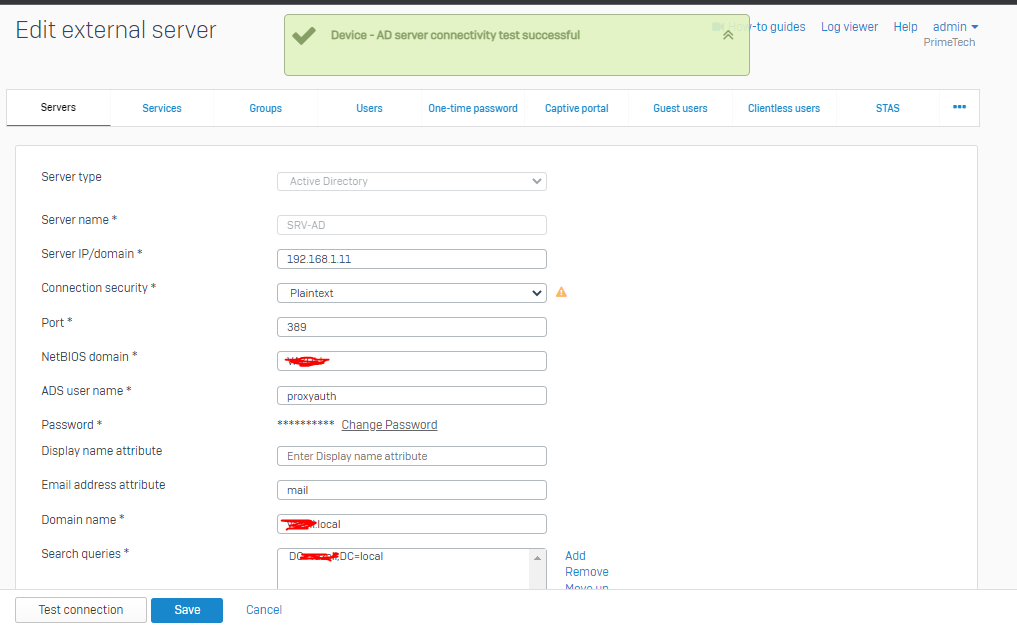
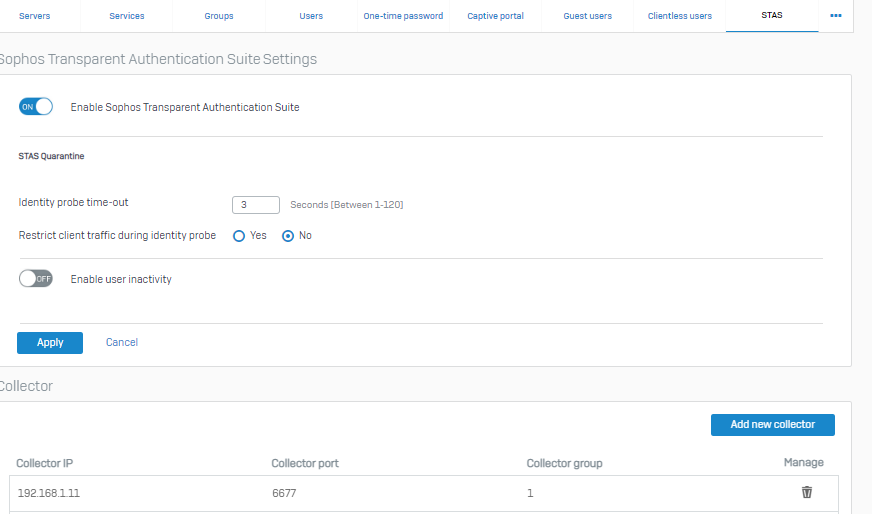
Domain controller: 192.168.1.11
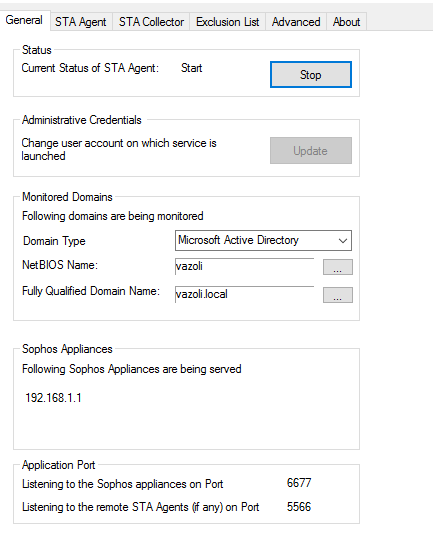
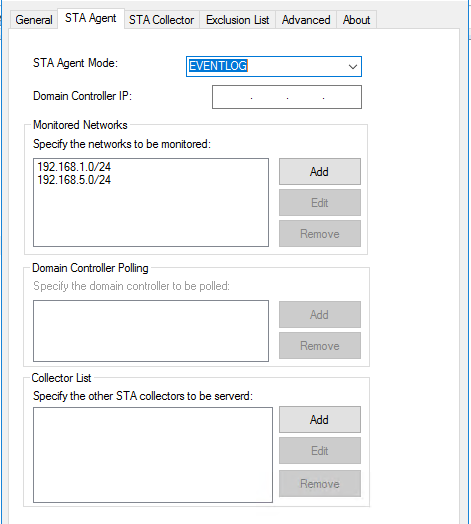
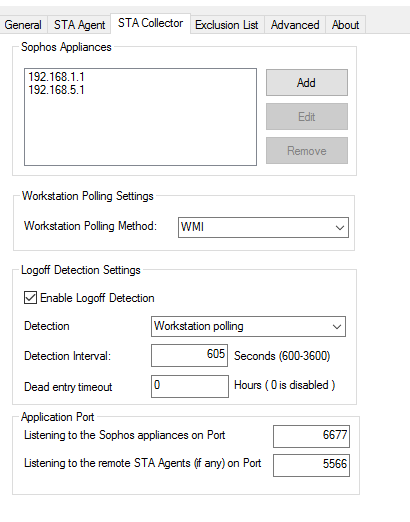
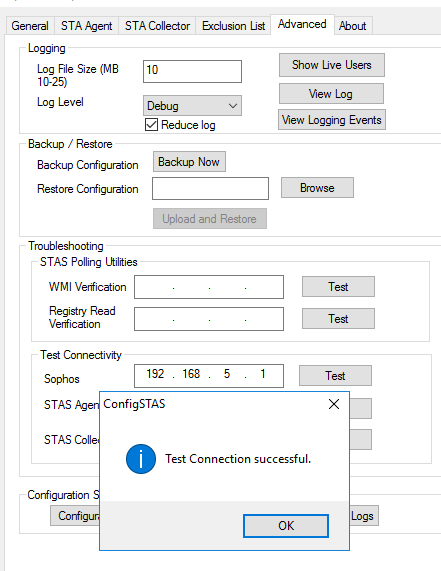
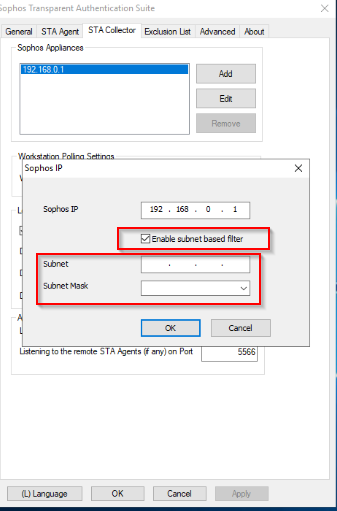
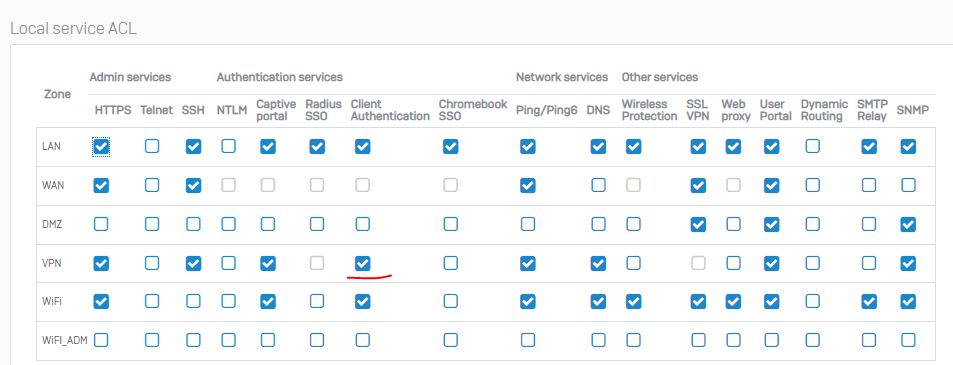
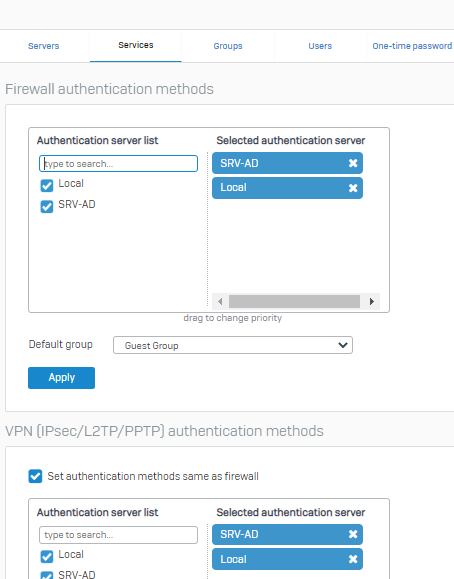
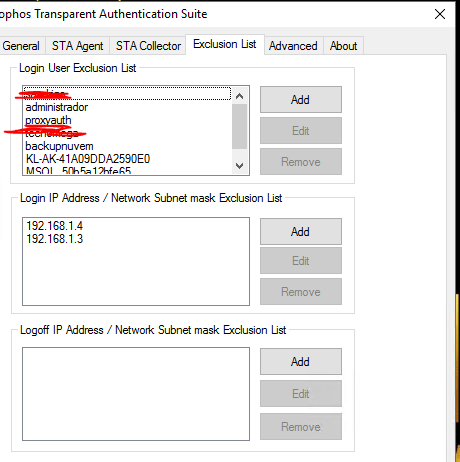
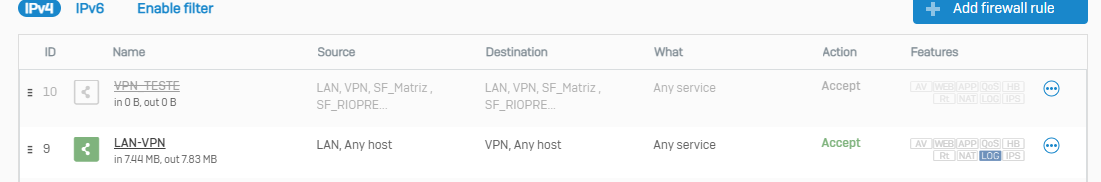
For the Head Office network users, it is everything ok with STAS. I`ve already set up the Servers, Services and STAS tab below like my Head Office Firewall.
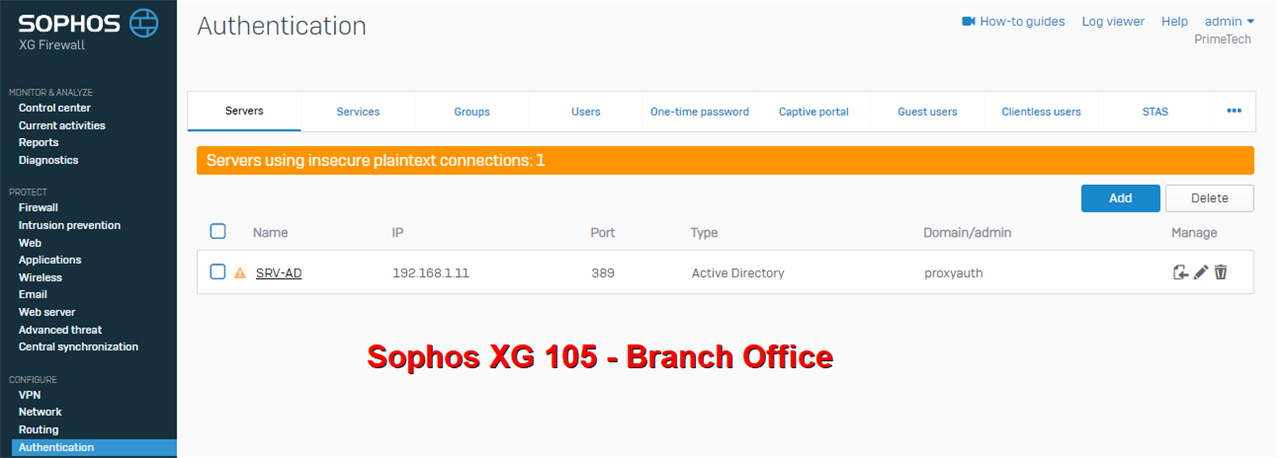
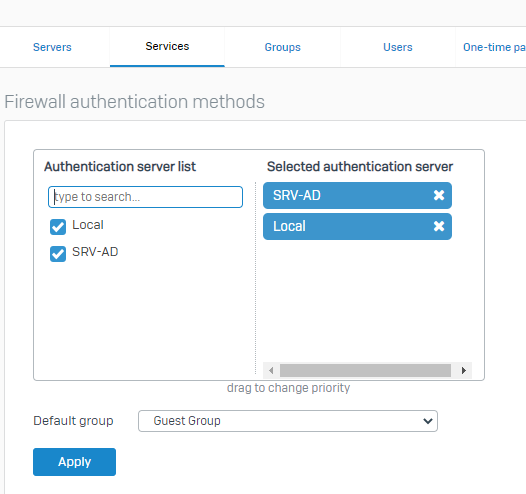
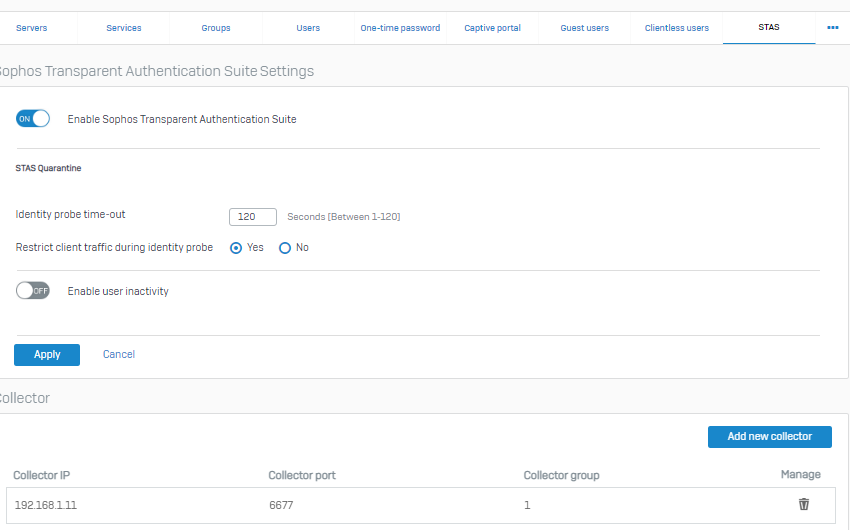
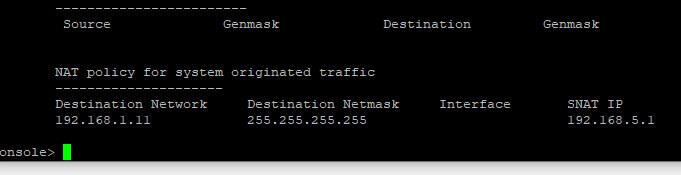
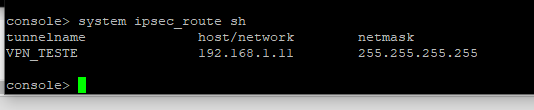
Head Office Sophos Firewall:
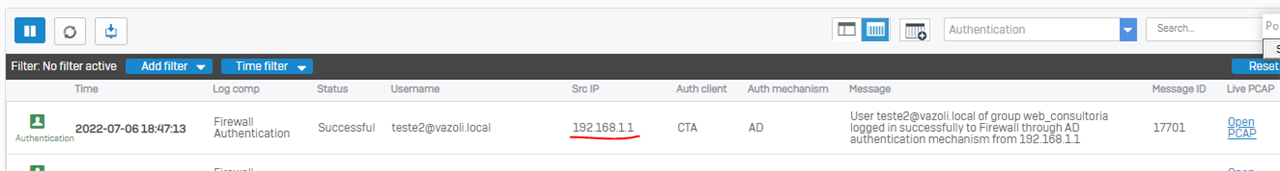
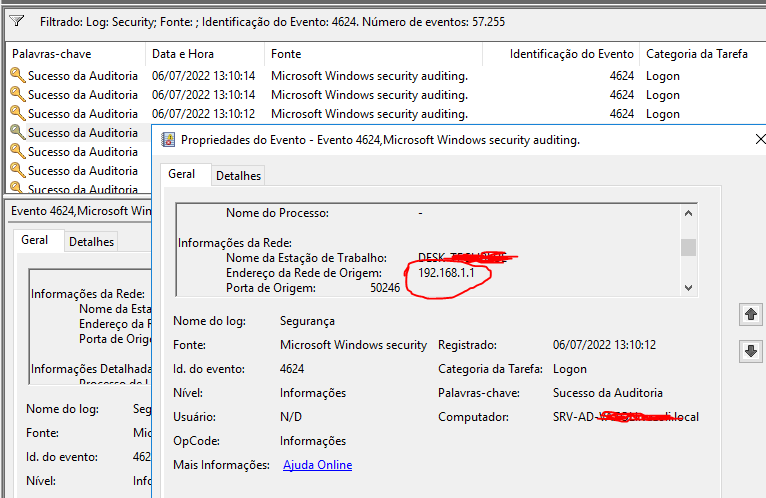
Here it should be 192.168.5.20.
What can I do so Sophos Firewall gets the correct IP 192.168.5.20 from the workstation on Branch Office site?
Thank you guys.
This thread was automatically locked due to age.