Hi
I was wondering if someone can point me in the right direction.
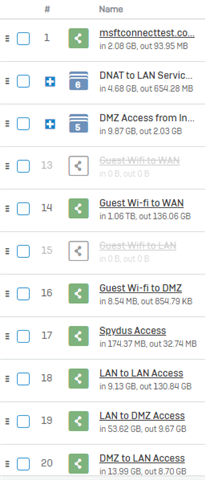
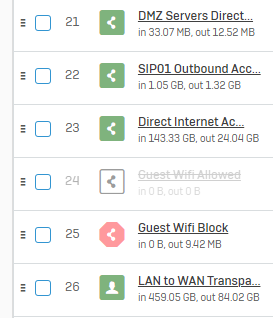
We had recently installed an XG firewall to replace an age Juniper firewall.
In moving to Sophos XG we wanted to get away from our explicit proxy in internet explorer.
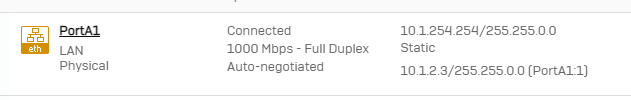
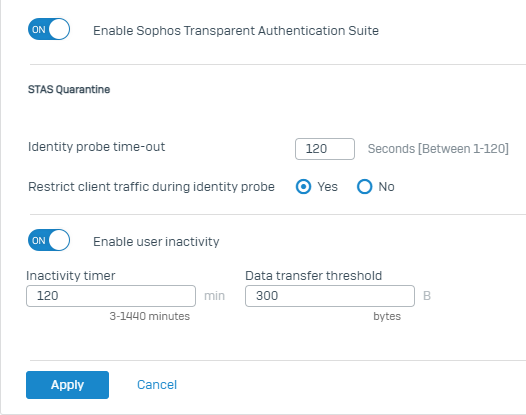
So to gently move us across we added an alias to the interface. We have also setup STAS etc.
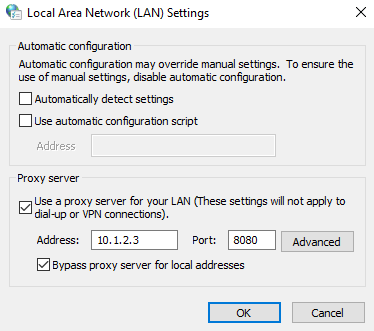
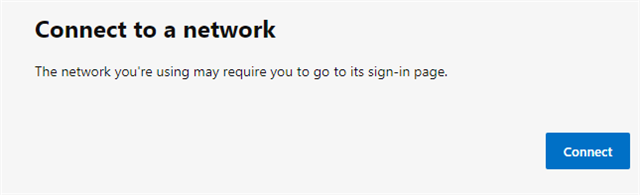
Now everything seems to be working ok at first, however once untick the "use a proxy server for your lan" then I the below.
if i put the proxy back in then it works again,
Does anyone know why this might be?
This thread was automatically locked due to age.