Howdy!
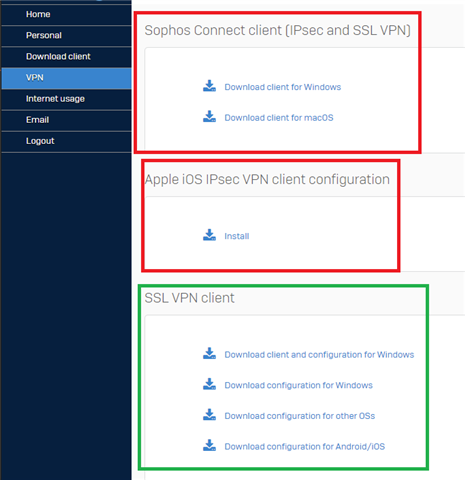
I'm getting used to the operations of my new XG135 firewall. I'm configuring users for IPSEC VPN client access. I can create a user on the firewall. I then navigate to the firewall's User Portal and log in as the user. The User Portal displays a QR that I scan using the Sophos Authenticator on my phone. I then log in to the User Portal as the user this time with the 2FA code appended to the user's password. I land on the User Portal page shown below.
When I try to download either of the Windows or macOS clients, I don't get any kind of executable or installer. Instead, I get a text file called "info.txt" with the following content.
Requested file could not be provided. Make sure Pattern Updates are working correctly. You can find it under 'Backup & Firmware' -> 'Pattern Updates'
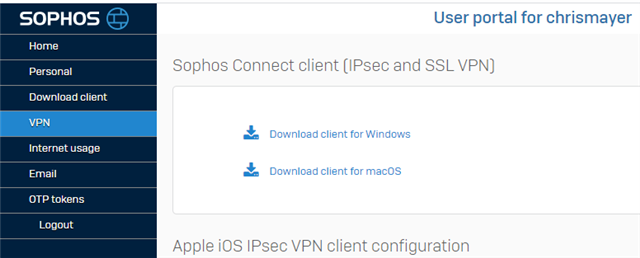
I've checked my firewall's Pattern Updates and the Sophos Connect clients are there and have been updated recently as shown below.

The firewall has the latest firmware (SFOS 18.0.4 MR-4) and all the Pattern Updates look good (populated and have recent timestamps).
I am able to download the Sophos Connect clients while managing the firewall through Sophos Central. This is from the "VPN > IPsec (remote access)" page. When I do this I get a zip file containing the files
- scadmin(legacy).msi
- Sophos Connect_1.4_(IPsec).pkg
- SophosConnect_2.0_(IPsec_and_SSLVPN).msi
I have used the Sophos Connect_1.4_(IPsec).pkg successfuly to install on a Mac. Similarly, SophosConnect_2.0_(IPsec_and_SSLVPN).msi works fine for Windows.
Thanks for your attention to my problem. Let me know if you need more information. I look forward to getting this resolved.
Sincerely,
Chris
This thread was automatically locked due to age.