Hi everyone,
I'm starting to find a few limitations in the Sophos central endpoint web filtering.
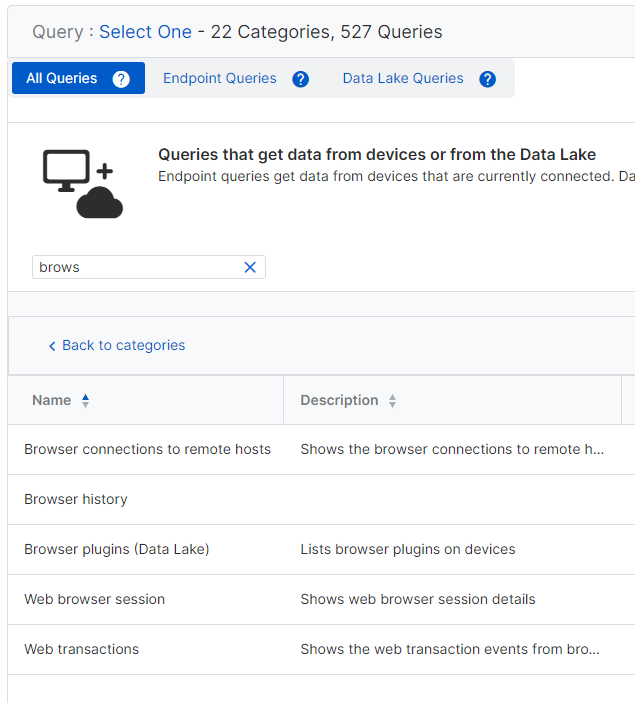
Is there any way to find out if a url is in a particular web category when using sophos central?
Also could sophos central report on all web browsing so I can see which sites users have been accessing most frequently. Or even a report where i can find out if any of our users have accessed a particualr site?
thanks in advance
Richard
Edited tags
[edited by: Gladys at 7:07 AM (GMT -7) on 19 Jun 2023]