I have several customers with hundreds of various computers both Mac and Windows on Endpoint Protection.
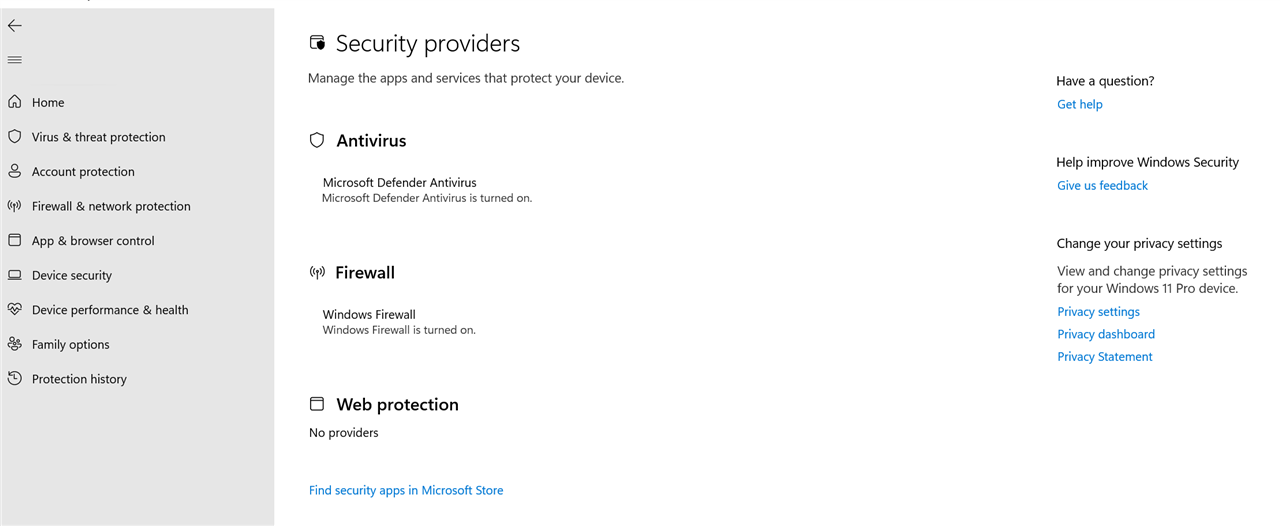
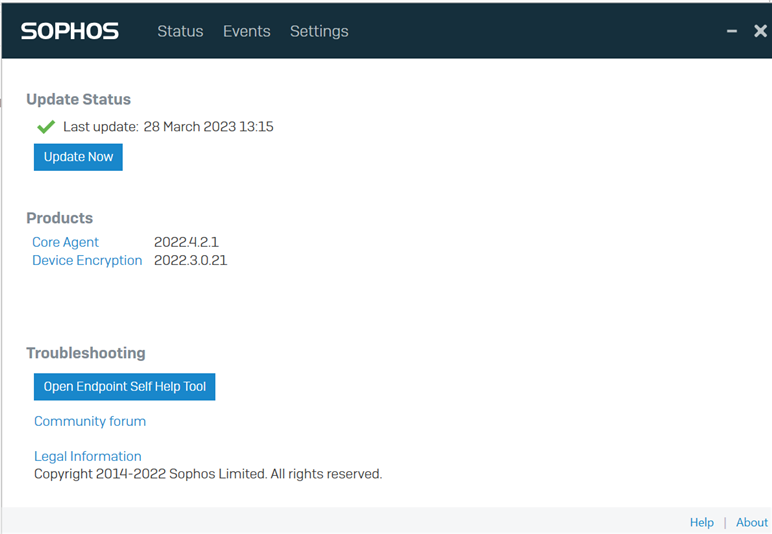
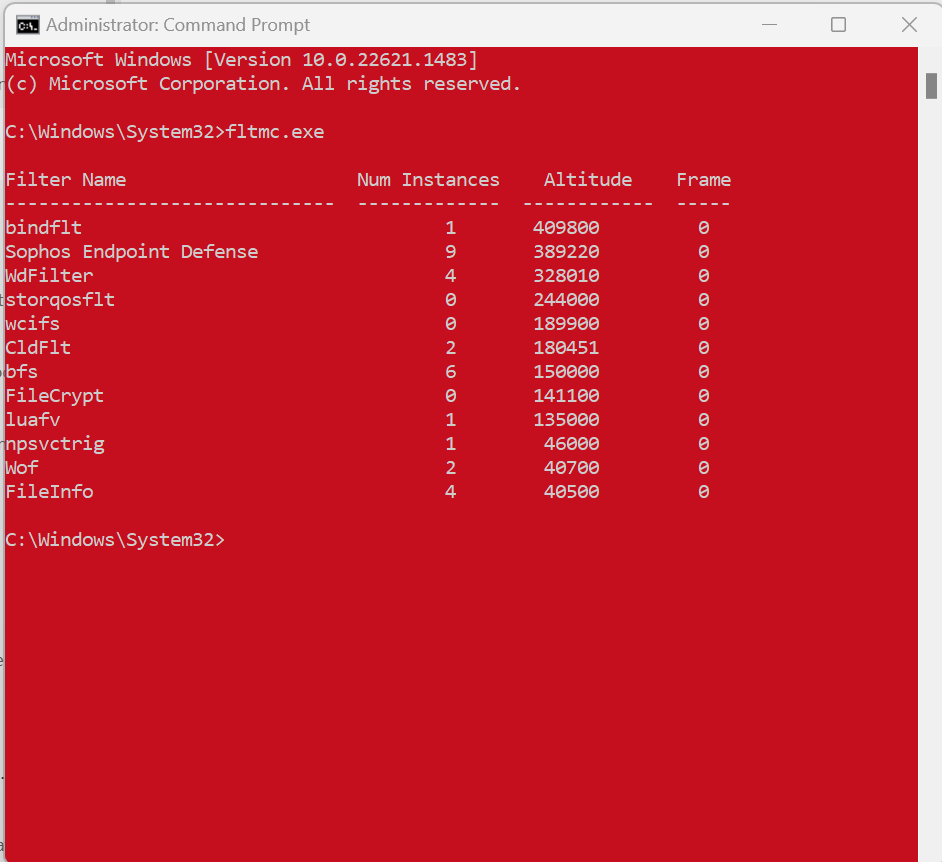
Over the last year i have noticed that the endpoint protection is causing all Windows machines to slow down. Even brand new machines running i7, 32Gb of ram, NVME SSD's and windows 11 become very sluggish to respond to actions once you install the endpoint client, remove the client or disable it and they return to normal. Scheduled scanning is off, using recommended settings for realtime.
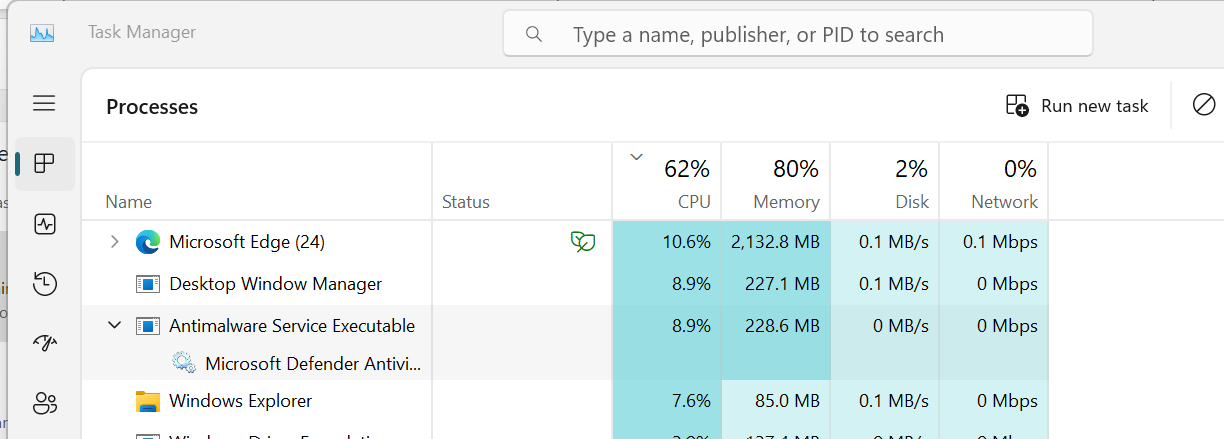
I can see that Sophos is pretty much always utilising the CPU proportionately heavily compared to other processes unless the PC has been idle for a while
This is not a isolated case these are brand new machines from Dell, Lenovo, custom built machines, and also older machines running windows 10 and being rebuilt.
Is there a way to make the client less impactful on performance?
This thread was automatically locked due to age.