For query assistance, please see the following Best Practices guide
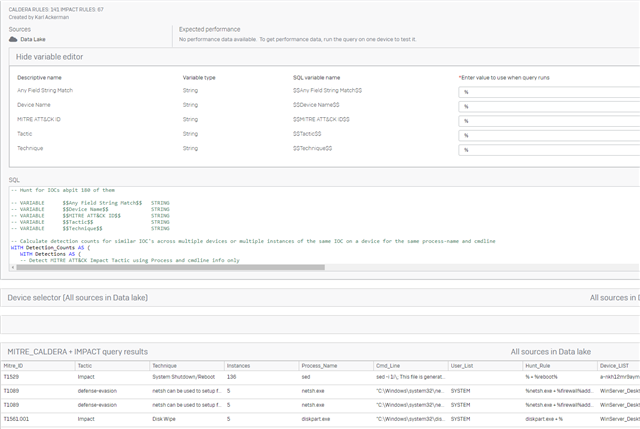
With the data lake we can do some interesting IOC hunts that perform counts across all devices for similar IOC's and with some use of variables we allow for the administrator to rapidly focus on things of interest.
Watch the Video:
Read the details:
For this demonstration query I mapped over the existing CALDERA detection IOCs and a set of IOCs for the IMPACT Tactic on MITRE.
We are currently adding support for a VALUES statement, so without that I had to use another method to build the table of IOC mappings and detection rules. UNION ALL (Ugly I know, but it does the trick).
This query has over 200 detection rules and when run across the entire estate of devices can take some time to run. In my test environment with 10 machines it runs in about 20seconds. In larger deployments it will take longer.
All of these IOC detection rules are based on process and command line analysis. We will be adding other detection rule types that look for registry activity, windows events, and more. For now it is a good test query to run across the data lake.
When we add scheduled reports I expect folks will want to run this type of query nightly to provide a starting point for investigations. As I work on this query I will also add some baselining and FP suppression rules into the query, but for now have FUN.
-- Hunt for IOCs ~200 IOC Rules
-- VARIABLE $$Any Field String Match$$ STRING
-- VARIABLE $$Device Name$$ STRING
-- VARIABLE $$MITRE ATT&CK ID$$ STRING
-- VARIABLE $$Tactic$$ STRING
-- VARIABLE $$Technique$$ STRING
-- Calculate detection counts for similar IOC's across multiple devices or multiple instances of the same IOC on a device for the same process-name and cmdline
WITH Detection_Counts AS (
WITH Detections AS (
-- Detect MITRE ATT&CK Impact Tactic using Process and cmdline info only
WITH Mitre_map (ID,Tactic,Technique,SubTechnique,Mitre_Link,Method,Condition,SubCondition,Refrence) AS (
-- IMPACT DETECTION SET
SELECT 'T1531','Impact','Account Access Removal','','https://attack.mitre.org/techniques/T1531','Process_Cmd','net.exe','%user % %','https://www.windows-commandline.com/change-user-password-in-windows-command-line/'
UNION ALL SELECT 'T1531','Impact','Account Access Removal','','https://attack.mitre.org/techniques/T1531','Process_Cmd','net1.exe','%user % %','https://www.windows-commandline.com/change-user-password-in-windows-command-line/'
UNION ALL SELECT 'T1485','Impact','Data Destruction','''','https://attack.mitre.org/techniques/T1485','Process_Cmd','sdelete.exe','%accepteula%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','sdelete64.exe','%accepteula%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','vssadmin.exe','%delete%shadows%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/vssadmin'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','powershell.exe','%Win32_Shadowcopy%delete%','https://gallery.technet.microsoft.com/scriptcenter/PowerShell-Script-to-ce858ca8'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','wbadmin.exe','%delete%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/wbadmin'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','wbadmin.exe','%disable%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/wbadmin'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','bcdedit.exe','%delete%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/bcdedit'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','bcdedit.exe','%import%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/bcdedit'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','ccleaner.exe','%auto%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','ccleaner.exe','%delete%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','pnputil.exe','%add%rawdisk%','rawdisk can be used to delete files, seeing it added is suspect'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','hdderase.exe','%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','killdisk.exe','%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','eraser.exe','%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','diskwipe.exe','%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1485','Impact','Data Destruction','','https://attack.mitre.org/techniques/T1485','Process_Cmd','diskpart.exe','%clean%','https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete'
UNION ALL SELECT 'T1486','Impact','Data Encrypted for Impact','','https://attack.mitre.org/techniques/T1486','Process_Cmd','enc.exe','%','https://www.carbonblack.com/blog/cb-tau-threat-intelligence-notification-jcry-ransomware-pretends-to-be-adobe-flash-player-update-installer/'
UNION ALL SELECT 'T1486','Impact','Data Encrypted for Impact','','https://attack.mitre.org/techniques/T1486','Process_Cmd','tgytutrc%.exe', '%-i%SM%-tgytutrc%','https://www.carbonblack.com/blog/tau-threat-intelligence-notification-lockergoga-ransomware/'
UNION ALL SELECT 'T1486','Impact','Data Encrypted for Impact','','https://attack.mitre.org/techniques/T1486','Process_Cmd','RobinHood.exe', '%','https://www.carbonblack.com/blog/cb-tau-threat-intelligence-notification-robbinhood-ransomware-stops-181-windows-services-before-encryption/'
UNION ALL SELECT 'T1565.002','Impact','Data Manipulation ','Transmitted Data Manipulation','https://attack.mitre.org/techniques/T1565/002','Process_Cmd','powershell.exe','%get-clipboard%set-clipboard%','https://attack.mitre.org/software/S0455/'
UNION ALL SELECT 'T1491.001','Impact','Defacement ','Internal Defacement','https://attack.mitre.org/techniques/T1491/001','Process_Cmd','powershell.exe','%Remove-Item%\Web\Wallpaper\Windows\%','https://gallery.technet.microsoft.com/scriptcenter/Change-the-Desktop-b5b2141c'
UNION ALL SELECT 'T1491.001','Impact','Defacement ','Internal Defacement','https://attack.mitre.org/techniques/T1491/001','Process_Cmd','powershell.exe','%Set-Wallpaper(Win10).ps1%','https://gallery.technet.microsoft.com/scriptcenter/Change-the-Desktop-b5b2141c'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','powershell.exe','%get-disk%diskpart%format%','Powershell invoking diskpart to format drive'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','powershell.exe','%get-disk%diskpart%clean%','Powershell invoking diskpart to clean drive'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','powershell.exe','%diskpart%format%','https://www.seagate.com/support/kb/how-to-diskpart-eraseclean-a-drive-through-the-command-prompt-005929en/'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','powershell.exe','%diskpart%clean%','https://www.seagate.com/support/kb/how-to-diskpart-eraseclean-a-drive-through-the-command-prompt-005929en/'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','diskpart.exe','%clean%','Powershell collecting disk info' || CHR(10) || 'https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/diskpart'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','diskpart.exe','%format%','Powershell collecting disk info' || CHR(10) || 'https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/diskpart'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','bootsect.exe','%','https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/bootsect-command-line-options'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','bcdedit.exe','%format%','https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/bcdedit-command-line-options'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','bcdboot.exe','%format%','https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/bcdboot-command-line-options-techref-di'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','bootcfg.exe','%delete%','https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/bootcfg'
UNION ALL SELECT 'T1561.001','Impact','Disk Wipe ','Disk Content Wipe','https://attack.mitre.org/techniques/T1561/001','Process_Cmd','diskpart.exe','%','TEST- Detect DISKPART USE' || CHR(10) || 'https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/diskpart'
UNION ALL SELECT 'T1499.004','Impact','Endpoint Denial of Service ','Application or System Exploitation','https://attack.mitre.org/techniques/T1499/004','Win_Crit_Error_Events','','','Critical OR Error Event Detected'
UNION ALL SELECT 'T1495','Impact','Firmware Corruption','','https://attack.mitre.org/techniques/T1495','Process_Cmd','bcdedit.exe','%set%','https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/bcdedit-command-line-options'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','vssadmin.exe','%delete%shadows%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','vssadmin.exe','%resize%shadowstorage%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','wmic.exe','%shadowcopy%delete%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','wbadmin.exe','%delete%catalog%-quiet%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','bcdedit.exe','%set%bootstatuspolicy%ignoreallfailures%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','bcdedit.exe','%recoveryenabled%no%', ''
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%HideBackupEntries%', 'Hide previous versions of files on backup location'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%DisableRemoteRestore%', 'Prevent restoring remote previous versions'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%DisableRemotePage%', 'Hide previous versions list for remote files'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%DisableLocalRestore%', 'Prevent restoring local previous versions'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%DisableLocalPage%', 'Hide previous versions list for local files'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','powershell.exe','%Set-ItemProperty%PreviousVersions%DisableBackupRestore%', 'Prevent restoring previous versions from backups'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%HideBackupEntries%', 'Hide previous versions of files on backup location'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%DisableRemoteRestore%', 'Prevent restoring remote previous versions'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%DisableRemotePage%', 'Hide previous versions list for remote files'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%DisableLocalRestore%', 'Prevent restoring local previous versions'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%DisableLocalPage%', 'Hide previous versions list for local files'
UNION ALL SELECT 'T1490','Impact','Inhibit System Recovery','','https://attack.mitre.org/techniques/T1490','Process_Cmd','reg.exe','%add%PreviousVersions%DisableBackupRestore%', 'Prevent restoring previous versions from backups'
UNION ALL SELECT 'T1489','Impact','Service Stop','','https://attack.mitre.org/techniques/T1489','Process_Cmd','sc.exe','%stop%',''
UNION ALL SELECT 'T1489','Impact','Service Stop','','https://attack.mitre.org/techniques/T1489','Process_Cmd','sc.exe','%config%start%=%disabled%',''
UNION ALL SELECT 'T1489','Impact','Service Stop','','https://attack.mitre.org/techniques/T1489','Process_Cmd','wmic.exe','%service%changeStartmode%Disabled%',''
UNION ALL SELECT 'T1489','Impact','Service Stop','','https://attack.mitre.org/techniques/T1489','Process_Cmd','powershell.exe','%Set-service%StartupType%Disabled%',''
UNION ALL SELECT 'T1489','Impact','Service Stop','','https://attack.mitre.org/techniques/T1489','Process_Cmd','net.exe','%stop%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','%','%shutdown%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','%','%reboot%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','shutdown.exe','%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','at.exe','%shutdown%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','schtasks.exe','%create%shutdown%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','powershell.exe','%stop-computer%',''
UNION ALL SELECT 'T1529','Impact','System Shutdown/Reboot','','https://attack.mitre.org/techniques/T1529','Process_Cmd','powershell.exe','%restart-computer%',''
-- CALDERA DETECTION SET
UNION ALL SELECT 'T1002','exfiltration','Compress staged directory','Data Compressed','https://attack.mitre.org/techniques/T1002','Process_Cmd','%powershell%','%Compress-Archive%','Compress a directory on the file system'
UNION ALL SELECT 'T1003','Process Memory-access','Leverage Procdump','Memory Dump','https://attack.mitre.org/techniques/T1003','Process_Cmd','%powershell%','%procdump%','Dump a processes memory'
UNION ALL SELECT 'T1003','credential-access','GetComputers (Alice','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%powershell%','%Get-NetComputer%','Get a list of all computers in a domain'
UNION ALL SELECT 'T1003','credential-access','Leverage Procdump for lsass memory','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%','%ma lsass.exe%','Dump lsass for later use with mimikatz'
UNION ALL SELECT 'T1003','credential-access','MiniDumpWriteDump (Spooky','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%','%\creds.dmp','Custom GO credential dumper using minidumpwritedump'
UNION ALL SELECT 'T1003','credential-access','Powerkatz (Staged','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%','%DumpCreds%','Use Invoke-Mimikatz'
UNION ALL SELECT 'T1003','credential-access','Credentials in Registry','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%','%reg query HKLM%/f password% /t REG_SZ% ','Search for possible credentials stored in the HKLM Hive'
UNION ALL SELECT 'T1003','credential-access','Credentials in Registry','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%reg.exe','%query HKLM%/f password% /t REG_SZ% ','Search for possible credentials stored in the HKLM Hive'
UNION ALL SELECT 'T1003','credential-access','Run PowerKatz','Credential Dumping','https://attack.mitre.org/techniques/T1003','Process_Cmd','%powershell%','%Invoke-Mimikatz%','Use powerkatz to execute mimikatz and attempt to grab plaintext and/or hashed passwords'
UNION ALL SELECT 'T1005','collection','Find sensitive files','Data from Local System','https://attack.mitre.org/techniques/T1005','Process_Cmd','%powershell%','%Get-ChildItem C:\\Users -Recurse -Include%','Locate files deemed sensitive'
UNION ALL SELECT 'T1007','discovery','Discover system services','System Service Discovery','https://attack.mitre.org/techniques/T1007','Process_Cmd','%powershell%','%Get-Service%','Identify system services'
UNION ALL SELECT 'T1010','discovery','Application Window Discovery','Application Window Discovery','https://attack.mitre.org/techniques/T1010','Process_Cmd','%powershell%','%Get-Process%MainWindowTitle%Shell.Application%','Extracts the names of all open non-explorer windows and the locations of all explorer windows.'
UNION ALL SELECT 'T1012','discovery','Query Registry','Query Registry','https://attack.mitre.org/techniques/T1012','Process_Cmd','%powershell%','%Get-ItemProperty%HKLM:\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion%','Query Registry using PowerShell Get-ItemProperty'
UNION ALL SELECT 'T1016','discovery','Find Domain','System Network Configuration Discovery','https://attack.mitre.org/techniques/T1016','Process_Cmd','%','%nbtstat -n%','Find Domain information'
UNION ALL SELECT 'T1016','discovery','Find Domain','System Network Configuration Discovery','https://attack.mitre.org/techniques/T1016','Process_Cmd','%nbstat.exe','%-n%','Find Domain information'
UNION ALL SELECT 'T1016','discovery','Scan WIFI networks','System Network Configuration Discovery','https://attack.mitre.org/techniques/T1016','Process_Cmd','%powershell%','%wifi.ps1 -Scan%','View all potential WIFI networks on host'
UNION ALL SELECT 'T1016','discovery','Preferred WIFI','System Network Configuration Discovery','https://attack.mitre.org/techniques/T1016','Process_Cmd','%powershell%','%wifi.ps1 -Pref%','See the most used WIFI networks of a machine'
UNION ALL SELECT 'T1016','discovery','Ping network','System Network Configuration Discovery','https://attack.mitre.org/techniques/T1016','Process_Cmd','%','%ping %','Ping the network in order to build the ARP cache'
UNION ALL SELECT 'T1018','discovery','Discover local hosts','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%powershell%','%powerview.ps1%Get-DomainComputer%','Use PowerView to query the Active Directory server for a list of computers in the Domain'
UNION ALL SELECT 'T1018','discovery','Discover domain controller','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%nltest /dclist%','Identify the remote domain controllers'
UNION ALL SELECT 'T1018','discovery','Discover domain controller','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%nltest.exe','%/dclist%','Identify the remote domain controllers'
UNION ALL SELECT 'T1018','discovery','Collect ARP details','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%arp -a%','Locate all active IP and FQDNs on the network'
UNION ALL SELECT 'T1018','discovery','Collect ARP details','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%arp.exe','%-a%','Locate all active IP and FQDNs on the network'
UNION ALL SELECT 'T1018','discovery','Find domain controller','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%nltest /dclist%','Identify remote domain controller'
UNION ALL SELECT 'T1018','discovery','Find domain controller','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%nltest.exe','%/dclist%','Identify remote domain controller'
UNION ALL SELECT 'T1018','discovery','Discover Mail Server','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%nslookup%mail%','Identify the organizations mail server'
UNION ALL SELECT 'T1018','discovery','Discover Mail Server','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%nslookup.exe','%mail%','Identify the organizations mail server'
UNION ALL SELECT 'T1018','discovery','Reverse nslookup IP','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%nslookup #{remote.host.ip}%','Find hostname of remote IP in domain'
UNION ALL SELECT 'T1018','discovery','Reverse nslookup IP','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%nslookup.exe','%remote.host.ip%','Find hostname of remote IP in domain'
UNION ALL SELECT 'T1018','discovery','Find Hostname','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%','%nbtstat -A #{remote.host.ip}%','Find hostname of remote host'
UNION ALL SELECT 'T1018','discovery','Find Hostname','Remote System Discovery','https://attack.mitre.org/techniques/T1018','Process_Cmd','%nbstat.exe','%remote.host.ip%','Find hostname of remote host'
UNION ALL SELECT 'T1031','persistence','Replace a service binary with alternate binary','Modify Existing Service','https://attack.mitre.org/techniques/T1031','Process_Cmd','%powershell%','%Get-Service -Name%Stop-Service%Copy-Item -Path%','A service was detected'
UNION ALL SELECT 'T1033','discovery','GetAdminMembers','System Owner/User Discovery','https://attack.mitre.org/techniques/T1033','Process_Cmd','%powershell%','%Get-NetUser -AdminCount%','Get Administrator users for a computer'
UNION ALL SELECT 'T1033','discovery','Identify active user','System Owner/User Discovery','https://attack.mitre.org/techniques/T1033','Process_Cmd','%','%whoami%','Find user running agent'
UNION ALL SELECT 'T1033','discovery','Identify active user','System Owner/User Discovery','https://attack.mitre.org/techniques/T1033','Process_Cmd','%','%$env:username%','Find user running agent'
UNION ALL SELECT 'T1033','discovery','GetServiceAccounts','System Owner/User Discovery','https://attack.mitre.org/techniques/T1033','Process_Cmd','%powershell%','%Get-NetUser -SPN%','Get Service Accounts for a domain'
UNION ALL SELECT 'T1040','credential-access','Sniff network traffic','Network Sniffing','https://attack.mitre.org/techniques/T1040','Process_Cmd','%powershell%','%New-NetEventSession -Name%-CaptureMode%','Perform a packet capture'
UNION ALL SELECT 'T1041','exfiltration','Exfil staged directory','Exfiltration Over Command and Control Channel','https://attack.mitre.org/techniques/T1041','Process_Cmd','%powershell%','%/file/upload%','Exfil the staged directory'
UNION ALL SELECT 'T1046','discovery','Fingerprint network services','Network Service Scanning','https://attack.mitre.org/techniques/T1046','Process_Cmd','%nmap.exe','%sV -p','Uses nmap to fingerprint services that were network accessible'
UNION ALL SELECT 'T1046','discovery','Fingerprint network services','Network Service Scanning','https://attack.mitre.org/techniques/T1046','Process_Cmd','%','%nmap -sV -p','Uses nmap to fingerprint services that were network accessible'
UNION ALL SELECT 'T1046','discovery','Network Service Scanning','Network Service Scanning','https://attack.mitre.org/techniques/T1046','Process_Cmd','%','%Get-NetIPConfiguration%','Scans the local network for common open ports'
UNION ALL SELECT 'T1047','discovery','Network Service Scanning','Network Service Scanning','https://attack.mitre.org/techniques/T1047','Process_Cmd','%powershell%','%wmic', 'process get executablepath WMIC'
UNION ALL SELECT 'T1047','execution','Remote Execute','Windows Management Instrumentation','https://attack.mitre.org/techniques/T1047','Process_Cmd','%powershell%','wmic /node:%/user:%/password:%process call create%','Remotely execute over WMI'
UNION ALL SELECT 'T1047','execution','Remote Execute','Windows Management Instrumentation','https://attack.mitre.org/techniques/T1047','Process_Cmd','%wmic.exe','%/node%password%process call create%','Remotely executes over WMI'
UNION ALL SELECT 'T1047','collection','WMIC Process Enumeration','WMIC','https://attack.mitre.org/techniques/T1047','Process_Cmd','%wmic.exe','%process get%executablepath%name%processid%parentprocessid%','Capture process id executable path pid and parent pid before writing to disk'
UNION ALL SELECT 'T1047','lateral-movement','Start remote process (WMI)','Windows Management Instrumentation','https://attack.mitre.org/techniques/T1047','Process_Cmd','%wmic.exe','%/node:%/user:%/password%process call create% ','Remotely executes a process over WMI'
UNION ALL SELECT 'T1047','lateral-movement','Start remote process (WMI)','Windows Management Instrumentation','https://attack.mitre.org/techniques/T1047','Process_Cmd','%powershell%','%wmic /node:%/user:%/password%process call create% ','Remotely executes a process over WMI'
UNION ALL SELECT 'T1049','discovery','System Network Connections Discovery','System Network Connections Discovery','https://attack.mitre.org/techniques/T1049','Process_Cmd','%','%netstat -ano%Get-NetTCPConnection%','Enumerates network connections'
UNION ALL SELECT 'T1049','discovery','System Network Connections Discovery','System Network Connections Discovery','https://attack.mitre.org/techniques/T1049','Process_Cmd','%netstat.exe','%-ano%','Enumerates network connections'
UNION ALL SELECT 'T1049','discovery','Find System Network Connections','System Network Connections Discovery','https://attack.mitre.org/techniques/T1049','Process_Cmd','%','%Get-NetTCPConnection%','Find System Network Connections'
UNION ALL SELECT 'T1050','Persistence','Privilege Escalation','New Service','https://attack.mitre.org/techniques/T1050','Process_Cmd','%powershell%','%New-Service%','powershell new service'
UNION ALL SELECT 'T1050','Persistence','Privilege Escalation','New Service','https://attack.mitre.org/techniques/T1050','Process_Cmd','%sc.exe','%create SERVICE%','sc.exe new service'
UNION ALL SELECT 'T1050','Persistence','Privilege Escalation','New Service','https://attack.mitre.org/techniques/T1050','Process_Cmd','%','%sc%create%SERVICE%','cmdline creation of new service'
UNION ALL SELECT 'T1055','defense-evasion','Inject into process','Process Injection','https://attack.mitre.org/techniques/T1055','Process_Cmd','%powershell%','%Invoke-ReflectivePEInjection.ps1%','Injects sandcat DLL into an available process'
UNION ALL SELECT 'T1055','defense-evasion','Signed Binary Execution - odbcconf','Process Injection','https://attack.mitre.org/techniques/T1055','Process_Cmd','%','%odbcconf.exe /S /A%','Leverage odbcconf for DLL injection'
UNION ALL SELECT 'T1055','defense-evasion','Signed Binary Execution - odbcconf','Process Injection','https://attack.mitre.org/techniques/T1055','Process_Cmd','%odbcconf.exe','%/S /A%','Leverage odbcconf for DLL injection'
UNION ALL SELECT 'T1055','defense-evasion','Signed Binary Execution - Mavinject','Process Injection','https://attack.mitre.org/techniques/T1055','Process_Cmd','%powershell%','%nmavinject.exe%','Leverage Mavinject (signed binary) for DLL injection'
UNION ALL SELECT 'T1055','defense-evasion','Signed Binary Execution - Mavinject','Process Injection','https://attack.mitre.org/techniques/T1055','Process_Cmd','%nmavinject.exe','%','Leverage Mavinject (signed binary) for DLL injection'
UNION ALL SELECT 'T1057','discovery','Discover injectable process','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%owner%%get-process%','Discovers processes that the current user has the ability to access and selects an injectable one'
UNION ALL SELECT 'T1057','discovery','Find LSASS','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%get-process%lsass%','Get process info for LSASS'
UNION ALL SELECT 'T1057','discovery','Find user processes','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%owner%user%get-process%','Get process info for processes running as a user'
UNION ALL SELECT 'T1057','discovery','System processes','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%Get-Process%','Identify system processes'
UNION ALL SELECT 'T1057','collection','tasklist Process Enumeration','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%tasklist /m%','Capture running processes and their loaded DLLs'
UNION ALL SELECT 'T1057','collection','tasklist Process Enumeration','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%tasklist.exe','%tasklist /m%','Capture running processes and their loaded DLLs'
UNION ALL SELECT 'T1057','collection','SysInternals PSTool Process Discovery','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%','%pslist.exe%','Process discovery via SysInternals pstool'
UNION ALL SELECT 'T1057','collection','SysInternals PSTool Process Discovery','Process Discovery','https://attack.mitre.org/techniques/T1057','Process_Cmd','%pslist.exe','%','Process discovery via SysInternals pstool'
UNION ALL SELECT 'T1059','execution','Stop PowerShell processes','Command-Line Interface','https://attack.mitre.org/techniques/T1059','Process_Cmd','%powershell%','%Get-Process -Name%powershell%Stop-Process%','Kill all PowerShell processes'
UNION ALL SELECT 'T1059','execution','Deploy downloaded software','Command-Line Interface','https://attack.mitre.org/techniques/T1059','Process_Cmd','%','%server=%%url=%System.Net.WebClient%','Start a new downloaded software'
UNION ALL SELECT 'T1059','execution','Disrupt WIFI','Command-Line Interface','https://attack.mitre.org/techniques/T1059','Process_Cmd','%powershell%','%wifi.ps1 -Off%','Turn a computers WIFI off'
UNION ALL SELECT 'T1063','discovery','Discover antivirus programs','Security Software Discovery','https://attack.mitre.org/techniques/T1063','Process_Cmd','%','%wmic%NAMESPACE%AntiVirusProduct%','Identify AV'
UNION ALL SELECT 'T1063','discovery','Discover antivirus programs','Security Software Discovery','https://attack.mitre.org/techniques/T1063','Process_Cmd','%wmic.exe','%AntiVirusProduct%','Identify AV'
UNION ALL SELECT 'T1063','discovery','Identify Firewalls','Security Software Discovery','https://attack.mitre.org/techniques/T1063','Process_Cmd','%','%SecurityCenter%AntiVirusProduct%','Identify Firewalls'
UNION ALL SELECT 'T1063','discovery','Identify Firewalls','Security Software Discovery','https://attack.mitre.org/techniques/T1063','Process_Cmd','%wmic.exe','%SecurityCenter%AntiVirusProduct%','Identify Firewalls'
UNION ALL SELECT 'T1064','execution','Impersonate user','Scripting','https://attack.mitre.org/techniques/T1064','Process_Cmd','%','%.exe -NoNewWindow -PassThru -Credential%','Run an application as a different user'
UNION ALL SELECT 'T1064','execution','Impersonate user','Scripting','https://attack.mitre.org/techniques/T1064','Process_Cmd','%','%-NoNewWindow -PassThru -Credential%','Run an application as a different user'
UNION ALL SELECT 'T1064','defense-evasion','Bypass ExecutionPolicy','Scripting','https://attack.mitre.org/techniques/T1064','Process_Cmd','%powershell%','%Set-ItemProperty -Path HKLM:\\Software\\Policies\\Microsoft\\Windows\\PowerShell -Name ExecutionPolicy -Value ByPass%','Ensure the ExecutionPolicy is turned to Bypass'
UNION ALL SELECT 'T1069','discovery','Permission Groups Discovery','Permission Groups Discovery','https://attack.mitre.org/techniques/T1069','Process_Cmd','%','%gpresult /R%','Summary of permission and security groups'
UNION ALL SELECT 'T1069','discovery','Permission Groups Discovery','Permission Groups Discovery','https://attack.mitre.org/techniques/T1069','Process_Cmd','%gpresult.exe','%/R%','Summary of permission and security groups'
UNION ALL SELECT 'T1069','discovery','Identify local users','Permission Groups Discovery','https://attack.mitre.org/techniques/T1069','Process_Cmd','%','%Get-WmiObject -Class Win32_UserAccount%','Identify all local users'
UNION ALL SELECT 'T1070','defense-evasion','Clear Logs','Indicator Removal on Host','https://attack.mitre.org/techniques/T1070','Process_Cmd','%powershell%','%Clear-Eventlog%','Clear logs'
UNION ALL SELECT 'T1072','execution','Encoded powershell','Scripting','https://attack.mitre.org/techniques/T1072','Process_Cmd','%','%powershell%-enc%','powershell with encoding'
UNION ALL SELECT 'T1074','collection','Stage sensitive files','Data Staged','https://attack.mitre.org/techniques/T1074','Process_Cmd','%powershell%','%Copy-Item%','copy files to staging directory'
UNION ALL SELECT 'T1074','collection','Create staging directory','Data Staged','https://attack.mitre.org/techniques/T1074','Process_Cmd','%powershell%','%New-Item%-Path%-ItemType%','create a directory for exfil staging'
UNION ALL SELECT 'T1077','lateral-movement','Net use','Windows Admin Shares','https://attack.mitre.org/techniques/T1077','Process_Cmd','%','%net use%/user:\n%','Mounts a network file share on a target computer'
UNION ALL SELECT 'T1077','lateral-movement','Net use','Windows Admin Shares','https://attack.mitre.org/techniques/T1077','Process_Cmd','%net.exe','%use%/user:\n%','Mounts a network file share on a target computer'
UNION ALL SELECT 'T1082','discovery','PowerShell version','System Information Discovery','https://attack.mitre.org/techniques/T1082','Process_Cmd','%','%PSVersionTable%','Discover the PowerShell version'
UNION ALL SELECT 'T1082','discovery','Find OS Version','System Information Discovery','https://attack.mitre.org/techniques/T1082','Process_Cmd','%','%OSVersion.Version%','Find OS Version'
UNION ALL SELECT 'T1083','discovery','File and Directory Discovery','File and Directory Discovery','https://attack.mitre.org/techniques/T1083','Process_Cmd','%powershell%','%Get-ChildItem -Path #{host.system.path}%','Find or discover files on the file system'
UNION ALL SELECT 'T1085','Defense Evasion','Execution','Rundll32','https://attack.mitre.org/techniques/T1085','Process_Cmd','%rundll32.exe','%vnc%server%','rundll32 to launch vncserver'
UNION ALL SELECT 'T1086','execution','Emulate Administrator Tasks','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%Emulate-Administrator-Tasks.ps1%','Emulate administrator tasks on a system in a separate process'
UNION ALL SELECT 'T1086','collection','PowerShell Process Enumeration','PowerShell Collection','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%get-process%ncat%','Capture running processes via PowerShell'
UNION ALL SELECT 'T1086','collection','ncat Enumeration','ncat Collection','https://attack.mitre.org/techniques/T1086','Process_Cmd','%ncat.exe','%get-process%ncat%','Capture running processes via ncat'
UNION ALL SELECT 'T1086','collection','cmd.exe information gathering','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%','%cmd.exe%net user%','User enumeration'
UNION ALL SELECT 'T1086','collection','cmd.exe information gathering','cmd','https://attack.mitre.org/techniques/T1086','Process_Cmd','%cmd.exe','%net user%','User enumeration'
UNION ALL SELECT 'T1086','collection','net.exe information gathering','net','https://attack.mitre.org/techniques/T1086','Process_Cmd','%net.exe','%user%','User enumeration'
UNION ALL SELECT 'T1086','collection','PowerShell information gathering','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%powershell.exe -c%Get-WmiObject -class win32_operatingsystem%','System Information Gathering Script'
UNION ALL SELECT 'T1086','collection','PowerShell information gathering','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%Get-WmiObject -class win32_operatingsystem%','System Information Gathering Script'
UNION ALL SELECT 'T1086','collection','UAC Status','PowerShell Collection','https://attack.mitre.org/techniques/T1086','Process_Cmd','%','%echo $(get-uac)%','Determine whether or not UAC is enabled'
UNION ALL SELECT 'T1086','execution','PowerShell bitly Link Download','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%https://bit.ly%','Download'
UNION ALL SELECT 'T1086','execution','PowerShell Invoke MimiKats','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%mimikatz%','Download'
UNION ALL SELECT 'T1086','defense-evasion','Move Powershell & triage','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%Copy-Item%PowerShell%','Copy powershell to non-standard location and perform triage commands'
UNION ALL SELECT 'T1086','execution','Install PSTools','PowerShell','https://attack.mitre.org/techniques/T1086','Process_Cmd','%powershell%','%New-Item%PSTools%','Download and install PSTools by unzipping the file'
UNION ALL SELECT 'T1087','discovery','Account Discovery (targeted','Account Discovery','https://attack.mitre.org/techniques/T1087','Process_Cmd','%','%net user #{domain.user.name} /domain%','The net utility is executed via cmd to enumerate detailed information about a specific user account.'
UNION ALL SELECT 'T1087','discovery','Account Discovery (targeted','Account Discovery','https://attack.mitre.org/techniques/T1087','Process_Cmd','%net.exe','%user.name%/domain%','The net utility is executed via cmd to enumerate detailed information about a specific user account.'
UNION ALL SELECT 'T1087','discovery','Account Discovery (all','Account Discovery','https://attack.mitre.org/techniques/T1087','Process_Cmd','%','net user /domain','The net utility is executed via cmd to enumerate domain user accounts.'
UNION ALL SELECT 'T1087','discovery','Account Discovery (all','Account Discovery','https://attack.mitre.org/techniques/T1087','Process_Cmd','%net.exe','%user /domain%','The net utility is executed via cmd to enumerate domain user accounts.'
UNION ALL SELECT 'T1088','privilege-escalation','UAC bypass registry','Bypass User Account Control','https://attack.mitre.org/techniques/T1088','Process_Cmd','%powershell%','%New-ItemProperty%%HKLM:Software%EnableLUA%-Value 0%','Set a registry key to allow UAC bypass'
UNION ALL SELECT 'T1088','privilege-escalation','wow64log DLL Hijack','Bypass User Account Control','https://attack.mitre.org/techniques/T1088','Process_Cmd','%','%Akagi64.exe%','using Akagi.exe'
UNION ALL SELECT 'T1088','privilege-escalation','wow64log DLL Hijack','Bypass User Account Control','https://attack.mitre.org/techniques/T1088','Process_Cmd','%akagi64.exe','%','using Akagi.exe'
UNION ALL SELECT 'T1088','privilege-escalation','Bypass UAC Medium','Bypass User Account Control','https://attack.mitre.org/techniques/T1088','Process_Cmd','%','%Bypass-UAC%','Bypass user account controls - medium'
UNION ALL SELECT 'T1089','defense-evasion','Disable Windows Defender Real-Time Protection','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%powershell%','%Set-MPPreference -DisableRealtimeMonitoring 1%','Disable Windows Defender Real-Time Protection'
UNION ALL SELECT 'T1089','defense-evasion','Disable Windows Defender IOAVProtection','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%powershell%','%Set-MpPreference -DisableIntrusionPreventionSystem%Set-MpPreference -DisableIOAVProtection%Set-MpPreference -DisableRealtimeMonitoring%Set-MpPreference -DisableScriptScanning%Set-MpPreference -EnableControlledFolderAccess Disabled%','Disable Windows Defender All'
UNION ALL SELECT 'T1089','defense-evasion','Disable Windows Defender IntrusionPrevention ','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%powershell%','%Set-MpPreference -DisableIntrusionPreventionSystem%','Disable Windows Defender All'
UNION ALL SELECT 'T1089','defense-evasion','Disable Windows Defender Script Scanning','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%powershell%','%Set-MpPreference -DisableScriptScanning%','Disable Windows Defender All'
UNION ALL SELECT 'T1089','defense-evasion','Disable Windows Defender ControledFolderAccess','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%powershell%','%Set-MpPreference -EnableControlledFolderAccess Disabled%','Disable Windows Defender All'
UNION ALL SELECT 'T1089','defense-evasion','netsh can be used to setup fw rules','Disabling Security Tools','https://attack.mitre.org/techniques/T1089','Process_Cmd','%netsh.exe','%firewall%add%rule%','netsh to add firewall rules'
UNION ALL SELECT 'T1090','command-and-control','netsh can be used to setup a proxy tunnel','connection proxy','https://attack.mitre.org/techniques/T1090','Process_Cmd','%netsh.exe','%winhttp%set%proxy%','setup connection proxy'
UNION ALL SELECT 'T1105','command-and-control','Leave note','Remote File Copy','https://attack.mitre.org/techniques/T1105','Process_Cmd','%powershell%','%Set-Content%-Path% -Value%hacked%','Create a text file for the user to find'
UNION ALL SELECT 'T1105','command-and-control','Leave note','Remote File Copy','https://attack.mitre.org/techniques/T1105','Process_Cmd','%powershell%','%Set-Content%-Path% -Value%pay%','Create a text file for the user to find'
UNION ALL SELECT 'T1105','lateral-movement','remote PSession','Remote File Copy','https://attack.mitre.org/techniques/T1105','Process_Cmd','%powershell%','%New-PSSession -ComputerName%','Launch Remote PSession'
UNION ALL SELECT 'T1105','lateral-movement','PSExec','Remote File Copy','https://attack.mitre.org/techniques/T1105','Process_Cmd','%powershell%','%PsExec%.exe%','using PsExec'
UNION ALL SELECT 'T1107','defense-evasion','Avoid logs','File Deletion','https://attack.mitre.org/techniques/T1107','Process_Cmd','%powershell%','%Clear-History;Clear%','Stop terminal from logging history'
UNION ALL SELECT 'T1108','defense-evasion','sleep','Redundant Access','https://attack.mitre.org/techniques/T1108','Process_Cmd','%powershell%','%sleep%','Pause all operations to avoid making noise'
UNION ALL SELECT 'T1113','collection','Screen Capture','Screen Capture','https://attack.mitre.org/techniques/T1113','Process_Cmd','%powershell%','%CopyFromScreen%','capture the contents of the screen'
UNION ALL SELECT 'T1115','collection','Copy Clipboard','Clipboard Data','https://attack.mitre.org/techniques/T1115','Process_Cmd','%powershell%','%Get-Clipboard%','copy the contents for the clipboard and print them'
UNION ALL SELECT 'T1124','discovery','Get System Time','System Time Discovery','https://attack.mitre.org/techniques/T1124','Process_Cmd','%powershell%','%Get-Date -UFormat%','get current system time (ISO 8601)'
UNION ALL SELECT 'T1135','discovery','View admin shares','Network Share Discovery','https://attack.mitre.org/techniques/T1135','Process_Cmd','%powershell%','%Get-SmbShare%','Network Share Discovery'
UNION ALL SELECT 'T1145','credential-access','Find private keys','Private Keys','https://attack.mitre.org/techniques/T1145','Process_Cmd','%powershell%','%.key%','Find private keys on the file system'
UNION ALL SELECT 'T1201','discovery','Password Policy','Password Policy Discovery','https://attack.mitre.org/techniques/T1201','Process_Cmd','%','%net accounts%','Password Policy Discovery'
UNION ALL SELECT 'T1201','discovery','Password Policy','Password Policy Discovery','https://attack.mitre.org/techniques/T1201','Process_Cmd','%net.exe','%accounts%','Password Policy Discovery'
UNION ALL SELECT 'T1214','credential-access','Credentials in Registry','Credentials in Registry','https://attack.mitre.org/techniques/T1214','Process_Cmd','%powershell%','%reg%query%HKCU%password%','Search for possible credentials stored in Registry'
UNION ALL SELECT 'T1214','credential-access','Credentials in Registry','Credentials in Registry','https://attack.mitre.org/techniques/T1214','Process_Cmd','%reg.exe','%query%HKCU%password%','Search for possible credentials stored in Registry'
UNION ALL SELECT 'T1219','Command and Control','AmmyAdmin Command and Control','Remote Access Tools','https://attack.mitre.org/techniques/T1219','Process_Cmd','%Ammyy%Admin.exe','%-connect%','AmmyAdmin can be used for Command and Control'
UNION ALL SELECT 'T1219','Command and Control','TeamViewer C2','Remote Access Tools','https://attack.mitre.org/techniques/T1219','Process_Cmd','%TeamViewer.exe','%assign%','TeamViewer can be used for Command and Control'
UNION ALL SELECT 'T1219','Command and Control','vncserver C2','Remote Access Tools','https://attack.mitre.org/techniques/T1219','Process_Cmd','%vncserver.exe','%-connect%','VNCServer can be used for Command and Control'
UNION ALL SELECT 'T1219','Command and Control','tvnserver C2','Remote Access Tools','https://attack.mitre.org/techniques/T1219','Process_Cmd','%tvnserver.exe','%-connect%','TVNServer can be used for Command and Control'
UNION ALL SELECT 'T1219','Command and Control','vncviewer C2','Remote Access Tools','https://attack.mitre.org/techniques/T1219','Process_Cmd','%vncviewer.exe','%-proxy%','vnc viewer can be used for Command and Control'
UNION ALL SELECT 'T1482','discovery','GetDomain','Domain Trust Discovery','https://attack.mitre.org/techniques/T1482','Process_Cmd','%powershell%','%powerview%Get-NetDomain%','Determine the Windows Domain of a computer'
UNION ALL SELECT 'T1492','impact','move a file to an executable','Stored Data Manipulation','https://attack.mitre.org/techniques/T1492','Process_Cmd','%powershell%','%mv%.%.exe%','move or rename an executable'
UNION ALL SELECT 'T1492','impact','move a file to an executable','Stored Data Manipulation','https://attack.mitre.org/techniques/T1492','Process_Cmd','%copy.exe','%.%.exe%','move or rename an executable'
UNION ALL SELECT 'T1497','discovery','Virtual or Real','Virtualization Sandbox Evasion','https://attack.mitre.org/techniques/T1497','Process_Cmd','%powershell%','%get-wmiobject win32_computersystem | fl model','Determine if the system is virtualized or physical'
UNION ALL SELECT 'T1518','discovery','Internet Explorer Version','Software Discovery','https://attack.mitre.org/techniques/T1518','Process_Cmd','%powershell%','%Get-ItemProperty%Internet Explorer%','Determine the version of Internet Explorer running'
)
--SELECT * FROM Mitre_Map
-- DETECTION BASED ON PROCESS_CMD
SELECT
xdr_data.meta_hostname Device_Name,
xdr_data.meta_os_type Device_Type,
xdr_data.unix_time Date_Time,
map.ID Mitre_ID,
map.Tactic Tactic,
map.Technique Technique,
map.SubTechnique SubTechnique,
map.condition || ' + ' || map.subcondition Hunt_Rule,
map.Mitre_Link,
map.Refrence,
xdr_data.username User_Name,
xdr_data.name Process_Name,
xdr_data.cmdline Cmd_Line,
xdr_data.sophos_PID SophosPID,
xdr_data.path Path_Name
FROM xdr_data
JOIN Mitre_map map ON
LOWER(xdr_data.name) LIKE LOWER(map.condition) AND
LOWER(xdr_data.cmdline) LIKE LOWER(map.SubCondition)
WHERE
LOWER(xdr_data.meta_hostname) LIKE LOWER('%$$Device Name$$%') AND
LOWER(map.Tactic) LIKE LOWER('%$$Tactic$$%') AND
LOWER(map.Technique) LIKE LOWER ('%$$Technique$$%') AND
LOWER(map.ID) LIKE LOWER ('%$$MITRE ATT&CK ID$$%') AND
map.Method = 'Process_Cmd'
)
SELECT
Mitre_ID,
Tactic,
Technique,
COUNT (Device_Name) Instances,
Process_Name,
Cmd_Line,
array_join(array_agg(DISTINCT User_Name), CHR(10)) User_List,
Hunt_Rule,
array_join(array_agg(DISTINCT Device_Name), CHR(10)) Device_LIST,
array_join(array_agg(DISTINCT Device_Type), CHR(10)) Device_Type,
MIN(Date_Time) First_Seen,
MAX(Date_Time) LAST_Seen,
SubTechnique,
array_join(array_agg(DISTINCT SophosPID), CHR(10)) SophosPID_LIST,
array_join(array_agg(DISTINCT Path_Name), CHR(10)) Path_Name_LIST,
MITRE_Link,
Refrence
FROM Detections
GROUP BY Mitre_ID, Tactic, Technique, Process_Name, Cmd_Line, Hunt_Rule, SubTechnique, User_Name, MITRE_Link, Refrence
)
SELECT * FROM Detection_Counts
WHERE LOWER(CAST (Mitre_ID AS VARCHAR) ||
CAST(Tactic AS VARCHAR) ||
CAST(Technique AS VARCHAR) ||
CAST(Instances AS VARCHAR) ||
CAST(Process_Name AS VARCHAR) ||
CAST(Cmd_Line AS VARCHAR) ||
CAST(User_List AS VARCHAR) ||
CAST(Hunt_Rule AS VARCHAR) ||
CAST(Device_List AS VARCHAR) ||
CAST(Device_Type AS VARCHAR) ||
CAST(First_Seen AS VARCHAR) ||
CAST(LAST_Seen AS VARCHAR) ||
CAST(SubTechnique AS VARCHAR) ||
CAST(SophosPID_LIST AS VARCHAR) ||
CAST(Path_Name_LIST AS VARCHAR) ||
CAST(MITRE_Link AS VARCHAR) ||
CAST(Refrence AS VARCHAR)
)
LIKE '%$$Any Field String Match$$%'
ORDER BY Instances DESC
Sample Output
I have attached a video so folks can see how to use the variables to go from searching for everything to perhaps just things of particular interest.
