Disclaimer: This information is provided as-is for the benefit of the Community. Please contact Sophos Professional Services if you require assistance with your specific environment.
Table of Contents
Overview:
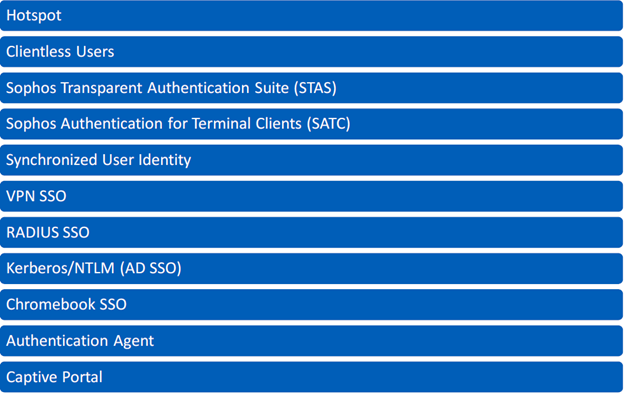
This recommended read provides an overview of supported authentication methods and how to configure them on the Sophos Firewall.
Hotspot
- Hotspot authentication is checked when a hotspot is active on the interface from which traffic is coming. Wireless hotspot authentication is primarily used to provide internet access to guests and restrict unwanted traffic on normal networks.
Clientless Users
- Clientless users don’t authenticate using a username and password but are identified purely by their IP address. Clientless users are always authenticated locally by the Sophos Firewall Firewall. Typically, you would use clientless users to control network access for servers or devices such as printers and VoIP phones. You can also configure people as clientless users, for example, senior executives, for whom you don't want to require a sign-in when they're within the network. If you configure users rather than network devices, we recommend you map the users with static IP addresses on your DHCP server.
- You can create clientless users individually or as a group. You can then edit each user's configuration and specify the policies and bandwidth usage.
- Clientless users appear as live users in current activities. If you deactivate these users, they don't appear as live users.
Single-Sign-On (SSO)
The Sophos Firewall Firewall has several methods for authenticating users for single sign-on:
Sophos Authentication for Terminal Client(STAS)
- The Sophos Transparent Authentication Suite, STAS, is installed on Domain Controllers and reports logon events to the Sophos Firewall.
Sophos Authentication for Terminal/Thin Client (SATC)
- Sophos authentication for Terminal Client, SATC, is installed on Terminal Servers and allows the Sophos Firewall to identify users based on the source port of the traffic from the Terminal Server.
Synchronized User Identity
- Synchronized user ID authentication uses the Security Heartbeat to authenticate endpoint users.
- Synchronized user ID works with Active Directory (AD) configured as an authentication server in Sophos Firewall and is currently supported for Windows 7 and 10. No agents are required on the server or clients, nor does it share or use any password information. The synchronized user ID doesn't work with other directory services or recognize local users. The synchronized user ID shares the domain user account information from the endpoint device the user is signed in to with Sophos Firewall via Security Heartbeat. Sophos Firewall then checks the user account against the configured AD server and activates the user.
- Sophos Endpoint Protection passes Windows sign-in information to Sophos Firewall, which uses this information to authenticate against AD. This authentication triggers user-based policies and general user authentication on the firewall.
VPN SSO
- When users are connected to the Sophos Firewall through a remote access VPN, they’re automatically and seamlessly authenticated with the firewall. Kindly note that in the case of HA failover, users will have to reconnect to the VPN tunnel as they’ll be disconnected, and the user will be logged out of the firewall.
RADIUS SSO
- The Sophos Sophos Firewall Firewall can transparently authenticate users who have already been authenticated on an external RADIUS server. The firewall does not interact with the RADIUS server; it simply monitors the RADIUS accounting records it sends. These records generally include the user’s IP address and user group.
Kerberos/NTLM SSO
- The Sophos Firewall Firewall also supports single sign-on for web traffic using Kerberos/NTLM authentication requests.
Chromebook SSO
- Sophos Firewall provides a Chromebook extension that shares Chromebook user IDs with the Firewall to turn on full user-based policy enforcement and reporting.
Authentication Agent
- The authentication agent client can be downloaded from the User Portal. Once installed, the user can enter their credentials and save them so that it’ll authenticate with the firewall every time they log in.
Web (Captive Portal) Authentication
- Captive Portal is the web-based authentication method where users get an authentication page within the browser.
Revamped
[edited by: Erick Jan at 5:23 AM (GMT -8) on 21 Nov 2024]



