I reviewed this
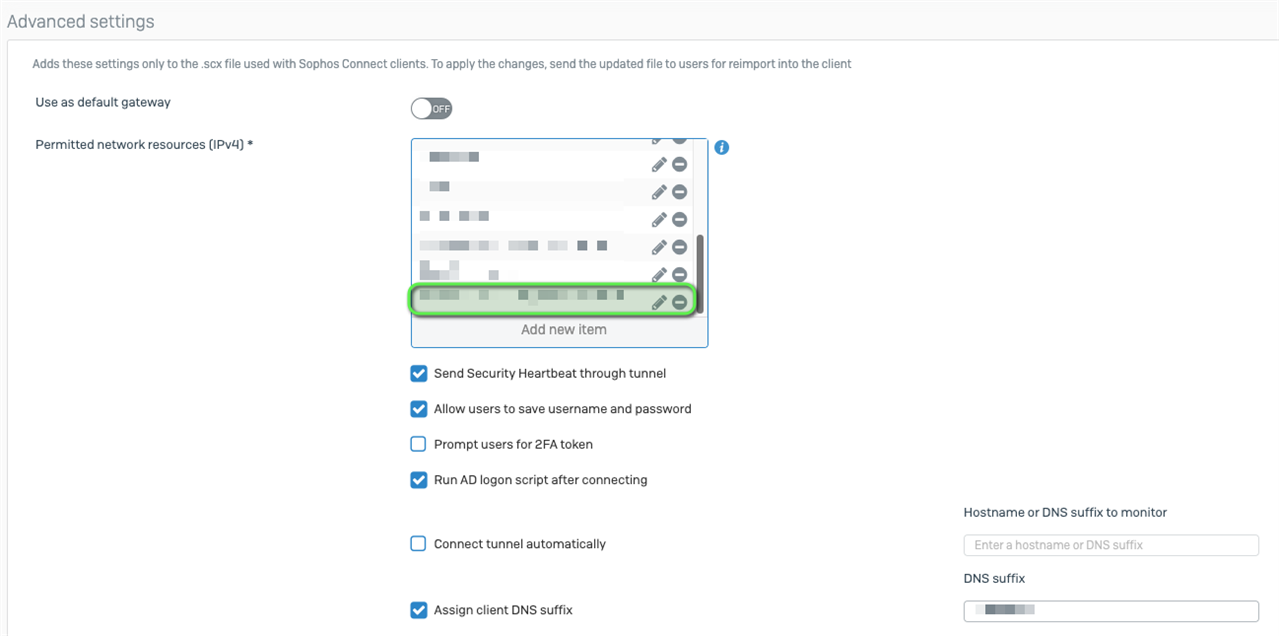
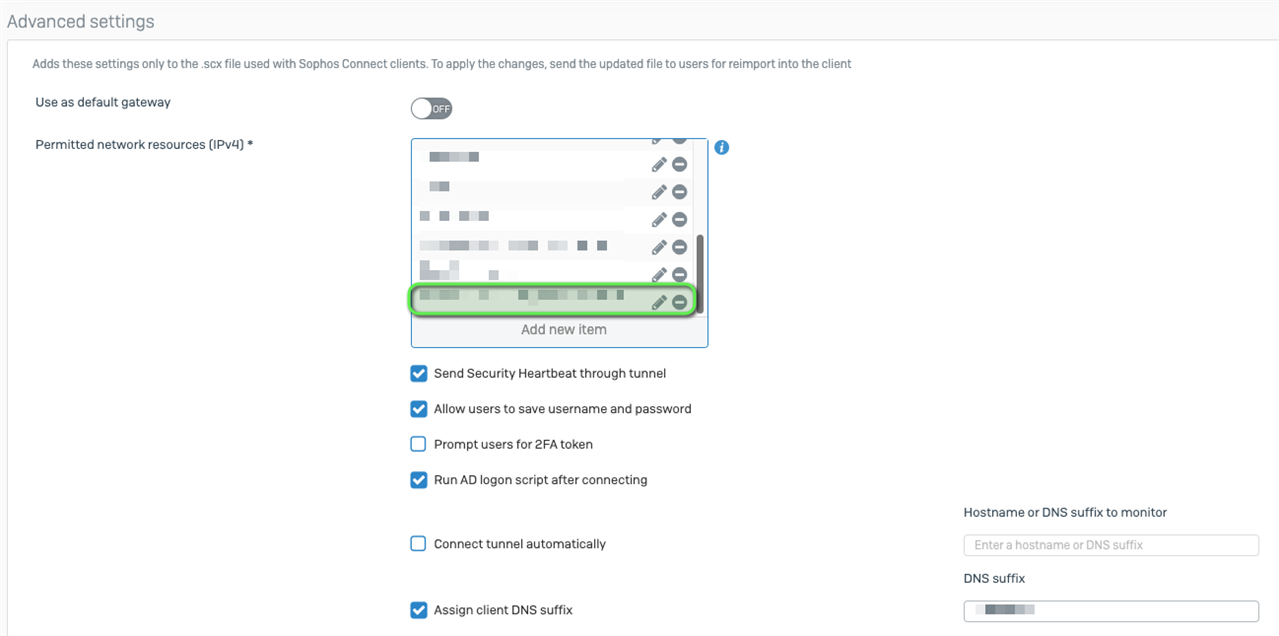
: Force specific websites through VPN tunnel?
This works for SSL VPN. However adding a host IP under IPsec Remote Access does nothing. Also cannot add an FQDN host under IPsec Remote Access under v20.
Is there any way to get this to work on an IPsec VPN or should I submit a feature request?
This thread was automatically locked due to age.