Hi everyone,
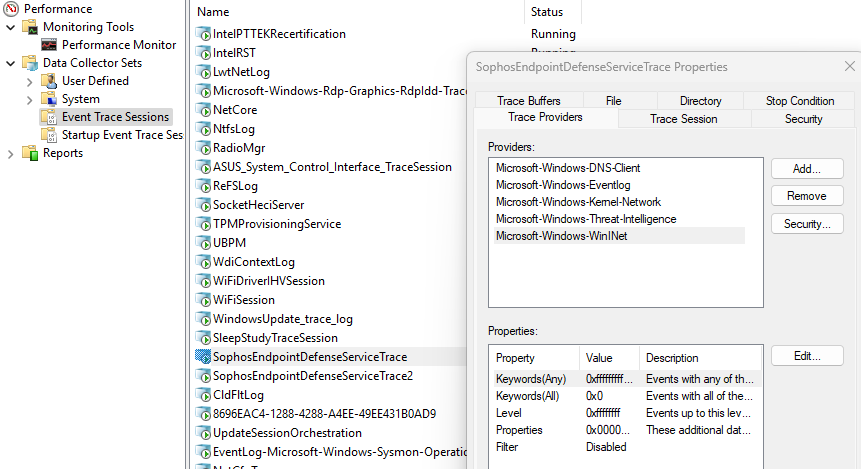
I received a ticket from a user reporting a decrease in the performance of his PC. Checking in task manager I found out that the “Sophos Endpoint Defence Service” is constantly using about 20% of CPU.
Searching for troubleshooting I found out that the “Endpoint Agent” client has not updated in the last month and the button for manually update doesn’t work (the latest updates date back to 03/12/2024 and today that I’m writing this post is 08/01/2025).
After that I tried to uninstall the client witch Sophos Central (everything is working, I have access to the central, the password with this client is working and gave me admin access) but I can’t disable the Tamper Protection because I can’t select the “Override Sophos Central Policy for up to 4 hours to troubleshoot”.
On the central side, except for the “last Sophos Central activity” everything is installed and working fine.
What should I do? Are these two problematics related somehow?
Windows 10 Pro 19045
Core Agent 2024.2.4.1.0
Sophos Intercept X 2024.2.4.1.0
Thank you in advance,
Giorgio