Hi sophos team.
I have an issue with sophos endpoint.
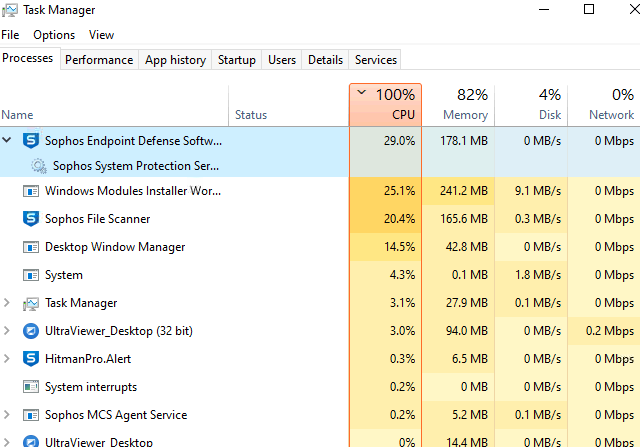
The computer is so lagged when updating windows. Sophos endpoint defense software and sophos file scanner took over 50% cpu, do we have settings to bypass scanning update from window.
The endpoint is the latest version.
This thread was automatically locked due to age.


