The Intercept X Thin Installer for Server is trying to download from api-cloudstation-eu-central-1.prod.hydra.sophos.com and fails due to firewall blocking this request.
api-cloudstation-eu-central-1.prod.hydra.sophos.com resolves to api-spinnaker-2098312200.eu-central-1.elb.amazonaws.com [18.157.100.246]
found it in the installer logs in here:
%ProgramData%\Sophos\CloudInstaller\Logs\
Sending HTTP 'POST' request to: api/download/stage2-details/df6f4312-eda5-43e8-ac02-6207693632ab 2021-11-18T13:50:44.3309692Z INFO : Did not discover an URL for a PAC file 2021-11-18T13:50:44.3309692Z INFO : Attempting to connect using proxy '' of type 'Empty Proxy'. 2021-11-18T13:50:44.3309692Z INFO : Set security protocol: 00000800 2021-11-18T13:50:44.3309692Z INFO : Opening connection to api-cloudstation-eu-central-1.prod.hydra.sophos.com 2021-11-18T13:50:44.3309692Z INFO : Request content size: 31 2021-11-18T13:51:47.4005030Z ERROR : WinHttpSendRequest failed with error 12002 2021-11-18T13:51:47.4005030Z INFO : Failed to connect using proxy '' with error: WinHttpSendRequest failed 2021-11-18T13:51:47.4005030Z INFO : Cleaning up extracted files
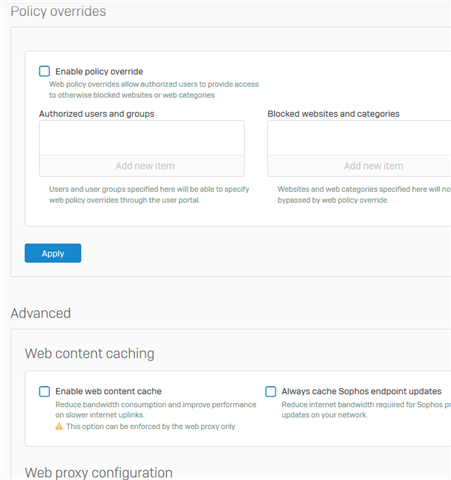
We only allow access to the FQDN allowed here.
https://docs.sophos.com/central/Customer/help/en-us/central/Customer/concepts/DomainsPorts.html
This FQDN is not listed on the KB
For a test I allowed this FQDN and as a result the installer succeeds.
Is this URL request intended for intercept X installer? if yes, could you please update the documentation and explain the new URL?
This thread was automatically locked due to age.