Hi everyone, can some explain what happened here? Is this a false\positive message?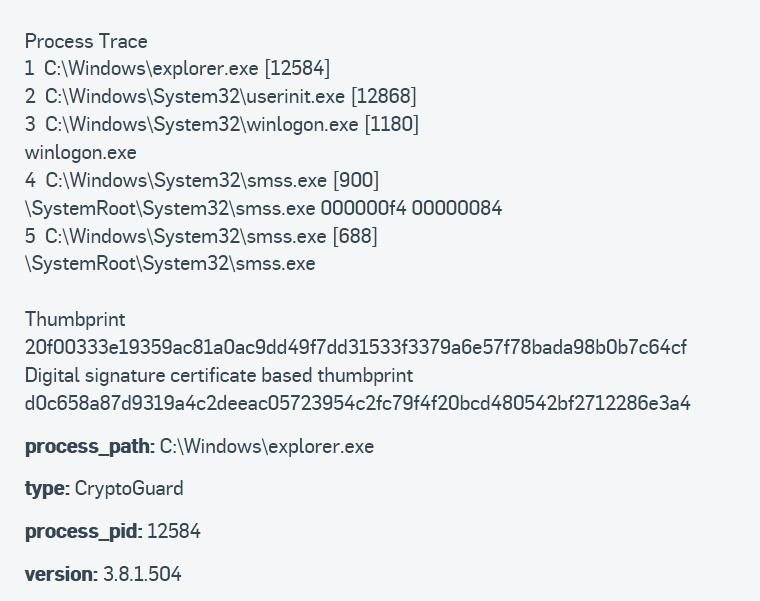
This thread was automatically locked due to age.
Hello pfeffex,
Thank you for reaching out to the Sophos Community.
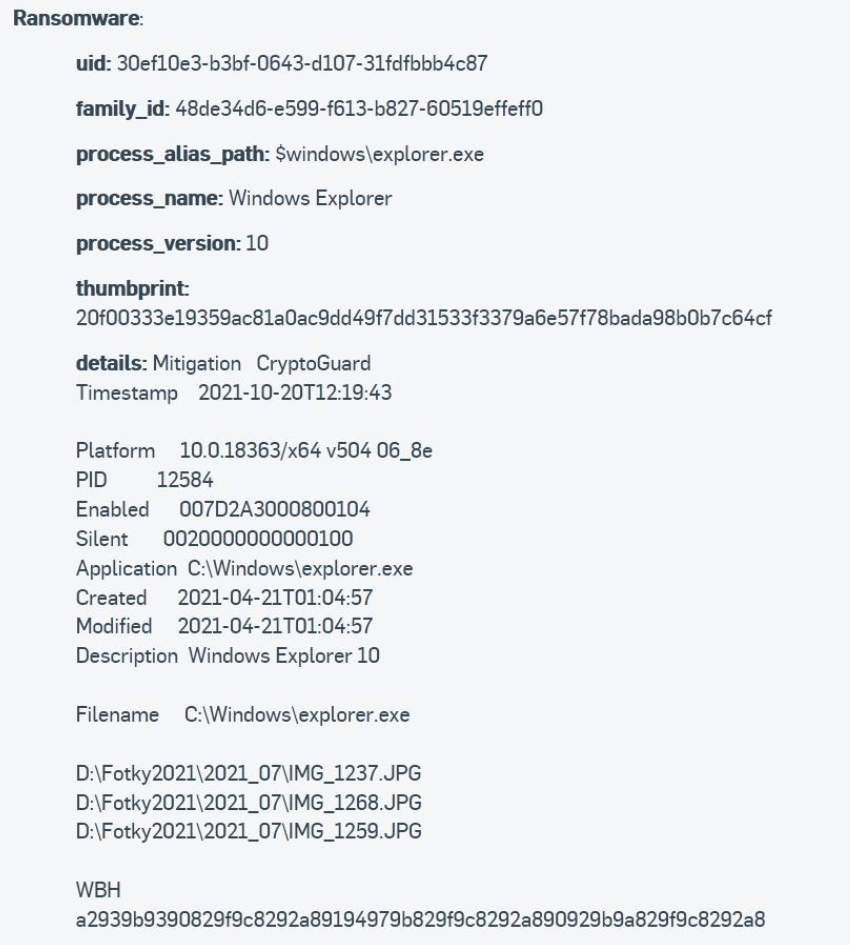
At first glance, this detection does appear to be a false positive. To elaborate, the "WBH" indication in the detection info here stands for "Write Based Header". This means that the file headers were re-written in a way where the resulting file no longer matches the originating file, this is likely why the detection came up.
Do you know if the method used to copy the file is encrypting or modifying the data before transmitting it?

Hello pfeffex,
Thank you for reaching out to the Sophos Community.
At first glance, this detection does appear to be a false positive. To elaborate, the "WBH" indication in the detection info here stands for "Write Based Header". This means that the file headers were re-written in a way where the resulting file no longer matches the originating file, this is likely why the detection came up.
Do you know if the method used to copy the file is encrypting or modifying the data before transmitting it?
