Hi,
I'm looking to turn on the policy isolate devices on red health, but i just want a better understanding of troubleshooting options before i do so.
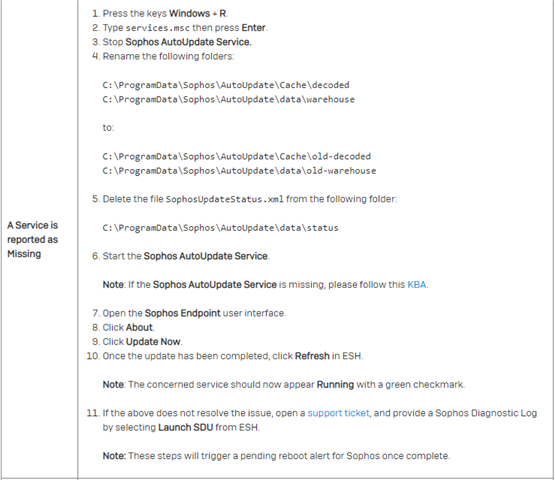
For instance, i have one devices currently on red health as a services is missing.
I've found the below steps to follow, however, i am geographically separated from the device.
So, if the device is isolated, i cannot remote to it, and i can't exactly call a user and give them admin passwords to do this stuff.
What are my options for this kind of incident, and what best practices do fellow technicians follow in cases like this?
Appreciate any answers, thanks
This thread was automatically locked due to age.


