Hi,
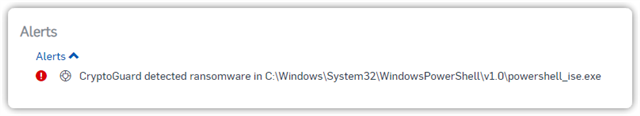
In an attempt to trigger CryptoGuard in a test setting I wrote several test scripts encrypting 50k+ files on disk in suspicious file paths. None of them seem to have triggered Cryptoguard, which makes me wonder if it's triggered solely on known IOC's. My first thought was that the number of I/O operations would have been enough to trigger an alarm, but it didn't. Is there something to be said about the detection that could help me trigger an alarm?
This thread was automatically locked due to age.