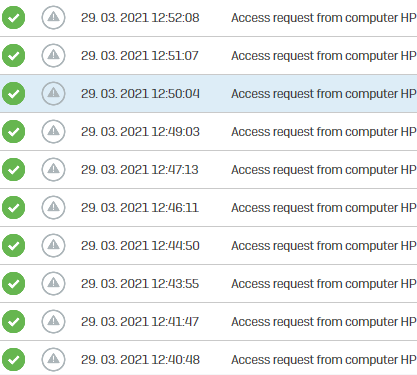
In our company we have three HP Elitebook Dragonfly notebooks, and only those three are causing trouble with "unsafe" computers. I hoped that uninstallig HP Sure * (couple of programs) would help me prevent that, but sadly that's not the case. Do you have any other idea which software, by default installed on the HP computer or actually any other thing/setting could cause the error?
Thank you for your time and kind regards!
This thread was automatically locked due to age.