HI,
Intercept X has removed a file. I whant to send it to Sophos Labs for analyzing. Where can I find it ? I do not whant to release it to get hold of it ;-)
This thread was automatically locked due to age.
HI,
Intercept X has removed a file. I whant to send it to Sophos Labs for analyzing. Where can I find it ? I do not whant to release it to get hold of it ;-)
Hi,
When an item is detected, a Sophos internal utility called Sophos Clean is used to cleanup the item. Customers using Sophos Central have the ability to restore files after they have been cleaned up. This feature is designed to allow the restoration of files and their associated permissions, registry keys e.t.c. after they have been incorrectly detected as malware and removed. BUT not all detected files will have an option to be restored, it is predominantly Portable Executable (PE) files that can be restored, this includes for example .exe, .dll and .sys files, whereas documents and scripts like .doc, .xls and .js aren't able to be restored.
To restore a file after a detection, please do the following:
Please give feedback if this helped you out!
Best Regards
Intrusus
Sophos Certified Engineer | Sophos Certified Technician
private lab:
XG firewall with SFOS 20.X running on Proxmox
If a post solves your question use the 'Verify Answer' link
Hi,
yes, I know how to release files, but the big question is, if it is safe to release a file. How am I supposed to know if file is false positive without having the chance to send it to Sophos Labs for example. On the other hand in my case it is an inf file. So what you are saying is, that sophos clean is removing it and it is gone for good? What if theis was an false positive? Bad luck?
Sorry, then I misunderstood you
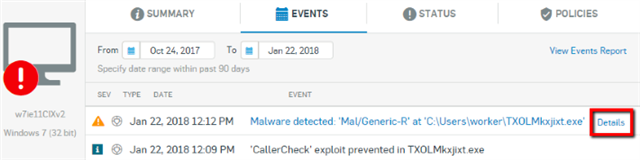
In these circumstances, Sophos suggests using the files SHA-256 hash. For Sophos Central customers, locating the SHA-256 hash of a detected or suspicious file is normally easy, for details on how to do this please see Sophos Central: How to locate a files unique SHA-256 hash. Then put this Hash into VirusTotal to check if other vendors have registered it as malware.
If the hash is unknown, we have here an official way when a file gets detected by central managed endpoints: If the target file has been detected by the endpoint and put into SafeStore you will need to contact Technical Support for them to process the extraction and submission. I know this can take some time, but it's the safest and only official way at the moment.
Cheers
Intrusus
Sophos Certified Engineer | Sophos Certified Technician
private lab:
XG firewall with SFOS 20.X running on Proxmox
If a post solves your question use the 'Verify Answer' link
Sorry, then I misunderstood you
In these circumstances, Sophos suggests using the files SHA-256 hash. For Sophos Central customers, locating the SHA-256 hash of a detected or suspicious file is normally easy, for details on how to do this please see Sophos Central: How to locate a files unique SHA-256 hash. Then put this Hash into VirusTotal to check if other vendors have registered it as malware.
If the hash is unknown, we have here an official way when a file gets detected by central managed endpoints: If the target file has been detected by the endpoint and put into SafeStore you will need to contact Technical Support for them to process the extraction and submission. I know this can take some time, but it's the safest and only official way at the moment.
Cheers
Intrusus
Sophos Certified Engineer | Sophos Certified Technician
private lab:
XG firewall with SFOS 20.X running on Proxmox
If a post solves your question use the 'Verify Answer' link