Hi.
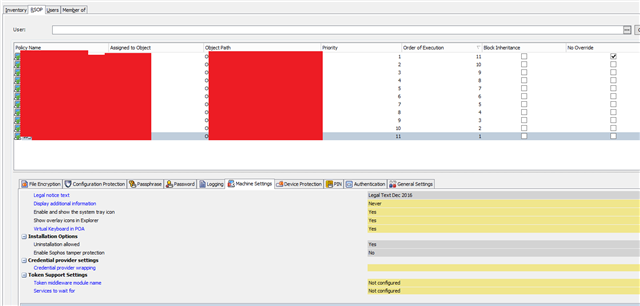
I have a few users lately where Safeguard is saying that their username and password is incorrect. However when I try their password I get the same thing. I can get them logged back and sync'd the safeguard server and they can login back in, but every now and again it locks them out again. Active Directory accounts are not locked.
Some of the trouble shooting I have done is:
1: Checked the last key received, last certificate received and last server contacts are all the same
2: Checked the users status which should sgn user (owner)
3: Removed and re-added the certificate and sycn'd with the safeguard server. The key, cert and server contact all match up fine, user is the owner.
4: Removed the cert from the management console and got the user to add their password when they are prompted. This does not work either.
I'm suspecting that the newer windows version are having a problems. Some of the users are on 2004
The version of safeguard that is being used is 8.0.
Any assistance would be great.
Thanks,
Rob.
This thread was automatically locked due to age.