First alert we had from rule SID 20842 was on 23 Nov at 17:39 GMT. Since then have had 230 alerts to around 50 different Windows 10 hosts, all this rule, 29 different IP source addresses, all source port 80, various destination ports.
Looking up the source IP addresses most of them look like CDN IPs, some identified as Akamai Technologies, couple I've seen Microsoft update mentioned. Looking at netstat on one host it looked like SearchApp.exe was connected to one of these sources. I checked the SearchApp.exe program certificate and it was genuine.
I just can't understand why this rule is suddenly generating these alerts. If the IPs are genuine CDN sources, why they are generating alerts? I'm not aware of any network or firewall changes that could be a factor.
I've logged a ticket with support, but haven't heard anything back and am desperate to understand what is going on here.
- Are these false positives or do we have malware on the network?
- If they are false positives why can't I find anything about this particular rule?
- Do people routinely disable IPS rules that generate false positives, or whitelist lots of domains after checking they are legit?
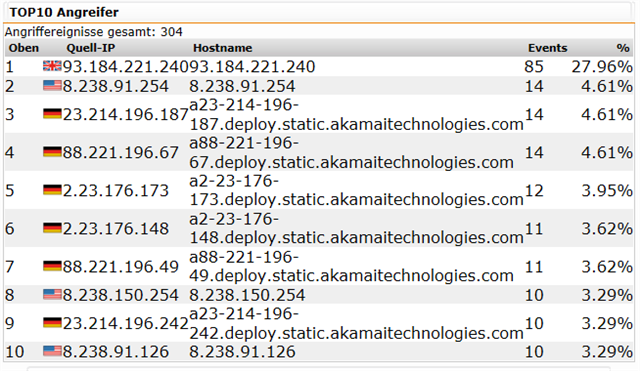
Top 10 IPS sources since first alert (all rule 20842):
|
1
|
23.73.136.145
|
66
|
||||||
|
2
|
23.73.136.89
|
52
|
||||||
|
3
|
13.107.4.50
|
28
|
||||||
|
4
|
178.79.251.0
|
12
|
||||||
|
5
|
8.238.11.126
|
7
|
||||||
|
6
|
2.22.146.145
|
6
|
||||||
|
7
|
8.238.5.126
|
5
|
||||||
|
8
|
8.238.3.254
|
5
|
||||||
|
9
|
2.22.146.144
|
4
|
||||||
|
10
|
8.238.55.126
|
4
|
Full email alert:
Intrusion Prevention Alert
An intrusion has been detected. The packet has been dropped automatically.
You can toggle this rule between "drop" and "alert only" in WebAdmin.
Details about the intrusion alert:
Message........: FILE-OTHER Interactive Data eSignal stack buffer overflow attempt
Details........: https://www.snort.org/search?query=20842
Time...........: 2021-11-23 17:39:17
Packet dropped.: yes
Priority.......: high
Classification.: Attempted User Privilege Gain
IP protocol....: 6 (TCP)
Source IP address: 13.107.4.50
Source port: 80 (http)
Destination IP address: 192.168.[x].[x]
Destination port: 58759
---
- Model: SG310
- Firmware: 9.707-5
- Pattern: 205149
Any help would be very much appreciated.
This thread was automatically locked due to age.