Case:
Client with Sophos Endpoint does DNS Request to XGS as resolver
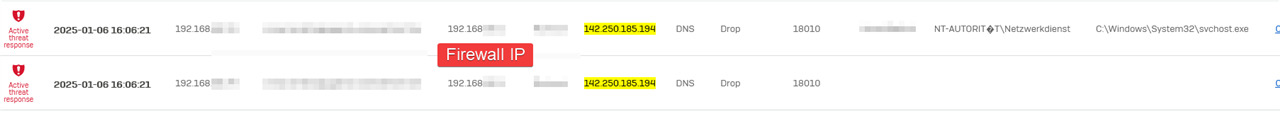
DNS Response IP is seen in a 3rd Party Threat Feed
Firewall generated ATP Alert and sends red Heartbeat to Sophos Central
The Client is isolated by Sophos Central.
Now, how can I find out which hostname the client requested in DNS request? The IP is from a huge Google IP List.
The firewall is not logging DNS requests unfortunately.
Datalake Query was not bringing expected results.
XDR queries could help. Generally speaking, it is hard to find this, as we "cannot" store DNS queries on a firewall due the amount of queries, the clients will generate.
You could try to find a matching DNS packet at the "exact same time" but even this will not help you.
This issue came up in the past years with UTM ATP as well.
Can you see via mouse over more information about this DNS drop?
__________________________________________________________________________________________________________________
I spent some time with the XDR Queries, could find a lot of browser related connections but no DNS requests.
2025-01-07 11:11:12 Active threat response messageid="18009" log_type="ATP" log_component="DNS" log_subtype="Alert" user="username" protocol="UDP" src_port="52472" dst_port="53" src_ip="xxx.xxx.xxx.xxx" dst_ip="Firewall-LAN-IP" url="143.204.98.125" threat="Blocklistname" threatfeed="Blocklistname" event_id="" type="Standard" host_login_user="" host_process_user="" endpoint_id="" execution_path=""
What DNS server do you use on SFOS? Not by any chance Secure DNS by Central?
__________________________________________________________________________________________________________________
No it's not Sophos DNS currently. In that case the firewall of the remote location uses Google DNS.