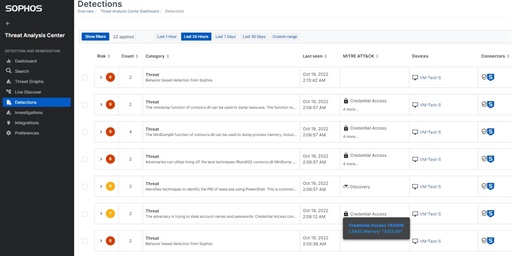
For those participating in the XDR Features Early Access Program (EAP) and utilizing our Threat Analysis Center's Search capability, we have an exciting announcement. We are currently in the process updating the user interface in preparation to broad...