I'm using a Sophos Central defined SD-Wan Connection Group and a series of rules to allow connection between sites. As best I can tell all the rules are working for all other workloads. The only place I'm aware that these rules are not working properly is when trying to backup my switches to a TFTP server located in another site. None of my rules are really fine grained enough to limit access to a service. If a host can reach another host, it has should be able to do so for any service. I have no specific rules setup on the Site A location to alternatively route this kind of traffic.
For the case at hand I have Site A (where TFTP server is) and Site B (where the switch is)
When I attempt to upload the switch's settings to the TFTP server I can see the connection being made from the switch to the TFTP server but when the TFTP server attempts to respond the firewall in Site A is sending the response "out the WAN" interface instead of into the XFRM interface that the connection came in.
From the TFTP server I can PING and SSH into the switch I'm testing with.
I've opened a support case and so far they've not been able to provide any guidance.
This is reproducible.
Site A is a SFV4C6 (SFOS 19.0.0 GA-Build317)
Site B is a XGS2300 (SFOS 19.0.0 GA-Build317)
This also affects another site running the same firmware but is an XGS 126
Can you check the packet capture of this traffic? Because it could be, the FTP helper is hitting. And the FTP Helper hitting means, it is sys-gen traffic.
Try to disable FTP scanning in your firewall rule as well.
__________________________________________________________________________________________________________________
LuCar Toni Thanks for responding. Could you expand on the FTP helper? I mentioned this to the technician I am working with during our last call and he wasn't familiar with it. Regarding the FTP scanning if you're meaning "Scan FTP for Malware" under the Security Features > Web Filtering. That's not enabled. (don't currently have any option selected in that section for the rule that it's hitting).
I apologize for stating something that may be obvious I'm trying to use TFTP not FTP.
Here's what the PCAP from the Site A firewall shows if that tells you anything.
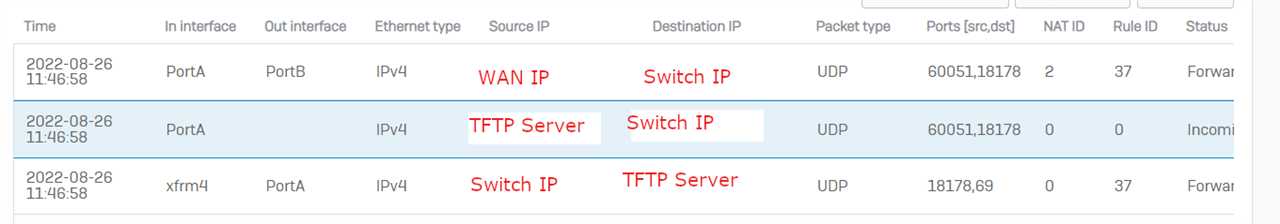
Rule 37 is a VPN > LAN rule and is basically Source "any of our fixed site VPN subnets" Destination "any Site A LAN resources"
There is no linked NAT rule on 37. NAT ID 2 is the Default out of the box "Default SNAT IPv4" rule. "Any Host to Any Host" Masq the source and outbound to Port B.
Just wondering. The Switch IP, does a route back exists? Likely because you told us, other services are working too?
__________________________________________________________________________________________________________________
My emailed response didn't come through, but yes, because I can ping and SSH along the route back without issue.
Hi John,
This sounds like an issue we fixed in v19.0 MR1, can you try upgrading to it to see if it resolves the issue for you?
community.sophos.com/.../sophos-firewall-v19-mr1-re_2d00_release-build-365-is-now-available
bobbylam Could you confirm which issue you believe this aligns with. I'm willing to wait for the mr1 re-release to make it to us to address the problem if we can confirm that it does.
Haven't had a chance to validate it but NC-86652 does sound like our issue. Thanks for pointing me to that. We've had enough growing pains over our implementation that I'll let MR1 release reach us through the "Available to All phase".
Just confirming that MR1 did resolve the TFTP upload issue we saw.