Hi everyone,
I am setting up a separate thread as I did not receive any specific reply in other threads.
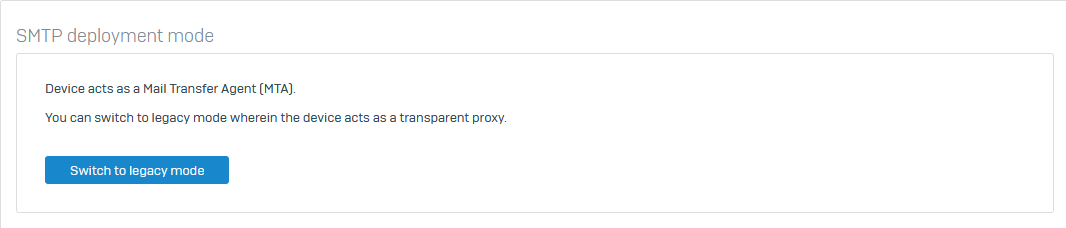
The case concerns Sophos Anti-Spam Interface after upgrading from v18.5MR2 to v18.5MR3 and from v19EAP1 to v19EAP2.
Before updating, antispam works great in legacy mode, detects a lot of intrusive messages and tags with a prefix (near 99%). After updating, only some messages are detected as spam and tagged (I did not do any changes in configuration).
What it comes from? How can I edit my lists to achieve pre-update spam detection?
Greetings
This thread was automatically locked due to age.