Disclaimer: This information is provided as-is for the benefit of the Community. Please contact Sophos Professional Services if you require assistance with your specific environment.
Table of Contents
Overview
With the SFOS v19 update up to v21, there are some significant changes concerning the configuration of selecting a gateway. These changes are quite different than what we had in previous versions, i.e. SFOS v17 & SFOS v18, which you can refer to here: https://community.sophos.com/sophos-xg-firewall/f/recommended-reads/118888/sophos-xg-firewall-v18-how-to-choose-the-gateway-for-a-firewall-rule
Traditional Settings For Primary and Backup Gateway:
Step 1: For the part mentioned in the screenshot, we’ll specify the name of the firewall rule and other details regarding rule grouping and Action. Then, we specify the Source zones, Source networks, and devices, during the Scheduled time, Destination zones, Destination networks, and Services. Please click the help button if you are unsure what each option means.
Path: Rules and Policies > Firewall rules > Add firewall rule > New firewall rule: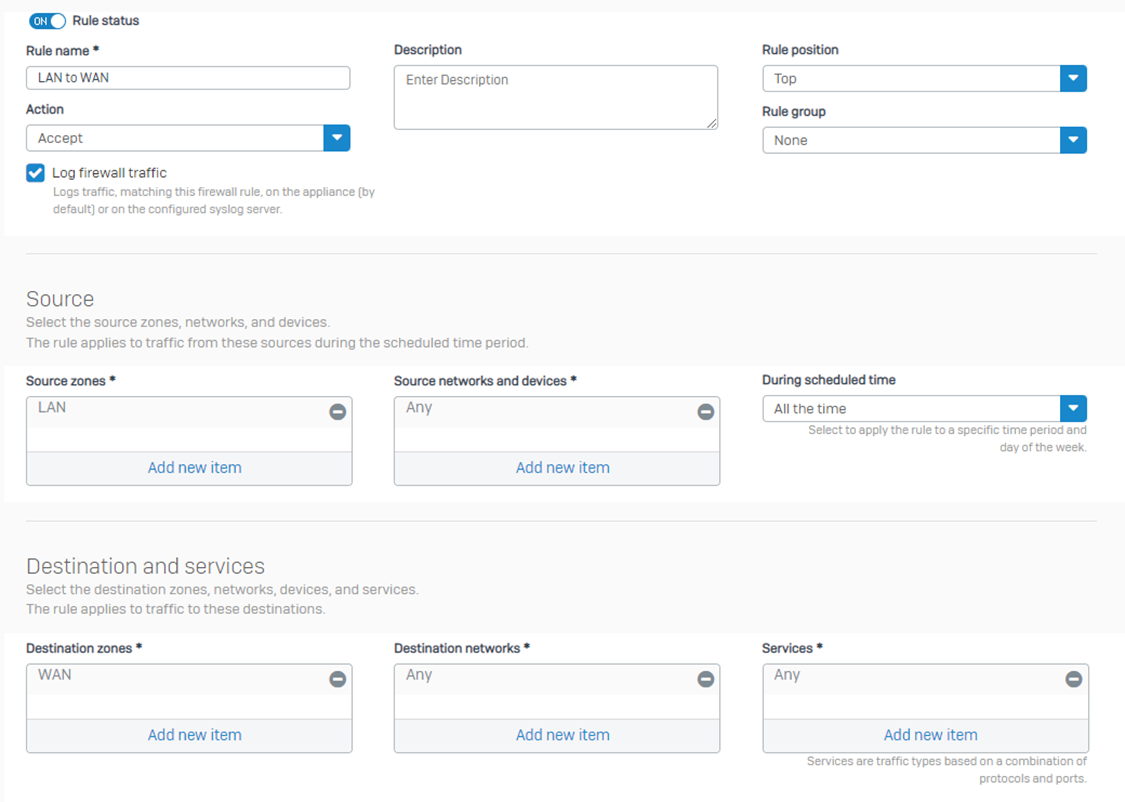
Step 2: Now, the next portion of the configuration is Add exclusion. You can use it to specify the criteria that you don't want to match for this rule. The firewall traverses the rule table further for the excluded criteria.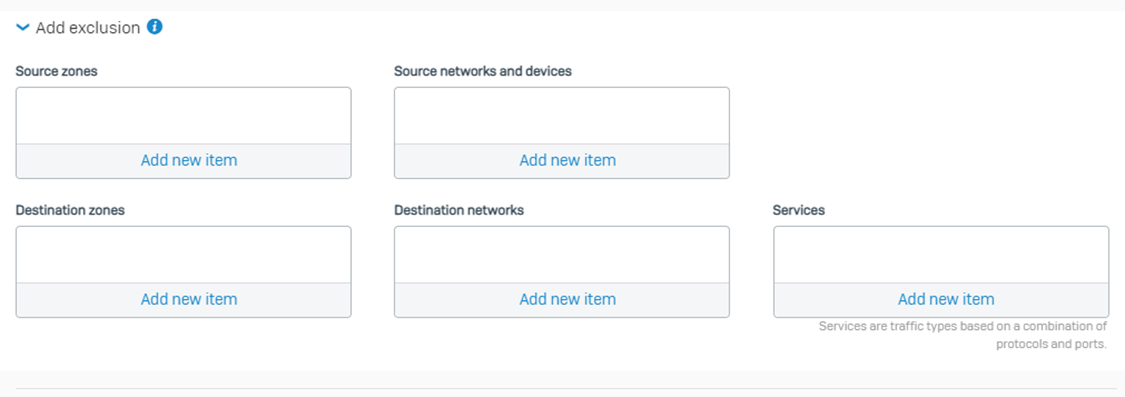
Step 3: Now, Scroll down to the same firewall rule and see the option “Create linked NAT rule.” Click the option. It isn’t a major change compared to v18.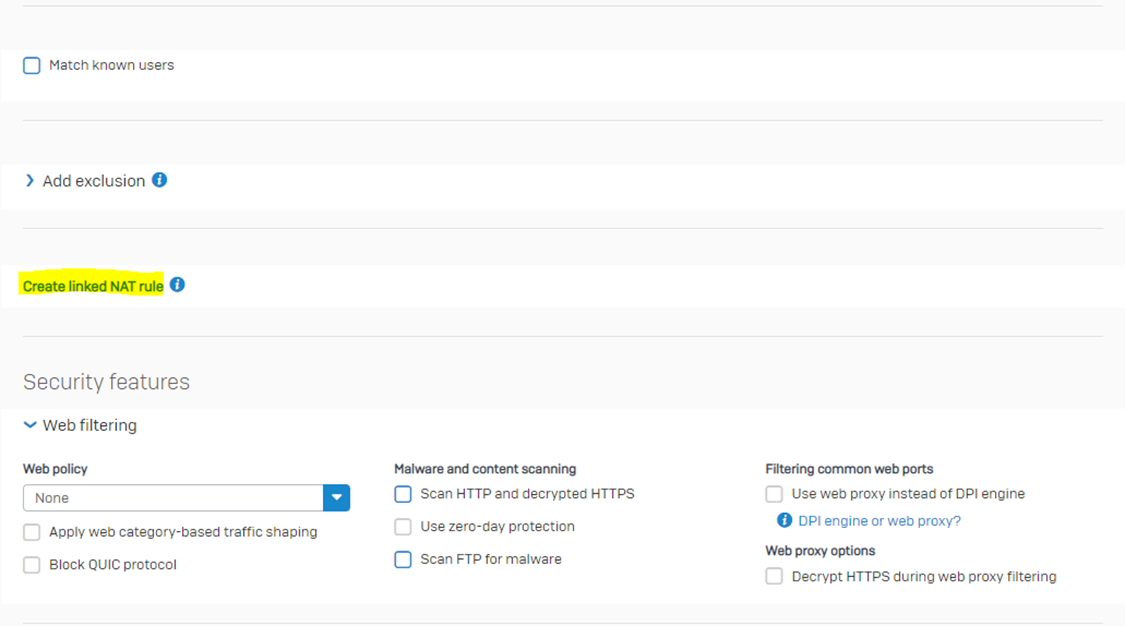
Step 4: If you create a NAT rule from this option, it’ll only apply to the traffic matching that specific firewall rule, and there will be some options that are greyed out, and you won’t be able to change them. You can't edit it in the NAT rule table, where it is listed along with all Source NAT rules. Further, it’s okay to NOT configure any NAT rule here. You must only configure a NAT rule from here to link that NAT rule only to this firewall rule.
Note that Sophos Firewall applies firewall rules before it applies source NAT rules. If a NAT rule meets the matching criteria and is listed in the NAT rule table above the linked NAT rule, Sophos Firewall applies that rule and doesn’t look further for the linked rule. Regardless of linked or unlinked NAT rules, Sophos Firewall will always follow the order shown approach and select the NAT rule just as it does for the Firewall rule for the matching criteria.
Turn on the MASQ option under the NAT rule LAN to WAN > Translated source (SNAT)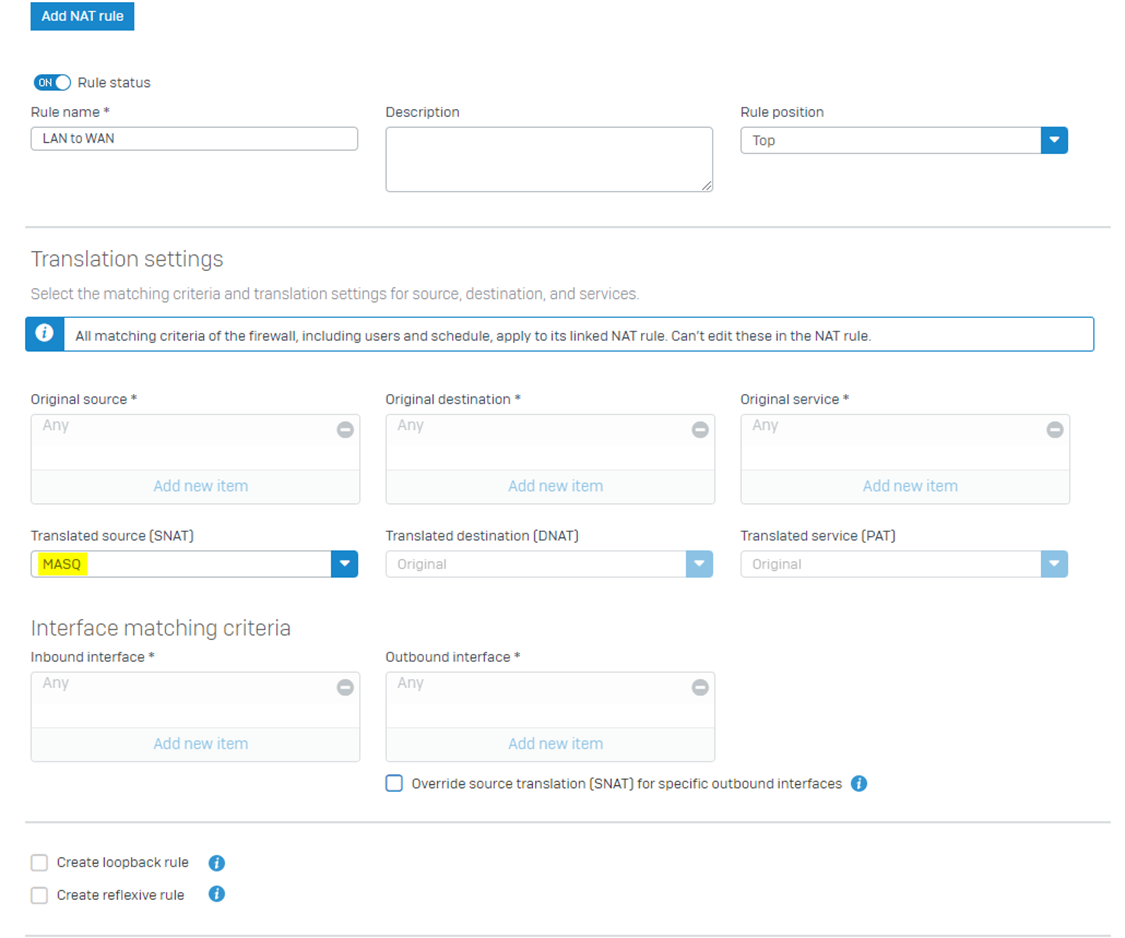
Step 5: The remaining part is shown in the screenshot below. You should select the options according to your requirements.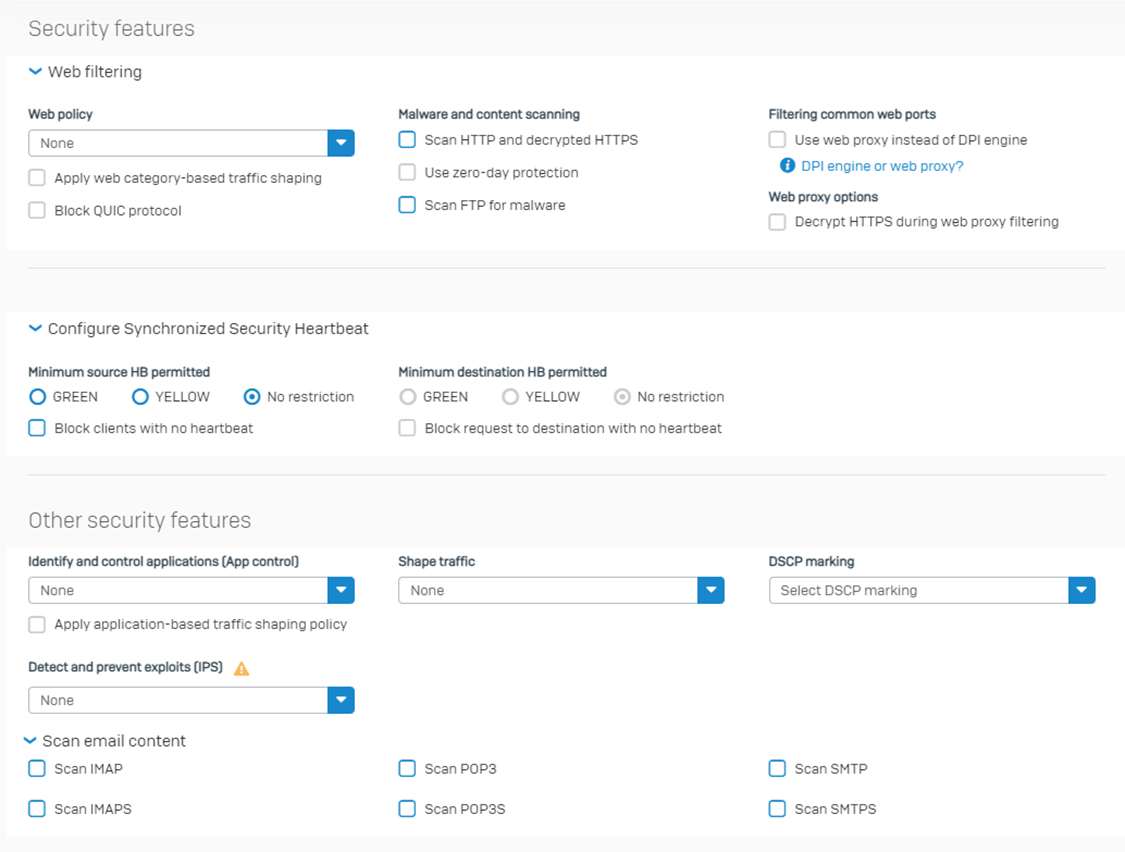
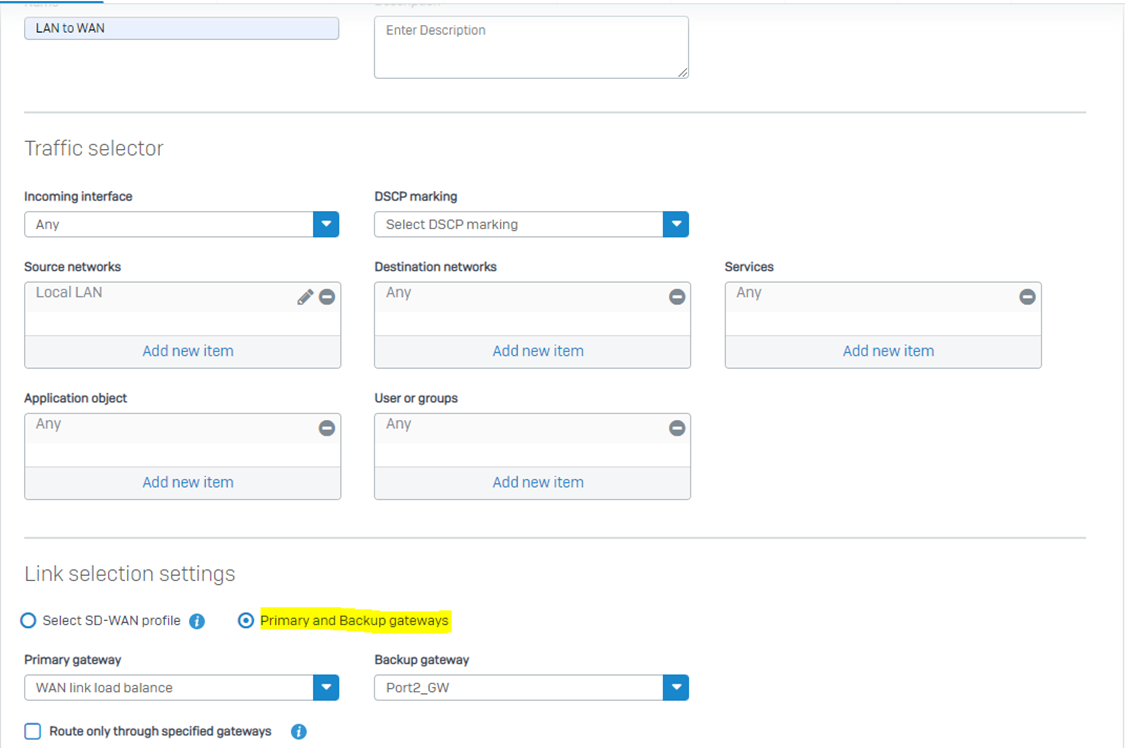
Step 6: Now, we’ll investigate how to send out the traffic from Sophos Firewall. Many granular controls are available to route traffic out from a specific interface if it matches certain criteria. Here is where the major significant changes are introduced from v19:
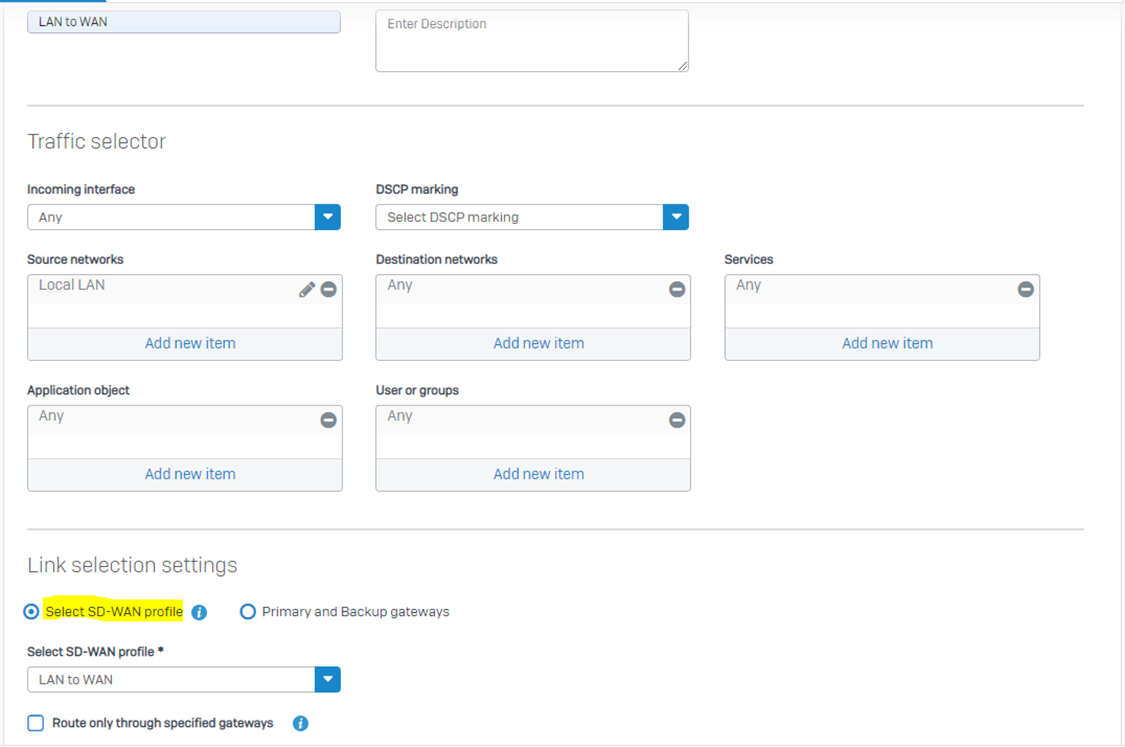
Path: Routing > SD-WAN routes > Add:
New SD-WAN Profile Settings From v19 Onwards:
Step 1: Now, the next-generation feature introduced is via SD-WAN profile, for which you would be required to create a profile under the following path:
Routing > SD-WAN profiles > Add
You select the gateway based on your required precedence of the available gateways:
SD-WAN can support up to 8 gateways.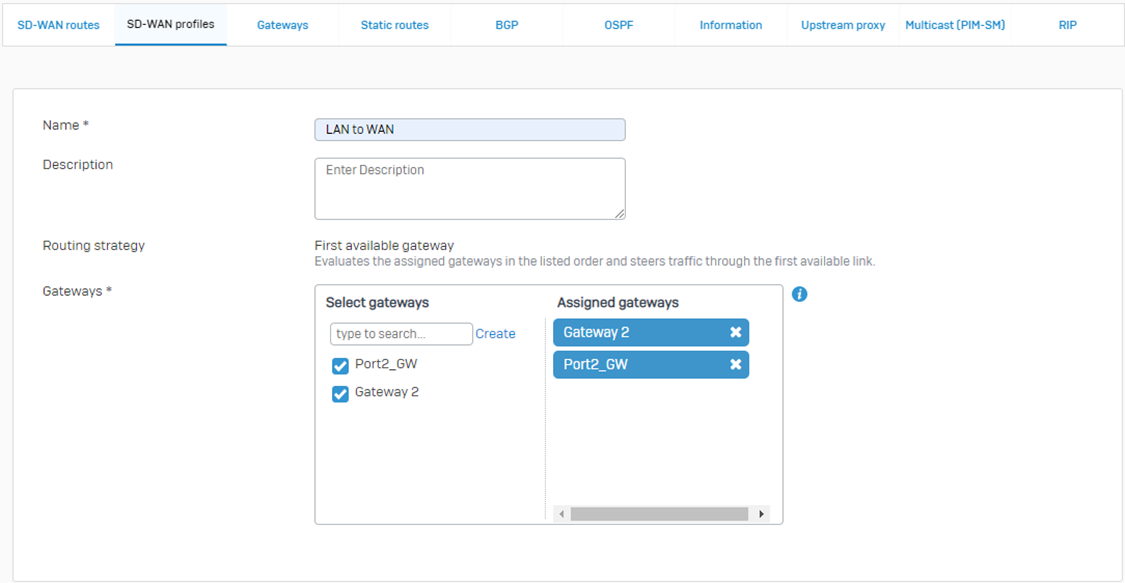
Step 2: Then comes the Service Level Agreement (SLA). For more details, please see: https://doc.sophos.com/nsg/sophos-firewall/19.5/help/en-us/webhelp/onlinehelp/AdministratorHelp/Routing/SDWANRoutes/SDWANProfiles/index.html
Note: Here, the Health check option remains on by default because we have the SLA turned on.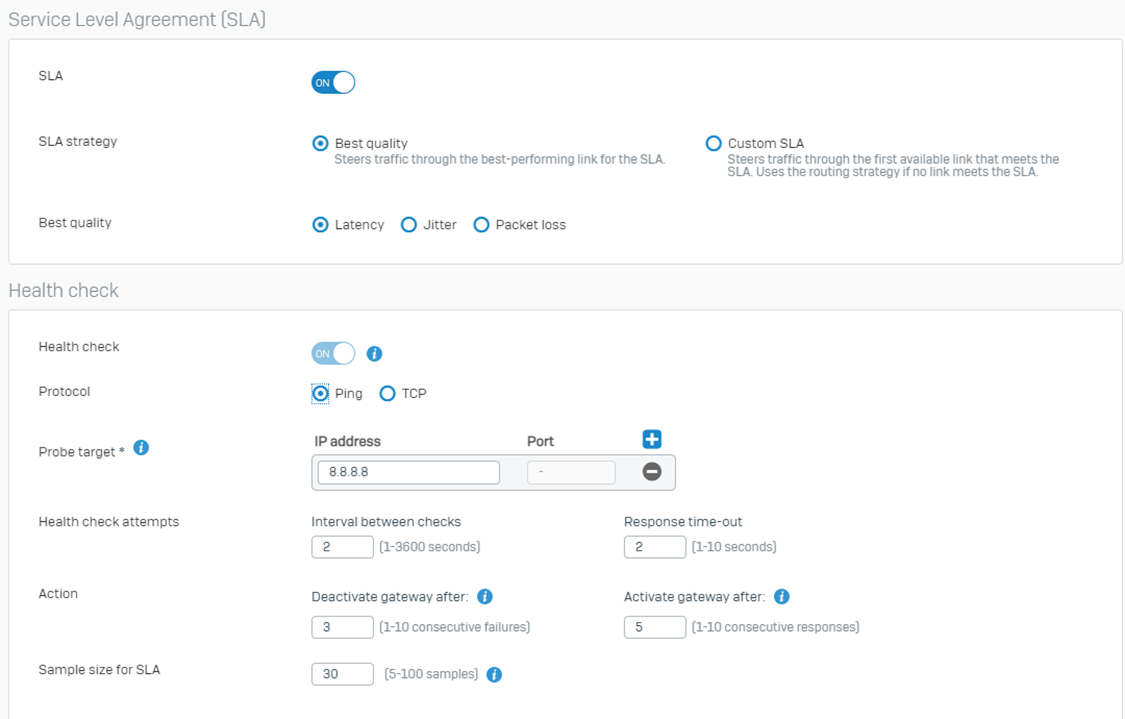
Once you save the SD-WAN profile, it will look similar to the screenshot below: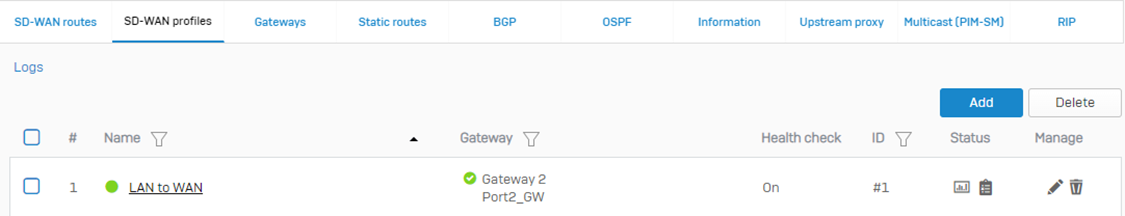
Step 3: Now, let’s apply this profile to our SD-WAN routes instead of using the traditional gateway settings we enabled in Step 6.
Once you save it looks like the screenshot below: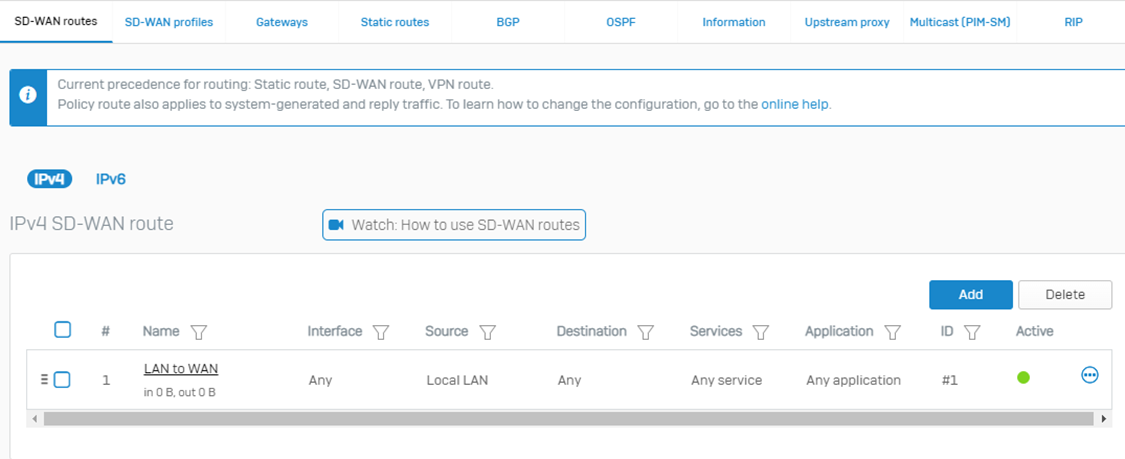
MASQ to Additional Address Interface on WAN
Special thanks to Quallensaft for the following information
How to Configure Additional Interface

I hope this article helps you understand the difference between previous firmware, i.e., SFOS v17, SFOS v18, and SFOS v19.
Revamping RR and added new Content
[edited by: Erick Jan at 6:22 AM (GMT -8) on 13 Feb 2025]