Disclaimer: This information is provided as-is for the benefit of the Community. Please contact Sophos Professional Services if you require assistance with your specific environment.
Table of Contents
Overview
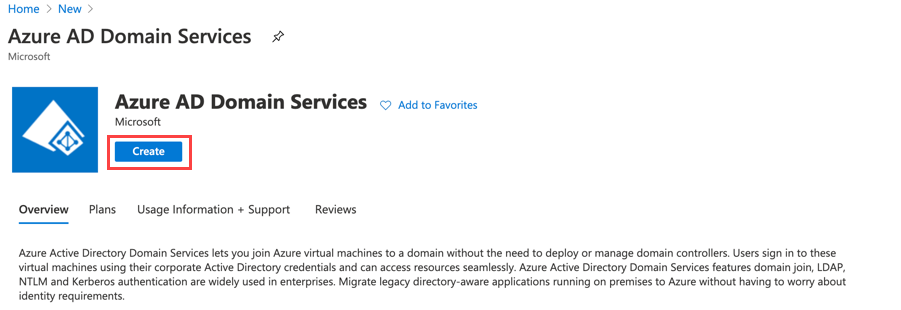
This recommended read applies to all the Sophos Firewalls running all versions. To integrate the Sophos firewall with Azure AD, we must create a new service called “Azure AD Domain Services”.
With this integration, administrators can use Azure AD for the following:
- Captive portal authentication of internal firewall users.
- Authentication agent for Windows, Mac, and Linux.
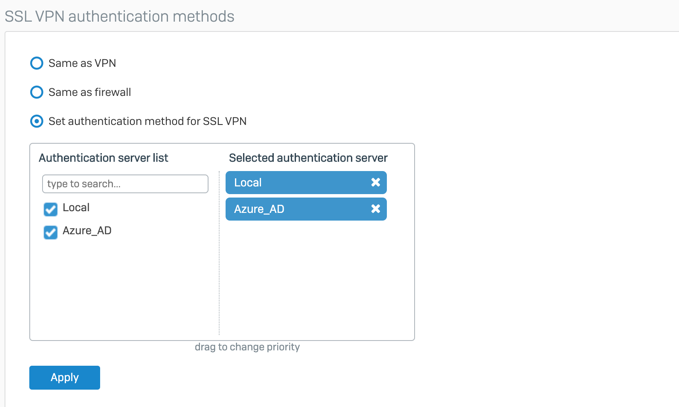
- SSL VPN authentication.
- Sophos Connect client
- Use the SSO using the Synchronized security UserID*.
Note: SSO with synchronized security and Azure AD must meet some specific requirements outside this document's scope.
Azure AD DS replicates identity information from Azure AD to a Microsoft-operated set of domain controllers, so it works with Azure AD tenants that are cloud-only or synchronized with an on-premises AD DS environment. The same set of Azure AD DS features exists for both environments.
Azure AD domain services offer an LDAP interface to Sophos that can replicate the working of an on-premise Active Directory. This article assumes there’s an existing Azure AD environment in place.
Azure configuration
- Login into the Azure portal and create Azure AD domain services. This step will take 60-90 minutes to set up. See the documentation from Microsoft on how to set up Azure AD domain services.
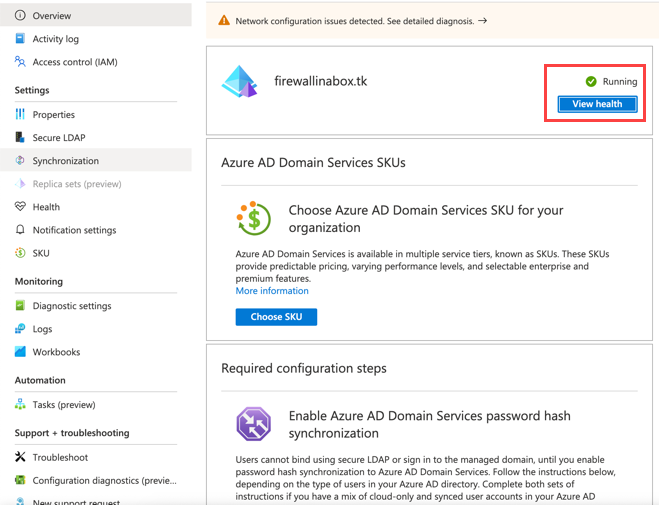
- Once the AD domain services are deployed, you can see the health status as “Running”.
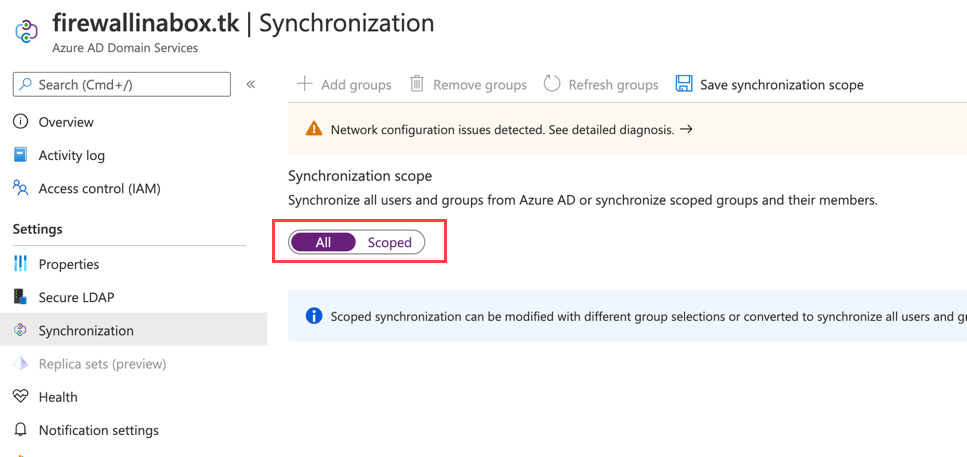
- Click Synchronize. You can either select scoped or choose to synchronize all the Azure AD.
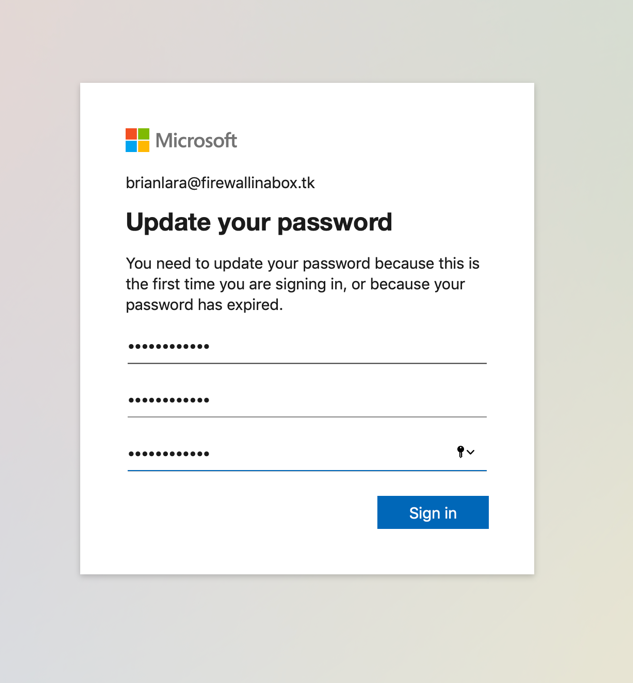
Note: The following step is required for cloud-only user accounts in Azure AD, as the Azure AD account isn’t synchronized with AD domain services until the user has changed the password by logging in to their office365 login. This password change process causes the password hashes for Kerberos and NTLM authentication to be generated and stored in Azure AD.
- Users must log in to the Office 365 portal and change the password. If it’s a new user logging into Office 365 for the first time, they’ll be prompted for the password change.
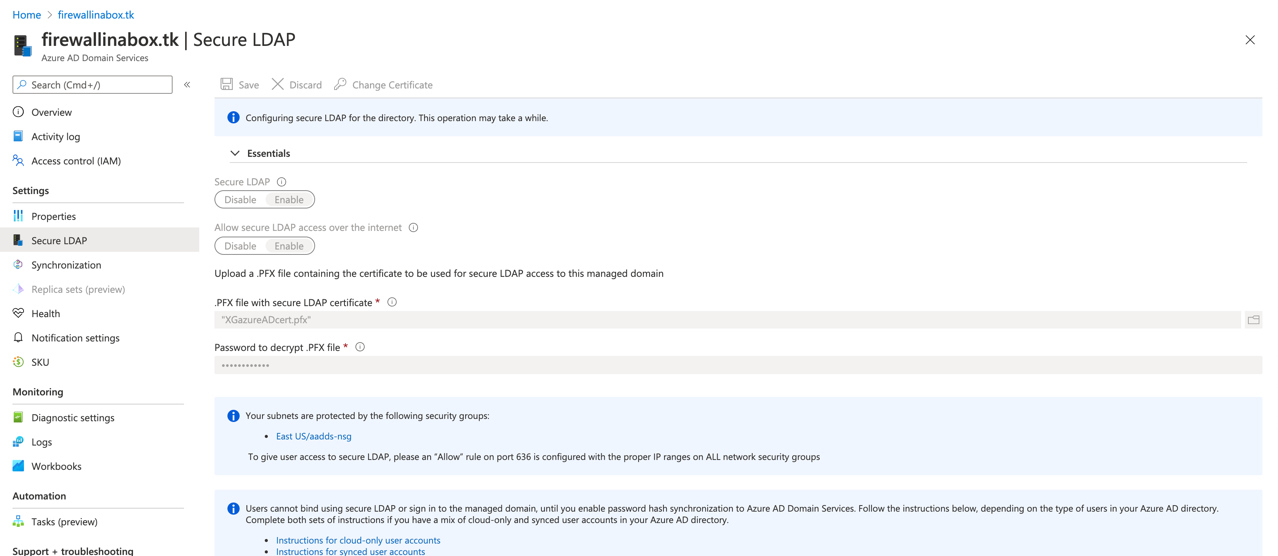
- Once the AD domain services are deployed, it's recommended to turn on LDAPs if the firewall sends LDAP bind requests over the internet. For additional security, we recommend creating an IPsec tunnel to Azure over which to bind the LDAP.
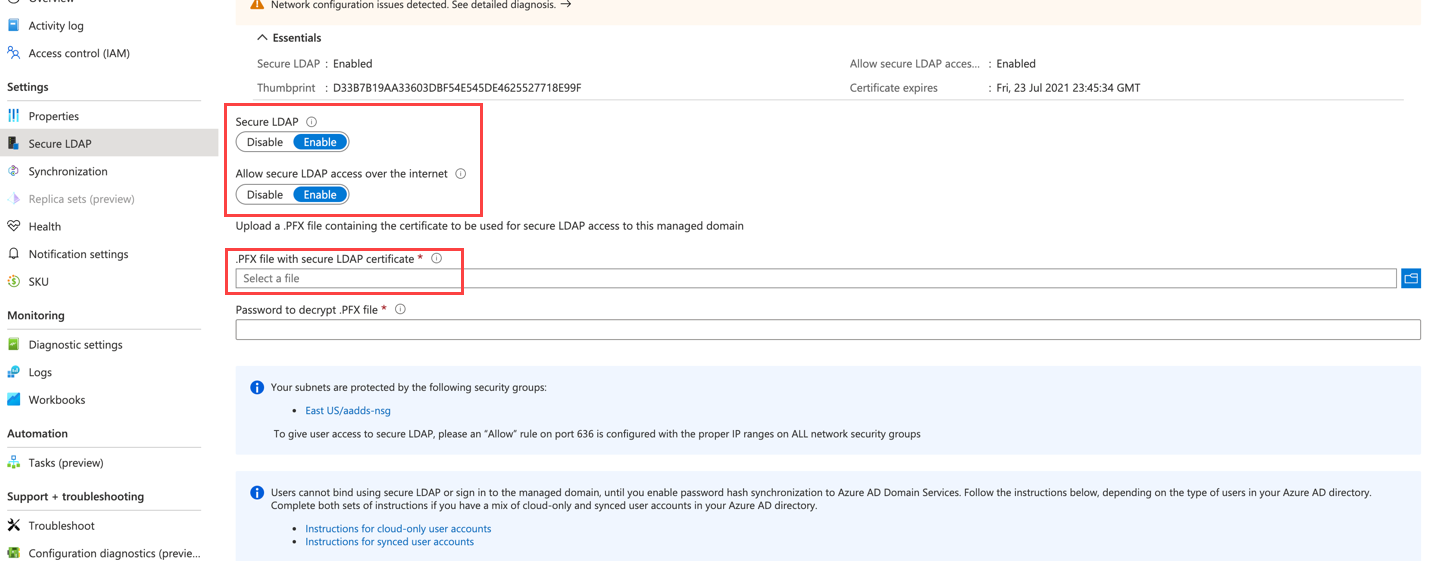
Note: Azure accepts self-signed certificates for this purpose. In this example, we use OpenSSL to generate a self-signed chain of certificates. Azure only accepts certs with “extended key usage for server authentication”.
Below is the process to generate self-signed Certs with EKU: server auth:
- To create the Certificate Authority Private Key and Certificate, you first need to create a private key for the CA with the name azureADca.key.
$ openssl genrsa -out azureADca.key 4096
Generating RSA private key, 4096 bit long modulus
..........................................................................................................................................................++
................++
e is 65537 (0x10001) - Create the CA certificate to validate signed certificates, called azureADca.pem.
$ openssl req -x509 -new -nodes -key azureADca.key -days 3650 -out azureADca.pem
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) []:CA
State or Province Name (full name) []:ON
Locality Name (eg, city) []:Burlington
Organization Name (eg, company) []:<Your org>
Organizational Unit Name (eg, section) []:Salesengineering
Common Name (eg, fully qualified host name) []:<Commaon name>
Email Address []:email@email.com - Create a text file and copy/paste the below text. Save the file as “azureAD-eku.conf” or any name you choose.
[client_server_ssl]
extendedKeyUsage = serverAuth - Now that this file exists, you must generate a private key for the LDAP cert named “ldapssl_private.key”.
$ openssl genrsa -out ldapssl_private.key 4096
Generating RSA private key, 4096 bit long modulus
...................................++
..........++
e is 65537 (0x10001) - Next, create a certificate signing request to sign with the CA you previously created with the name “azureADldapssl.csr” and fill in the following values in yellow.
$ openssl req -new -key ldapssl_private.key -out azureADldapssl.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) []:CA
State or Province Name (full name) []:ON
Locality Name (eg, city) []:Burlington
Organization Name (eg, company) []:firewallinabox
Organizational Unit Name (eg, section) []:Sales Engineering
Common Name (eg, fully qualified host name) []:<yourdomainname>
Email Address []:<email@email.com>Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:<Password> - You now need to sign the request, while including the signing extensions created earlier. The following command will create the signed cert named “azureADcert.crt”.
$ openssl x509 -req -extensions client_server_ssl -extfile azureAD-eku.conf -in azureADldapssl.csr -CA azureADca.pem -CAkey azureADca.key -CAcreateserial -out azureADcert.crt -days 365
Signature ok
subject=/C=CA/ST=ON/L=Burlington/O=firewallinabox/OU=Sales Engineering/CN=firewallinabox.tk/emailAddress=email@email.com
Getting CA Private Key
$ -
Convert the certificate into PFX format, as Azure accepts the certs in the PFX format.
$ openssl pkcs12 -export -out SophosazureADcert.pfx -inkey ldapssl_private.key -in azureADcert.crt -certfile azureADca.crt
Enter Export Password:
Verifying - Enter Export Password: -
Next, upload the SophosazureADcert.pfx file into Azure AD.
- To create the Certificate Authority Private Key and Certificate, you first need to create a private key for the CA with the name azureADca.key.
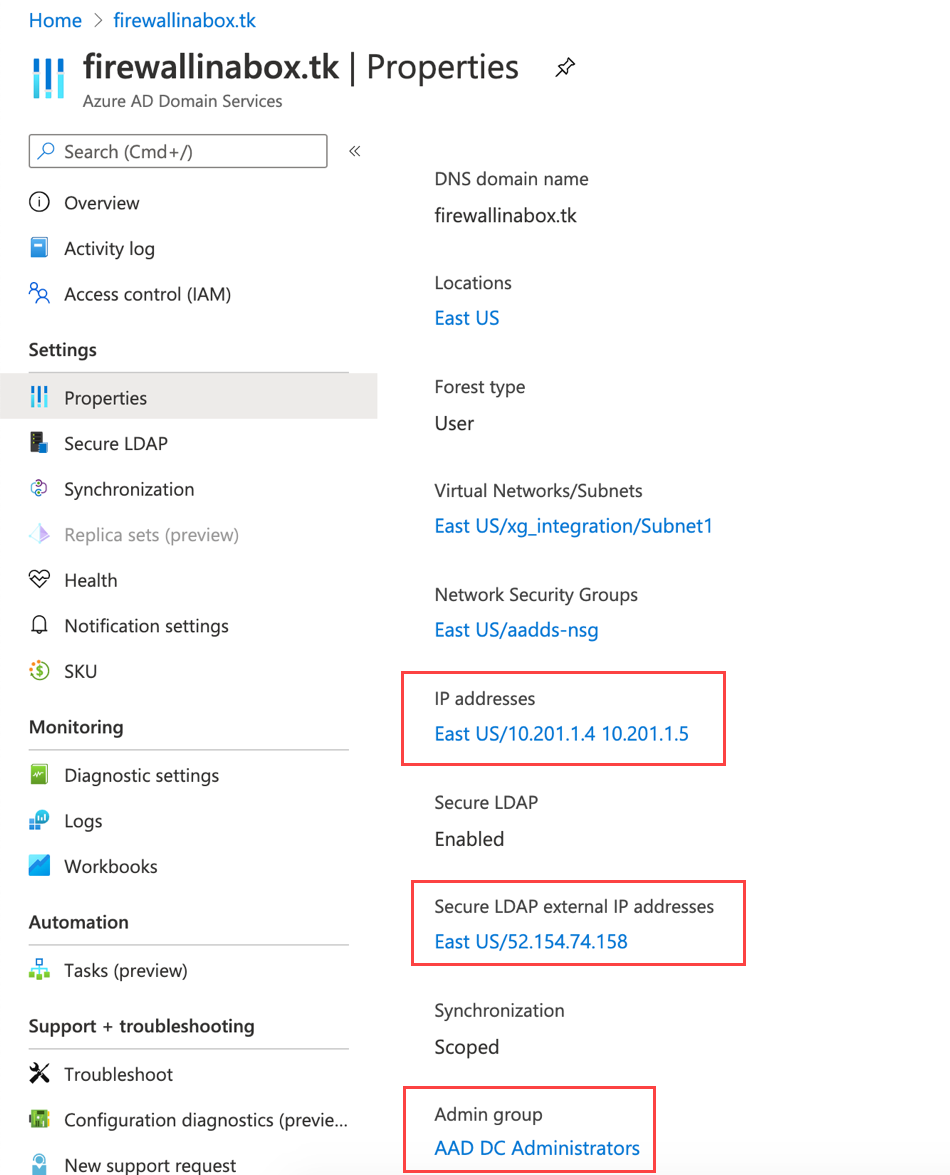
- Under Azure AD domain service, go to properties and note the following: Secure LDAP external IP address. If you’re connecting through an IPsec tunnel, you can use the internal addresses of 10.201.1.4 and 10.201.1.5 in this example.
- Ensure the admin group is selected with the correct administrator group used on the Sophos to send LDAP bind requests to AD domain services.
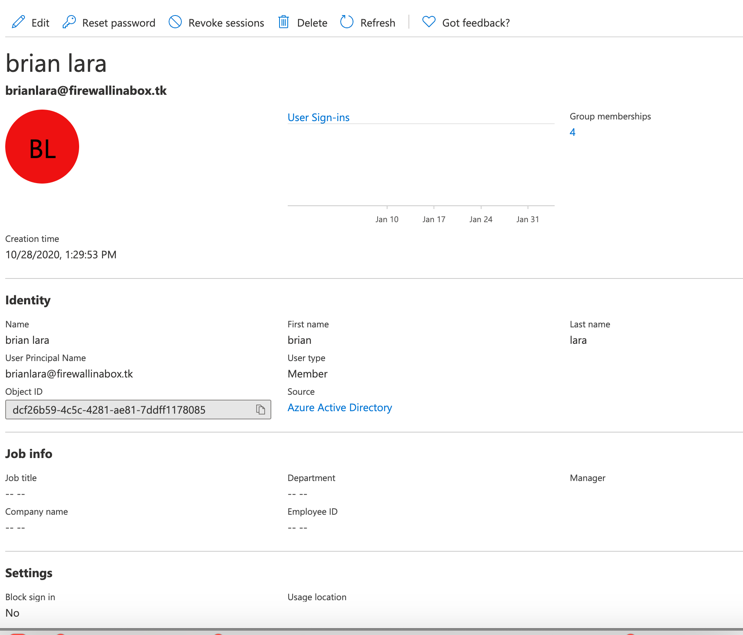
- In the Azure portal, go to Azure AD > Users and make sure the user is part of the AAD DC Administrators group inside Azure AD.
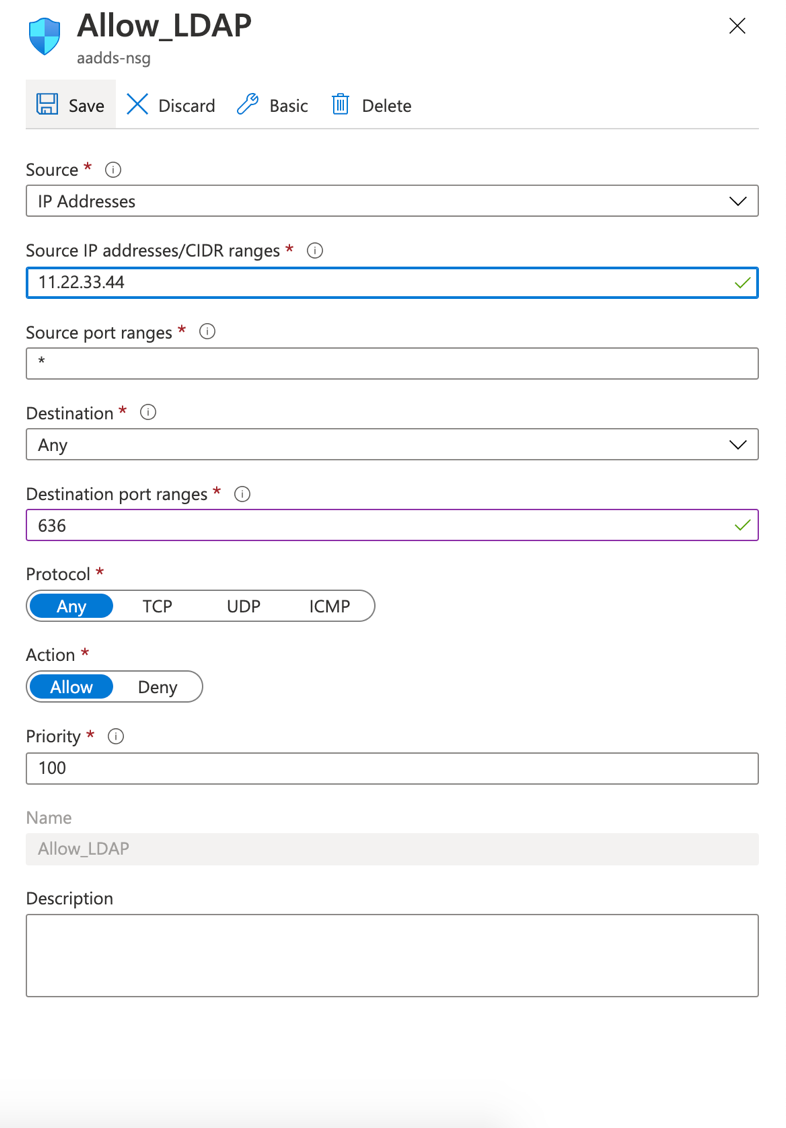
- In the Azure portal, go to to the Network security groups > Inbound security rules, then add a new inbound security rule allowing the LDAPs traffic from your firewall public IP. (This is optional and only required if you’re using an IPsec tunnel for additional security).
- The administrator account you’ll be using on the Sophos Firewall must first log in to Office365, and the password must be changed upfront.
Firewall configuration
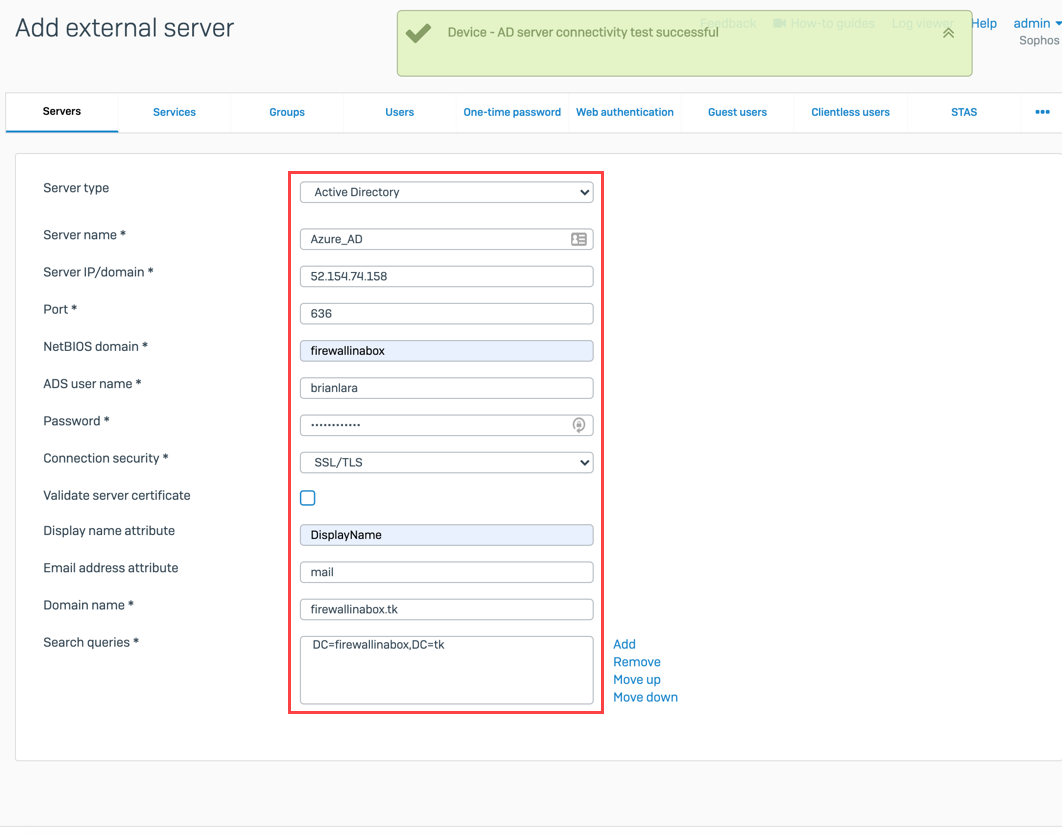
- Log in to the Sophos Firewall web UI, go to Configure > Authentication > Servers > Add, and use the following settings from the Azure AD domain services.
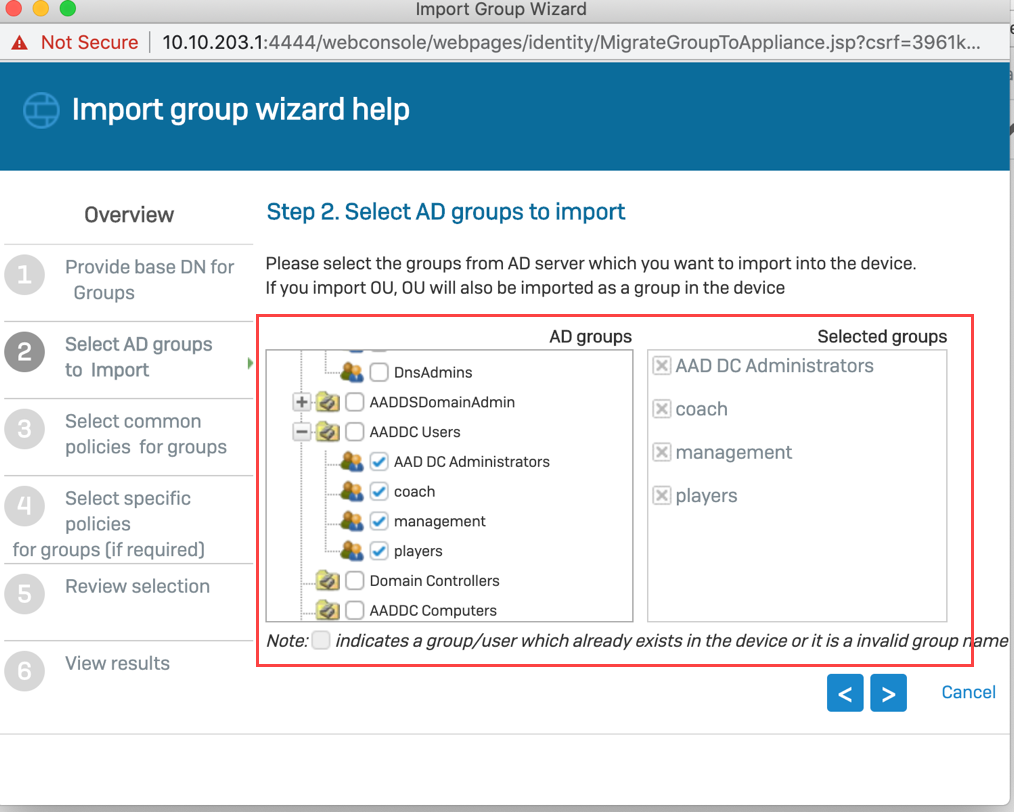
- Import the groups from Azure AD as shown below.
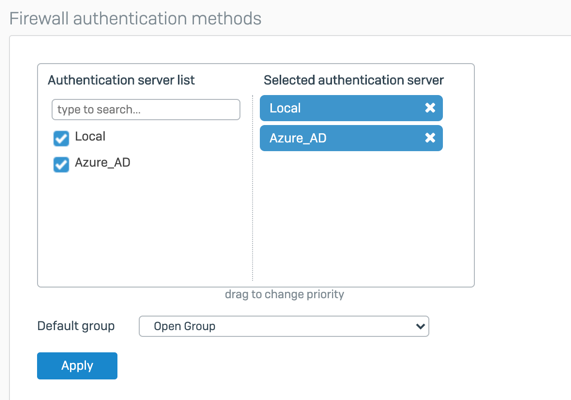
- Select the server from the list of authenticated servers from Configure > Authentication > Services.
- Test the authentication with the user portal; the login will be successful.
Edited Grammar, Horizontal lines
[edited by: Raphael Alganes at 11:07 AM (GMT -8) on 14 Nov 2024]

