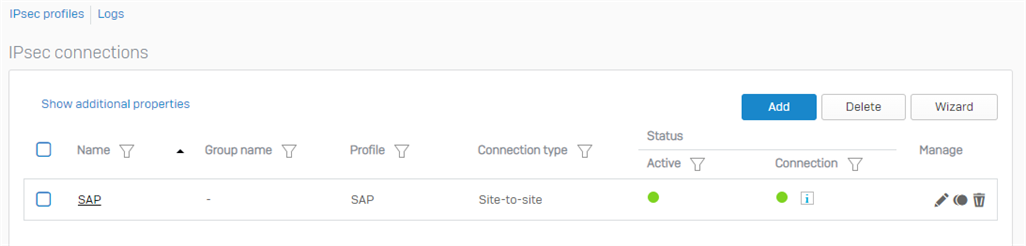
Hi, we have a Sophos XG210, SFOS 19. We set a site-to-site VPN tunnel to SAP with the parameters they gave us.
Locally, we have the network 10.X.X.X and 192.168.X.X (we are migrating to all class A), and SAP 10.100.0.0/22 & 10.100.4.0/27.
The tunnel works OK. We have connection between local hosts and remote servers in the SAP cloud. But, after some hours the tunnel goes down (I don´t know if it is important, but we are implementing SAP, there is only test traffic, not working officialy with SAP).
The status apears ACTIVE (green) but CONNECTION in YELLOW. If I restart the connection, the tunnel goes up and works OK.
If click in the information appears near "connection" item, I see that:
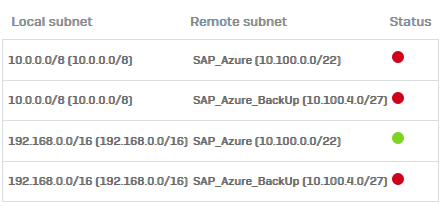
The problem is only with network class A. In the log console appers this message:
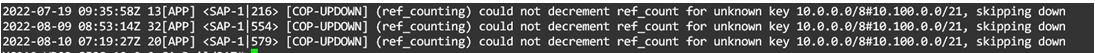
I don´t know if the problem is in SAP side, or maybe I need to configure a more specific network in my site (no /8)
This thread was automatically locked due to age.


