Hello, I am starting this discussion to solicit joint interest in the lack of a "Details" link for events on a macOS machine. Please vote using the ideas link below if you share the same sentiment.
When responding to alerts in Sophos Central, the first thing I do is gather as much information as possible from the alert itself. Whether the endpoint is Windows or macOS, I need to be able to view details such as the file hash, raw detection data, file publisher, etc. in order to properly triage the alert.
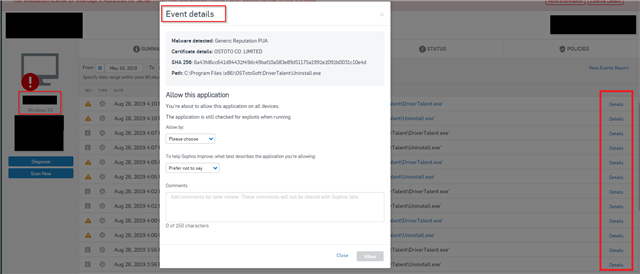
After reviewing an alert, I go directly to the events tab of the device in question. On a Windows machine I am able to click a "Details" link for each of the events that were alerted on, as well as the events that may have preceded the detection. On a macOS machine no such link exists, so I am left relatively blind to details that are crucial to continue my investigation.
I was told that because many of the detections I was seeing were PUPs and PUAs, a detail link was not provided since they are not necessarily malicious in nature. However, I also encountered instances where I cannot see details for 'Malware detected: 'Mal/Phish-A' events either. In addition to this, I should be able to view details on PUP and PUA detections (just like is available in Windows) so that my teammates and I can make the determination on whether to block the application across our environment.
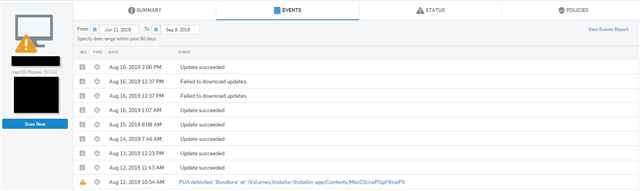
Example 1 - No event details for detection on macOS machine (Malware detected: 'Mal/Phish-A')
Example 2 - No event details for detecion on macOS machine (PUP)
Windows OS example, PUP/ PUA showing event details
This thread was automatically locked due to age.