Good morning,
I hope we are all having a healthy/safe social distancing morning. I am tinkering with my home UTM, now that I seem to have lots of time.
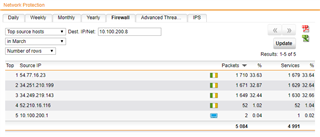
I am seeing lots of traffic blocked in my web filter logs from my AP15.
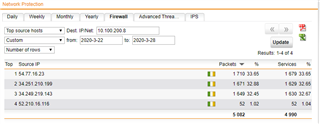
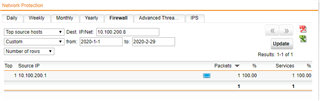
2020:03:25-09:56:47 hostname httpproxy[7621]: id="0061" severity="info" sys="SecureWeb" sub="http" name="web request blocked, reputation limit" action="block" method="CONNECT" srcip="10.100.200.8" dstip="" user="" group="" ad_domain="" statuscode="403" cached="0" profile="REF_HttProContaLanNetwo2 (Core_Devices_Profile)" filteraction="REF_HttCffCorefilter (Core_Filter_Action)" size="3270" request="0xe560d100" url="https://34.251.210.199/" referer="" error="" authtime="0" dnstime="0" aptptime="98" cattime="140" avscantime="0" fullreqtime="244564" device="0" auth="0" ua="" exceptions="" reason="reputation" category="9998" reputation="unverified" categoryname="Uncategorized"
2020:03:25-09:56:53 hostname httpproxy[7621]: id="0061" severity="info" sys="SecureWeb" sub="http" name="web request blocked, reputation limit" action="block" method="CONNECT" srcip="10.100.200.8" dstip="" user="" group="" ad_domain="" statuscode="403" cached="0" profile="REF_HttProContaLanNetwo2 (Core_Devices_Profile)" filteraction="REF_HttCffCorefilter (Core_Filter_Action)" size="3270" request="0xcc8ca00" url="https://34.249.219.143/" referer="" error="" authtime="0" dnstime="0" aptptime="137" cattime="146" avscantime="0" fullreqtime="236847" device="0" auth="0" ua="" exceptions="" reason="reputation" category="9998" reputation="unverified" categoryname="Uncategorized"
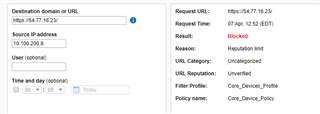
2020:03:25-09:56:58 hostname httpproxy[7621]: id="0061" severity="info" sys="SecureWeb" sub="http" name="web request blocked, reputation limit" action="block" method="CONNECT" srcip="10.100.200.8" dstip="" user="" group="" ad_domain="" statuscode="403" cached="0" profile="REF_HttProContaLanNetwo2 (Core_Devices_Profile)" filteraction="REF_HttCffCorefilter (Core_Filter_Action)" size="3264" request="0xc1e1c300" url="https://54.77.16.23/" referer="" error="" authtime="0" dnstime="0" aptptime="97" cattime="123" avscantime="0" fullreqtime="236449" device="0" auth="0" ua="" exceptions="" reason="reputation" category="9998" reputation="unverified" categoryname="Uncategorized"
- These hosts all resolve to Sophos Central. Isn't it strange that Sophos' own IPs are listed as uncategorized/unverified?
- Why does my AP need to talk externally at all? I have never, nor do I plan to use Sophos Central to manage my UTM in any way.
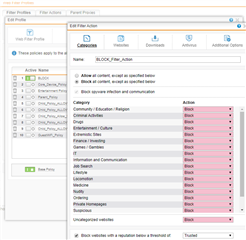
I have not seen this before, and have always kept all of my core systems (by IP) in a group that gets very restrictive web filter URL blocks.
This thread was automatically locked due to age.