Hello, I'm new here but did not find any issue like mine so I decided to give it a chance
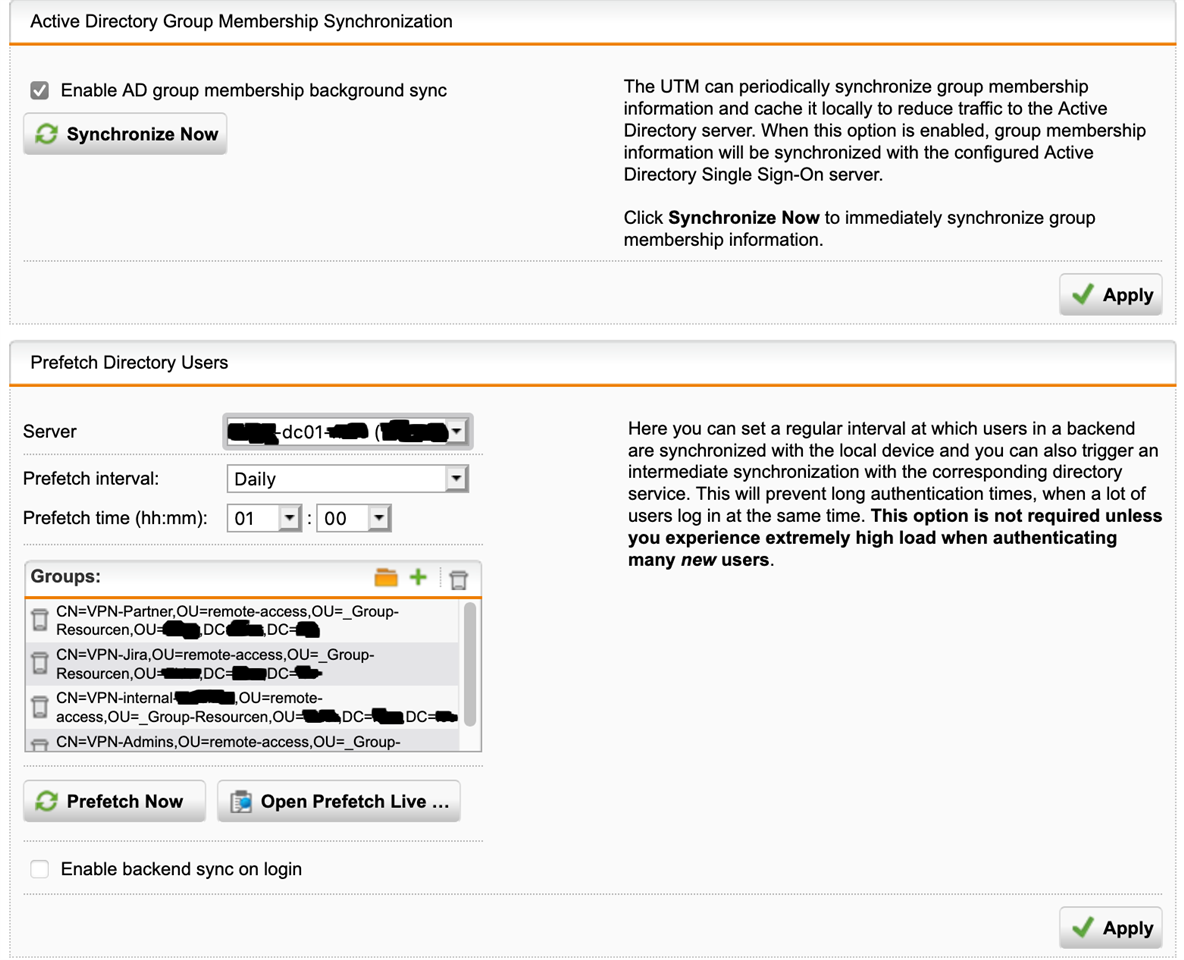
I'm taking over a Sophos UTM (standby cluster) integrated with ActiveDirectory (authentication server, SSO).
Software is 9.705-3 on Sophos HW SG550
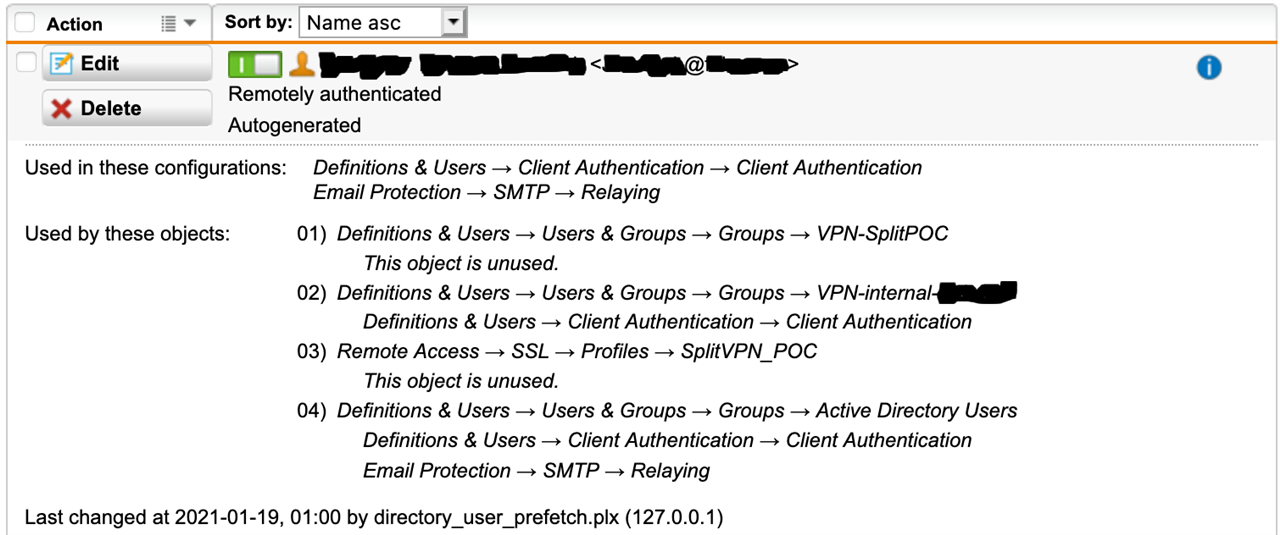
AD users are able to login to the portal and also the users are created within the UTM as expected.
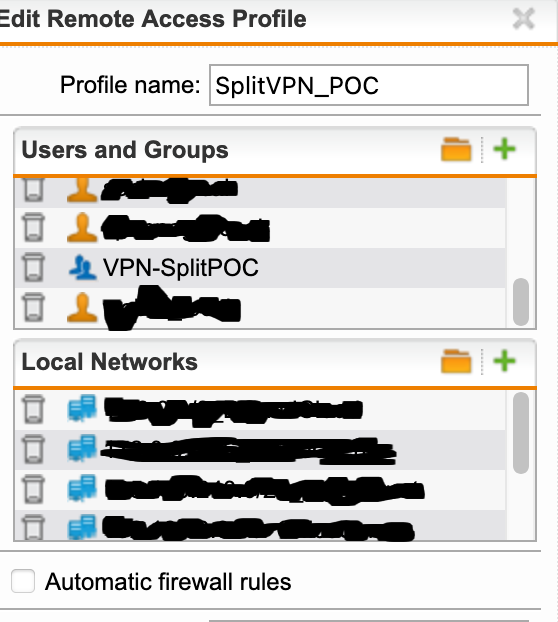
Currently there is one SSL VPN Profile (Group "Active Directory Users") which enables all AD users to connect - that is working fine.
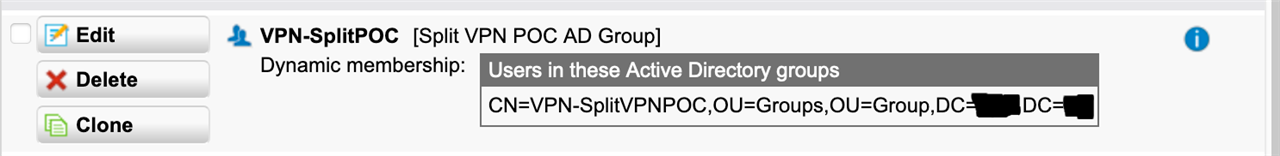
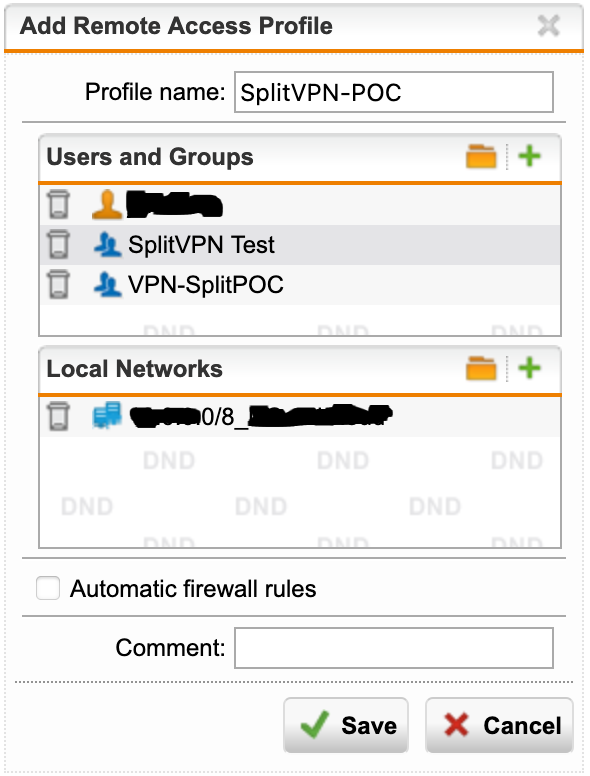
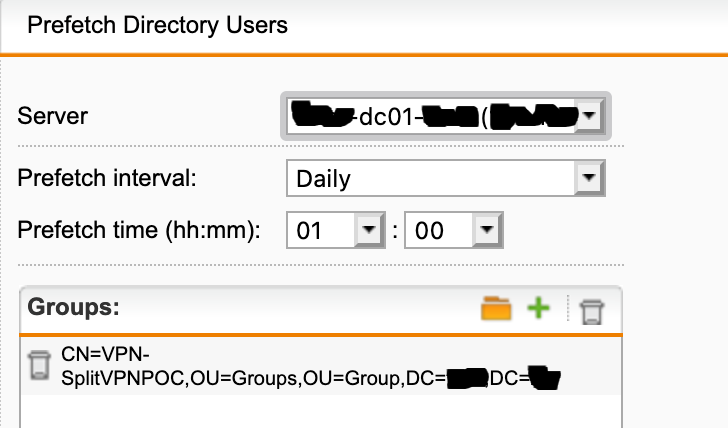
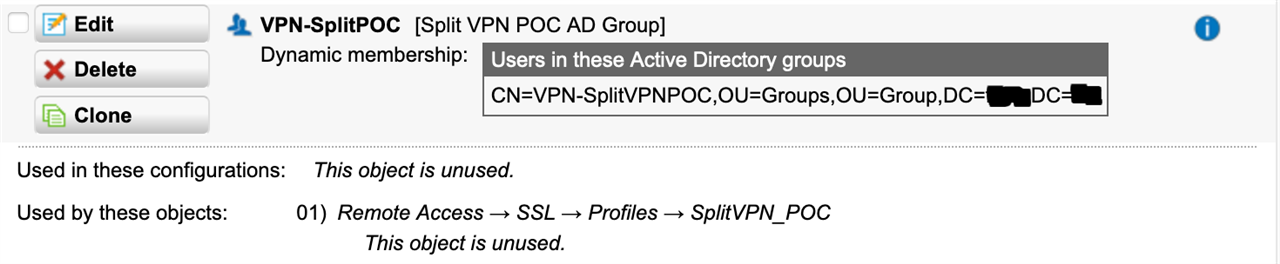
We now wanted to create AD Groups to control a little bit "who" is able to login and with which profile (there are lot of how to's).
Thats where our issue starts but I didn't find a solution anywhere.
Issue is that the new groups are totally ignored and removing this "Active Directory Users" Group results in no one being able to connect anymore.
Debug steps I did already:
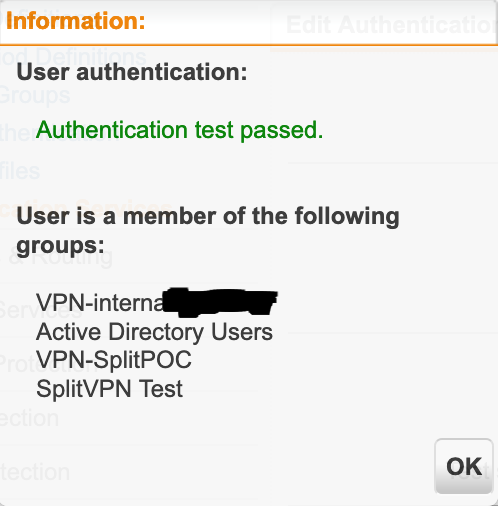
* Authentication Servers are setup and working - test with my user shows "Passed" and gives me all UTM groups I'm member of - also the mentioned VPN groups I've created and used in the SSL VPN profiles.
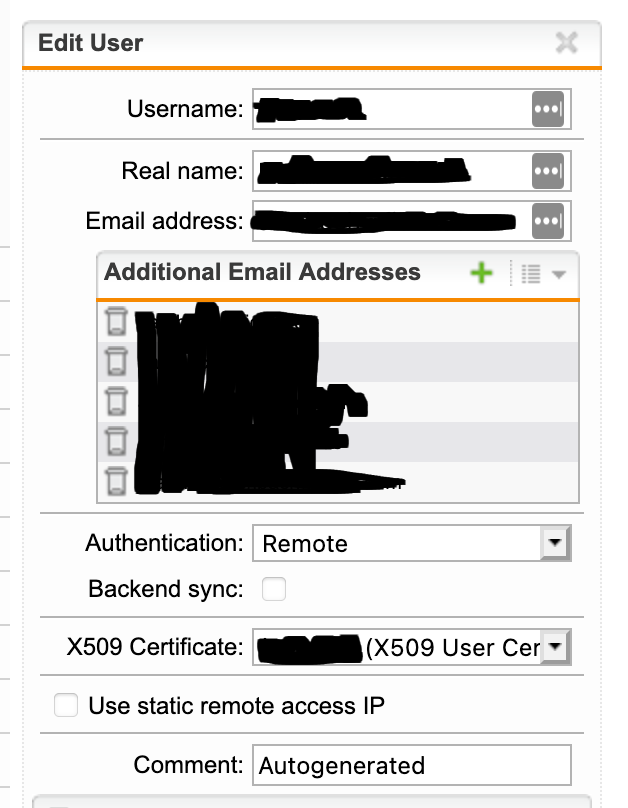
* Adding my UTM user (backend authenticated) directly also has no effect at all
* Sophos support didn't find a solution for this so far (we started a case months ago but did not follow up anymore - will have to restart this)
My current guess is, that there is some kind of Bug with our configuration.
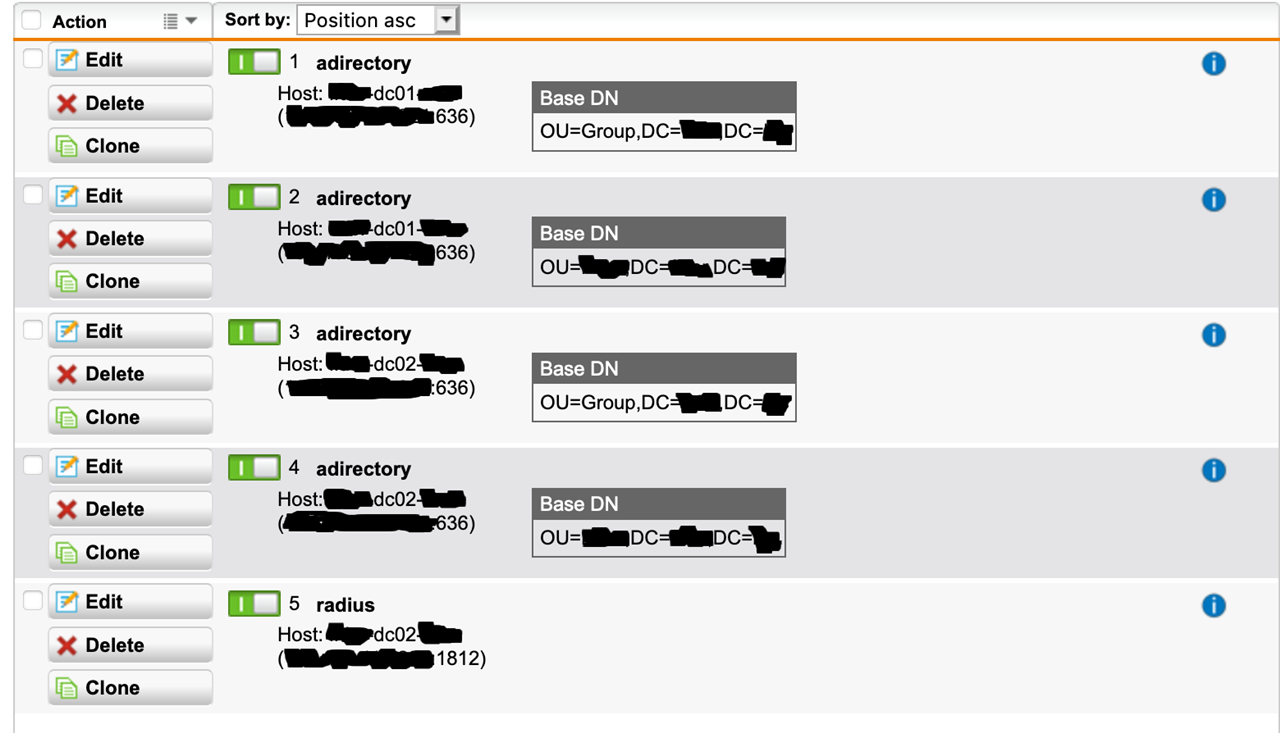
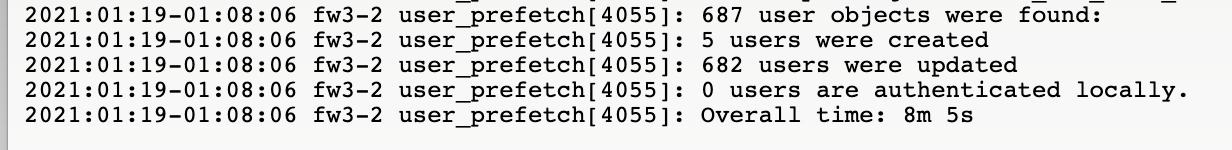
One thing which "might" cause it is, that we have two AD servers but four authentication backend servers defined... two per server with different base-OUs as we are in the middle of a migration - so users and groups are in different base-OUs currently - but I guess thats no correct.
The plan would be either to move everything into the same base-OU, or set the base-OU to the domain root anyways but does anyone know if this could cause the issue we are facing?
There is also an no more used radius backend.
I've already tested it with a group being in the same bsae-OU than the user but that didn't work either.
I thought at least adding my AD cloned user to another profile directly will result in some reconnect with combined routes but it just did nothing.
Doing this with a local user (locally authenticated) results in the expected behavior.
Summary:
* Groups are working
* Users can authenticate (portal, test auth)
* Groups can be found by UTM and users are shown as members of the groups (test auth)
* Users can use VPN (are member of the not limited AD backend Group)
Issue => AD backend users are ignored in the SSL VPN profile config when used directly or via limited AD backend groups.
Thank you for your ideas - if I need to provide any further information, I will try to do so.
This thread was automatically locked due to age.