DNS Best Practice
You might have seen the model we use as I've described it in many places here:
- The 'Global' tab of 'Network Services >> DNS' lists "Internal (Network)" (also other internal networks, like "DMZ (Network)" and any "VPN Pool" if applicable) as 'Allowed networks'.
- On the 'Forwarders' tab, if you use or plan to use the SMTP Proxy, use an Availability Group containing the OpenDNS or Google (8.8.4.4 first, for speed) name servers in 'DNS Forwarders' (if using any spamhaus.org RBLs with the SMTP Proxy, don't use Google DNS). 'Use forwarders assigned by ISP' is not checked.*
- If the SMTP Proxy is not to be a part of your setup, don't add anything in 'DNS Forwarders' and do select 'Use forwarders assigned by ISP'. See the Change Log below concerning CDNs.
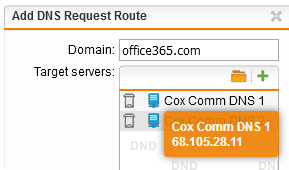
- Alternatively, if you're using a Microsoft CDN like Office365, do use the Availability Group approach above and add a Request Route for office365.com pointing at your ISP's name server.
- In 'Request Routing', the internal DNS is used for reverse DNS of internal IPs (for example if your internal subnet is 172.16.20.0/24, you would have "20.16.172.in-addr.arpa" in the 'Domain' field and your internal DNS server(s) in 'Target Servers'. With that, the UTM can list machine names instead of internal IP addresses in the reports.
- Also, in 'Request Routing', so the UTM can resolve internal FQDNs, add, for example 'yourdomain.loc -> {internal DNS server}'. Do the same for other domains for which you have Forward Lookup Zones in your internal DNS server.
- Configure Windows Server (or other) DHCP server for internal devices to point at your internal name server for DNS, then the UTM, then the OpenDNS or Google servers.
- The internal DNS server's first forwarder is to the UTM's DNS Proxy, then to the OpenDNS or Google servers.
- If you consistently have "connection to server timed out" issues and ECN is not selected ('Advanced' tab of 'QoS'), empty 'Allowed networks' in #1, configure the internal DNS server to bypass the UTM in #6. I suspect this is caused by a problem at the ISP.
- In Transparent mode Web Filtering, the client browser resolves FQDNs. When Pharming Protection is enabled at the bottom of the 'Misc' tab, the Proxy will block a request with "Host Not Found" if it cannot resolve the FQDN to an IP. If disabling Pharming Protection eliminates such blocks for you, then you have not followed #1 through #7.
We used to do it the other way, but comments by BarryG, BruceKConvergent and others convinced me to change our approach.
Cheers - Bob
* Caution: unchecking 'Use forwarders assigned by ISP' and failing to populate 'DNS Forwarders' will result in degraded performance as the ASG/UTM will fall back to the Root Name Servers.
Change Log: 2020-02-14 Based on a post by wolfman1, I added a warning in 2. about using Google if spamhaus.org is one of the RBLs used in the SMTP Proxy; 2017-11-13 Added 2.a and 2.b based on further info in Alex Busch's thread; 2017-11-12 Added the caveat to #2 about the SMTP Proxy because of Alex Busch's comments about Content Delivery Networks (CDNs); 2017-08-02 added #8 based on a comment by Sophos' Michael Dunn; 2017-06-09 added "VPN Pool" to #1; 2017-04-08 made #3 clearer based on a question by jlbrown also added "or Google" to #5 & #6; 2017-02-12 added 8.8.4.4 comment to #2 based on a comment here by rfcat_vk; 2017-01-14 added "in the 'Domain' field" in #3; 2015-09-25 In #7 corrected #5 to #6; 2015-09-24 changed Astaro to UTM and added #7 based on comments by vilic in DNS issue?; 2015-06-22 based on a thread by TCF, I improved the wording in #1, #2 & #4; 2015-06-20 changed from .local to .loc as reminded by bimmerdriver; 2015-03-20 Added title; 2014-10-04 DHCP and internal FQDNs; 2013-10-09 Added Availability Group idea from adrienjb in #2; 2013-02-04 reordered; 2012-08-20 Added "* Caution" note for #2 based on a suggestion by BarryG
Tags
[edited by: FloSupport at 11:06 AM (GMT -7) on 18 Sep 2020]