Hi everyone,
we are having issues with the customers skype for business (still on prem) because of IPS.
After a while the voice stops and our users at the office (it is working from home or data plan) cannot voip anymore.
The IPS log shows the IP(s) of the customer and UDP flood.
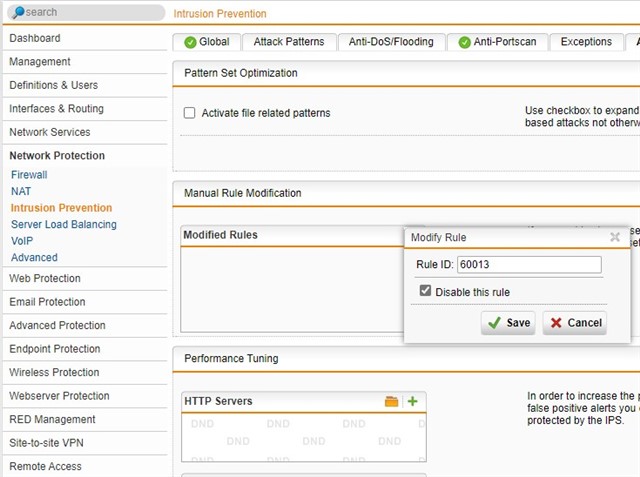
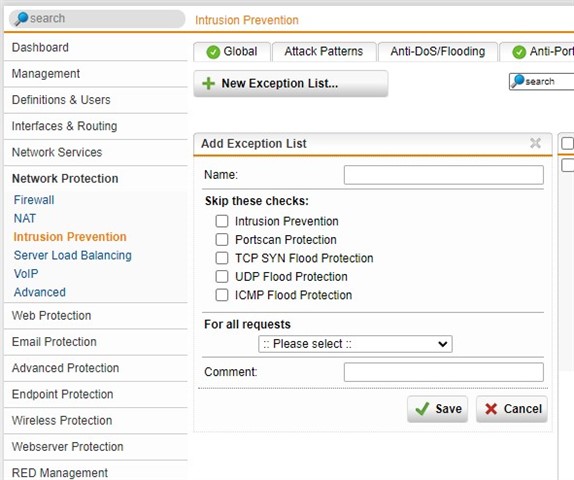
As i do not know which customers use what IP, i cannot (and i don't wanna) configure all IPs (ranges are not working) in IPS exceptions. Is there an easy way (without disabling UDP flooding) to accomplish good voice quality for everyone?
Or can i whitelist "german or some european countries" for UDP flooding?
Log entry where 213.95.x is the customers skype server
2021:11:17-14:10:56 fw3str-1 ulogd[35793]: id="2105" severity="info" sys="SecureNet" sub="ips" name="UDP flood detected" action="UDP flood" fwrule="60013" initf="eth5" srcmac="3c:13:cc:53:df:80" dstmac="00:1a:8c:f0:4e:65" srcip="213.95.x" dstip="62.96.x" proto="17" length="650" tos="0x00" prec="0x00" ttl="122" srcport="53916" dstport="20388"
BR
Stephan
This thread was automatically locked due to age.