Hi all,
we experience a strange issue when trying to connect an UTM to a XG via SSL-VPN. Unfortunately, IPSec cannot be used as the UTM stands behind a router and no fixed public IP is available.
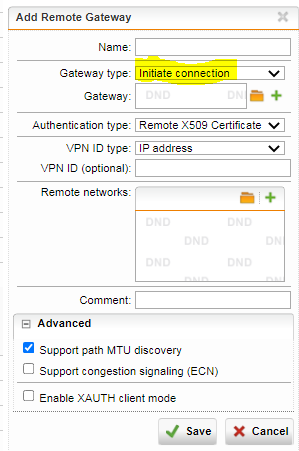
We have configured the SSLVPN settings as follows:
- Protocol: UDP
- SSL Server Certificate: WILDCARD.customer.de (the error is the same with a specific certificate for the DNS name vpn.customer.de)
- Port: 443
When importing the SSLVPN configuration file to the UTM, the live protocol gives the following error:
VERIFY X509NAME ERROR: /CN=_.customer.de, must be CN=*.customer.de
I read somewhere that Sophos does not support using wildcard certificates for SSLVPN - strangely it works when connecting to the XG via OpenVPN client (current version 2.5.3). But OK - I bought another certificate for vpn.customer.de and assigned it to the configuration. Then I exported and imported the configuration on the UTM again. The error is somehow the same:
VERIFY X509NAME ERROR: /CN=vpn.customer.de, must be CN=vpn.customer.de
When I look at the certificates uploaded to the XG configuration (hovering over the certificate with the mouse), it tells me that the subject is "/CN=vpn.customer.de". So where does this slash come from? Obviously, the UTM cannot read such certificate correctly but I cannot modify the subject. Either this is a bug in the upload process of the XG or a bug in the OpenVPN client included in the UTM.
If I switch to the ApplianceCertificate, everything works but we want to use public certificates for that. Am I doing something wrong?
Thanks in advance and greetings
Ben
This thread was automatically locked due to age.