Hello,
In Sophos UTM SG there was a user prefetch - I am really missing this feature because I need to send quarantine-mails to every user on our on-prem exchange.
Can´t believe that this is not longer implemented and users are only created when they login the first time?
There is no need for any of our users to logon at our firewall.
VPN is not needed because every modern OS has its own client an we do roll out fully configured devices.
WebProxy is transparent.
Mail-Release-Self-service becomes a henn-egg-problem: If there is no user, there will be no mail-address to send a quarantine report to inform that user that he has to login into the XGS to release a mail.
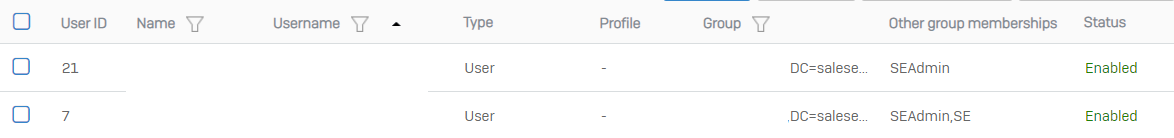
So how can we create/change users in our AD and can publish that to XGS automatically? (push or pull)
I do not believe that the XGS became worse than old SG/astaro.
This thread was automatically locked due to age.