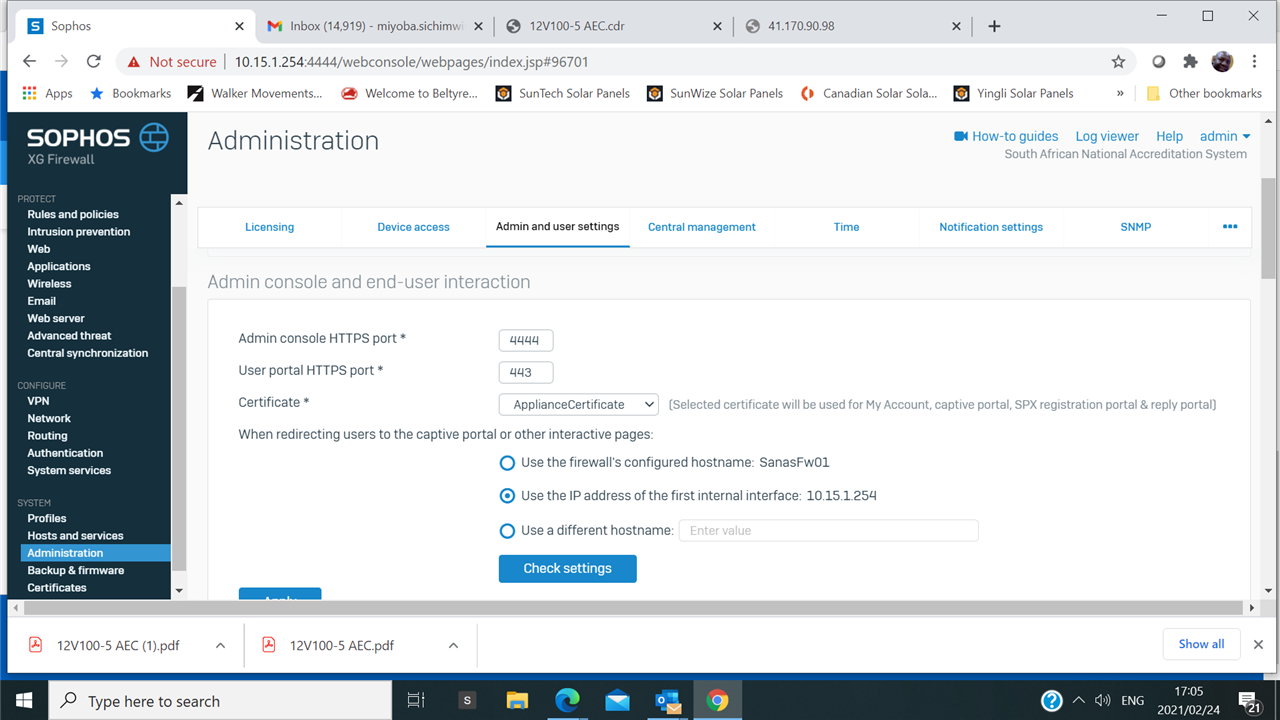
I have a problem that probably started with a IOS upgrade to 17.5 and 18.4. Our Sophos XG could allowed our users to download vpn client by contacting our public interface, however, that is only possible after activating appliance_access on the console, but this disrupts all other internet traffic and renders this useless, as we have more critical services running through internet traffic. I have tried sophos tech but its useless.
This thread was automatically locked due to age.