Hi,
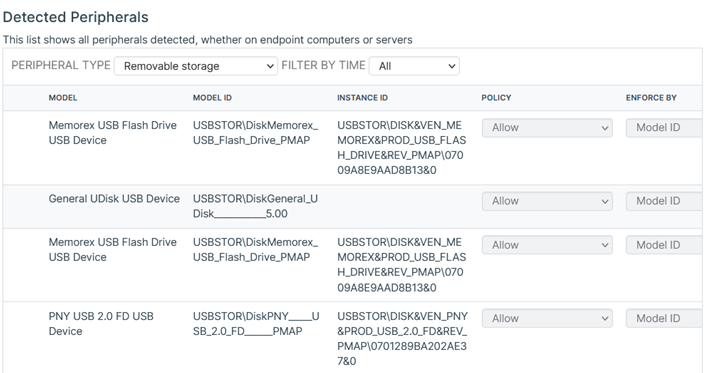
We wanted to issue company-owned USB drives and then use Sophos to block all other USB drives. This seemed straightforward - buy USB drives, plug them in with peripheral control in monitor mode to get the InstanceIDs of each USB stick, and then block USB storage with exceptions for the InstanceIDs collected in the previous step.
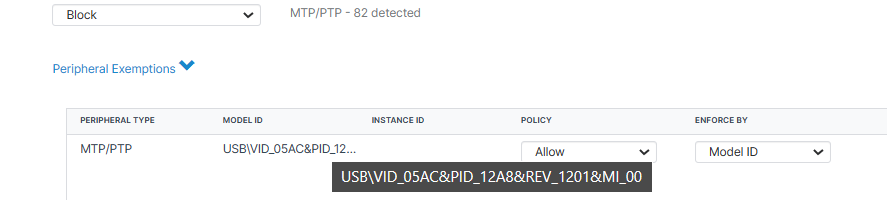
However, after we purchased the USB drives, we noticed that Sophos peripheral control does not enumerate the InstanceIDs of these USB sticks.
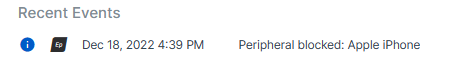
This problem was raised in the forum, and it appears that if the InstanceID has the "&" character in it, then Sophos Peripheral control leaves the InstanceID blank. Unfortunately, the response from Sophos was to discuss with them directly, and then the thread was locked:
Are there any plans to fix this bug?
Is there another way to block all USB drives except for certain specific USB drives (as opposed to a drive model)?
Thanks,
Ken
This thread was automatically locked due to age.