Hello Sophos Community,
my name is David Lorenz and I am a it service provider with many customers. Our customers use Windows Server 2016 and 2019 as a virtual VMware machine.
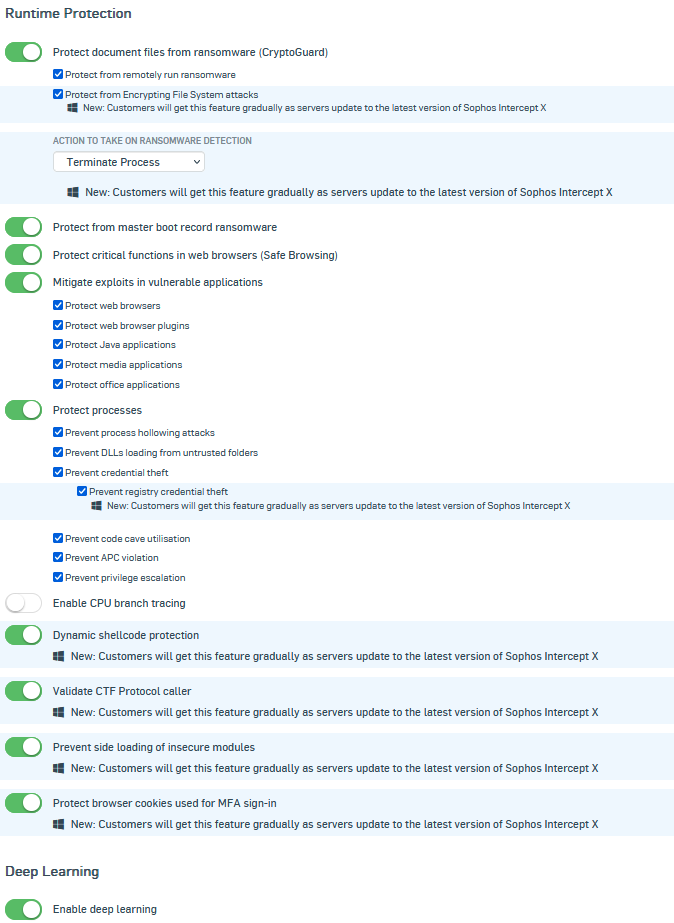
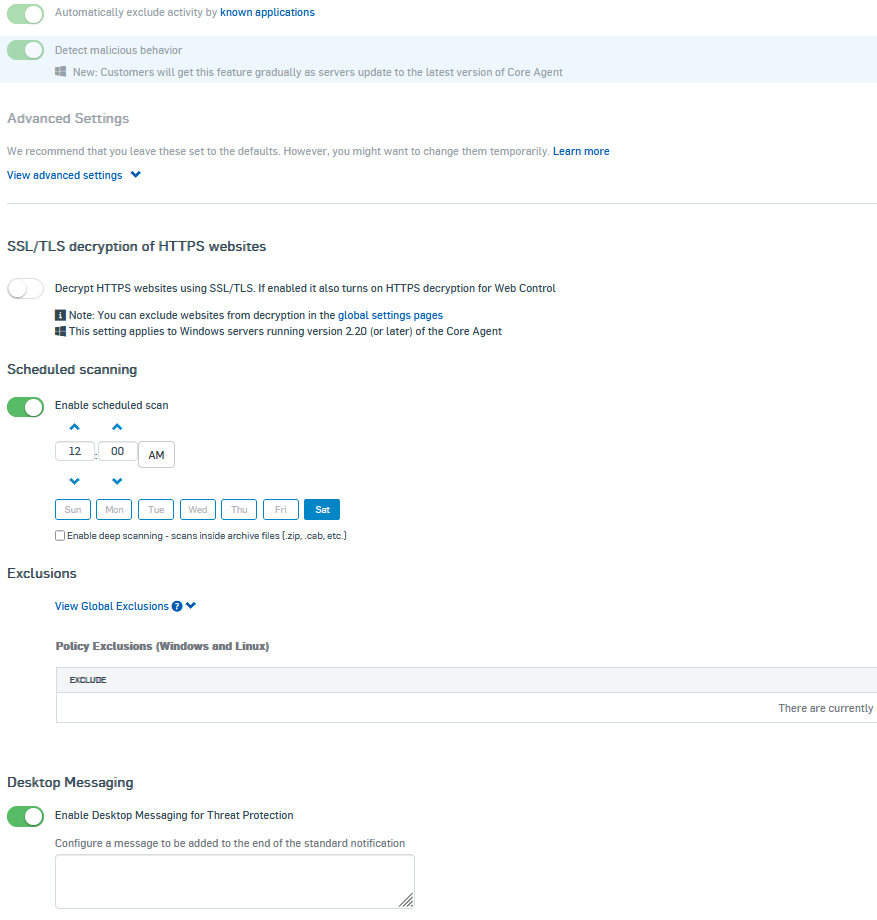
They use Intercept X Advanced with XDR for Server or Intercept X Essentials.
Montly we install Windows Updates on our customers servers. The problem is that the installation need so much time because of running sophos services with extrem high cpu usage while Windows Update installation process.
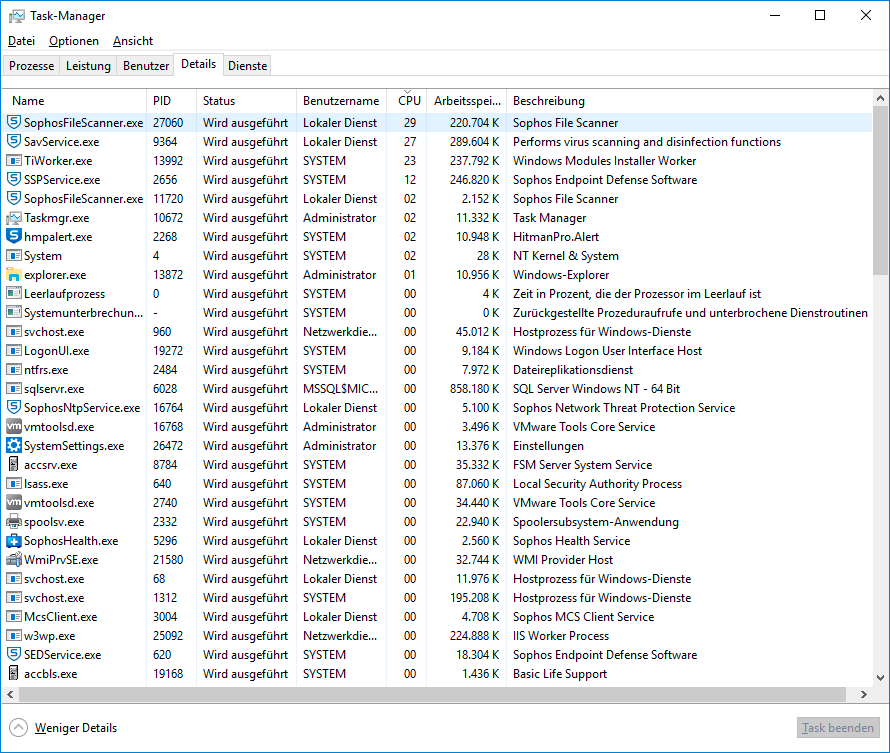
Thats the policy configuration:

Do you have a idea what we can do for our customers? Many thanks in advance.
PS. i have already researched on the internet
This thread was automatically locked due to age.

