I've recently updated to latest version (19), not sure if it's related.
I've added a simple rule to allow ssh between two machines in different vlans, but didn't work. I tried stripping down some restriction to Any-Any between the whole subnets and no user matching to try to troubleshoot it, but still no luck. Got literally dozens of similar rules, all working fine.
I am totally sawmped on what would be the reason the rule doesn't trigger at all and just gets ignored.
Anyone has a suggestion?
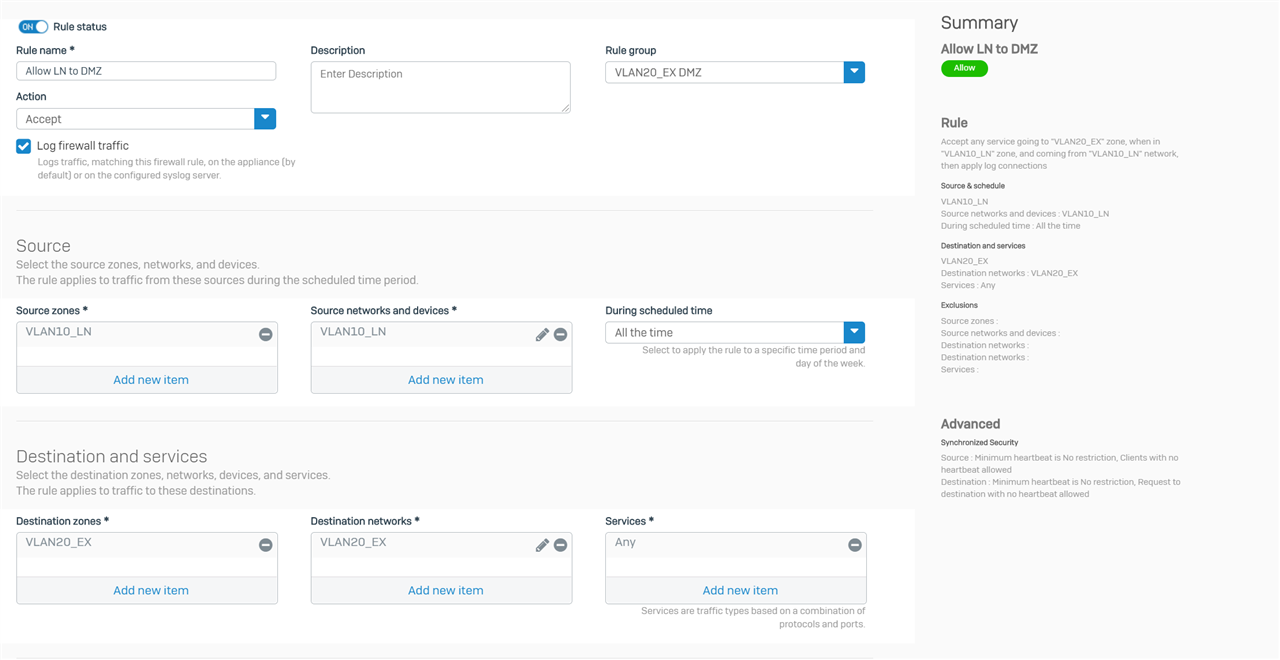
Here's the rule: (the two IP ranges are 172.21.10.0/24 as the source and 172.21.20.0/24 as the destination, and they work fine in other rules)
And some logs: (Rule #8 is a drop all and log as the very last rule)
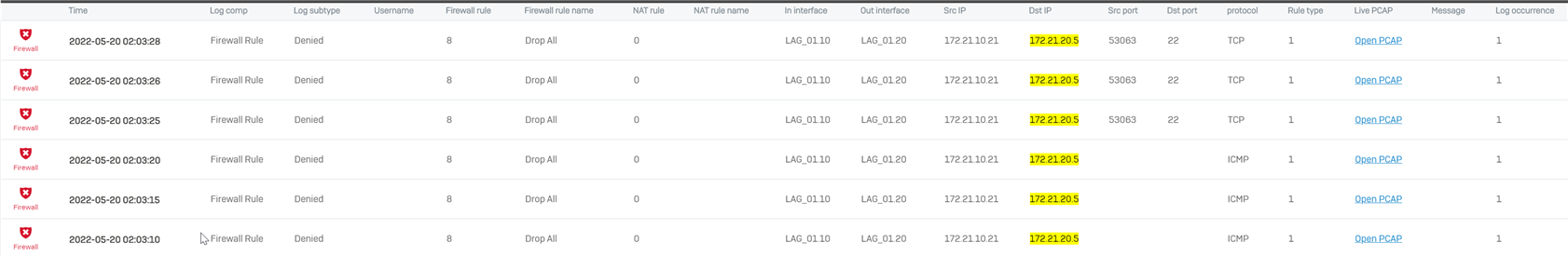
And all the details of the topmost logs if it helps:
2022-05-20 02:03:28Firewallmessageid="00002" log_type="Firewall" log_component="Firewall Rule" log_subtype="Denied" status="Deny" con_duration="0" fw_rule_id="8" fw_rule_name="Drop All" fw_rule_section="Local rule" nat_rule_id="0" nat_rule_name="" policy_type="1" sdwan_profile_id_request="0" sdwan_profile_name_request="" sdwan_profile_id_reply="0" sdwan_profile_name_reply="" gw_id_request="0" gw_name_request="" gw_id_reply="0" gw_name_reply="" sdwan_route_id_request="0" sdwan_route_name_request="" sdwan_route_id_reply="0" sdwan_route_name_reply="" user="" user_group="" web_policy_id="2" ips_policy_id="0" appfilter_policy_id="0" app_name="" app_risk="0" app_technology="" app_category="" vlan_id="" ether_type="IPv4 (0x0800)" bridge_name="" bridge_display_name="" in_interface="LAG_01.10" in_display_interface="VLAN10_LN" out_interface="LAG_01.20" out_display_interface="VLAN20_EX" src_mac="fc:34:97:1e:77:6e" dst_mac="" src_ip="172.21.10.21" src_country="R1" dst_ip="172.21.20.5" dst_country="R1" protocol="TCP" src_port="53063" dst_port="22" packets_sent="0" packets_received="0" bytes_sent="0" bytes_received="0" src_trans_ip="" src_trans_port="0" dst_trans_ip="" dst_trans_port="0" src_zone_type="" src_zone="" dst_zone_type="" dst_zone="" con_direction="" con_id="" virt_con_id="" hb_status="No Heartbeat" message="" appresolvedby="Signature" app_is_cloud="0" log_occurrence="1" flags="0" web_policy="Deny All"
This thread was automatically locked due to age.


