I had updated the firmware for sophos firewall yesterday and after that we are facing the captive portal issue.
Our setup:
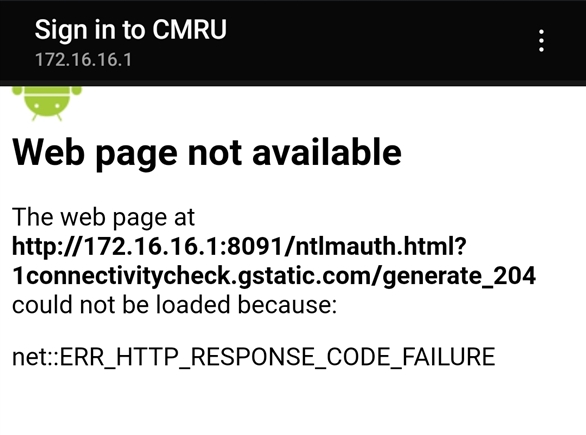
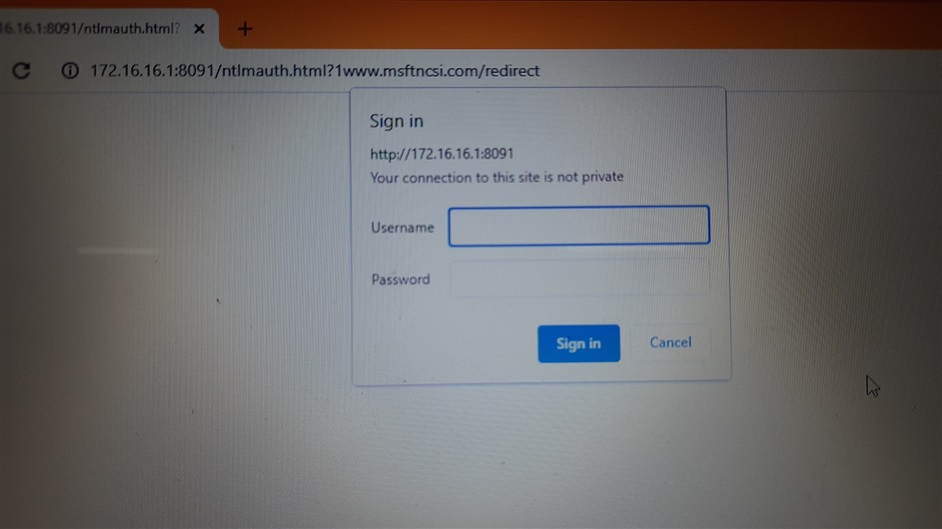
We have STAS enabled for domain systems where users can use internet directly after logging into domain pc's, those who are out side domain environment will get a captive portal to access the internet. Since the latest firmware update, we are not getting redirected to the captive portal instead we get the ntlm page. I have attached screenshots. Need a solution.
This thread was automatically locked due to age.


