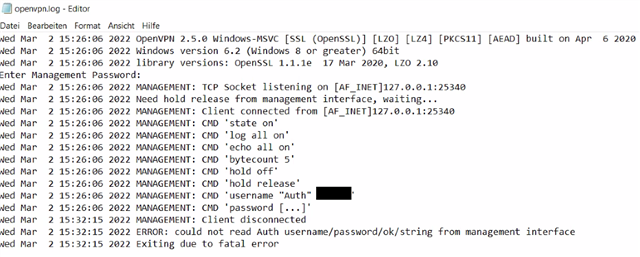
Today we came accross the issue with multiple live users, that Connect client deployed with pro file, does not work when the user has a password beginning with #
Like with space/blank known not working. https://community.sophos.com/sophos-xg-firewall/f/discussions/129828/sophos-connect-client-2-1-20-0309---password-with-spaces-in-it-fails-login
When deployed with the pro file, the client can connect to the userportal and it downloads the protected file. Can see the change in file size and in the XG log file that the user logged in to userportal.

But after it connects to the firewall, it never get's there. Just does nothing while showing "authenticating"
May I know if there is a list of password characters and combinations not working?
I could lough at it if it was'nt so serious. What a joke of a program.
This thread was automatically locked due to age.

