Hello,
we just bought a Sophos XG Firewall and i ran into some problems. I'm pretty new to the Sophos Universe and even to VLANs.
For testing purposes i setup two laptops on a managed Dell Switch (62xx Series, Port 26 and Port 28). I connected the XG on Port 39.
The Switch-Port-Configuration is as followes:
...
configure
vlan database
vlan 2247
exit
...
interface vlan 2247
name "Test"
exit
...
interface ethernet 1/g26
spanning-tree portfast
switchport access vlan 2247
lldp transmit-tlv sys-name sys-desc
exit
...
interface ethernet 1/g28
spanning-tree portfast
switchport access vlan 2247
lldp transmit-tlv sys-name sys-desc
exit
...
interface ethernet 1/g39
spanning-tree portfast
switchport mode general
switchport general allowed vlan add 2247 tagged
lldp transmit-tlv port-desc sys-name sys-desc sys-cap
exit
...
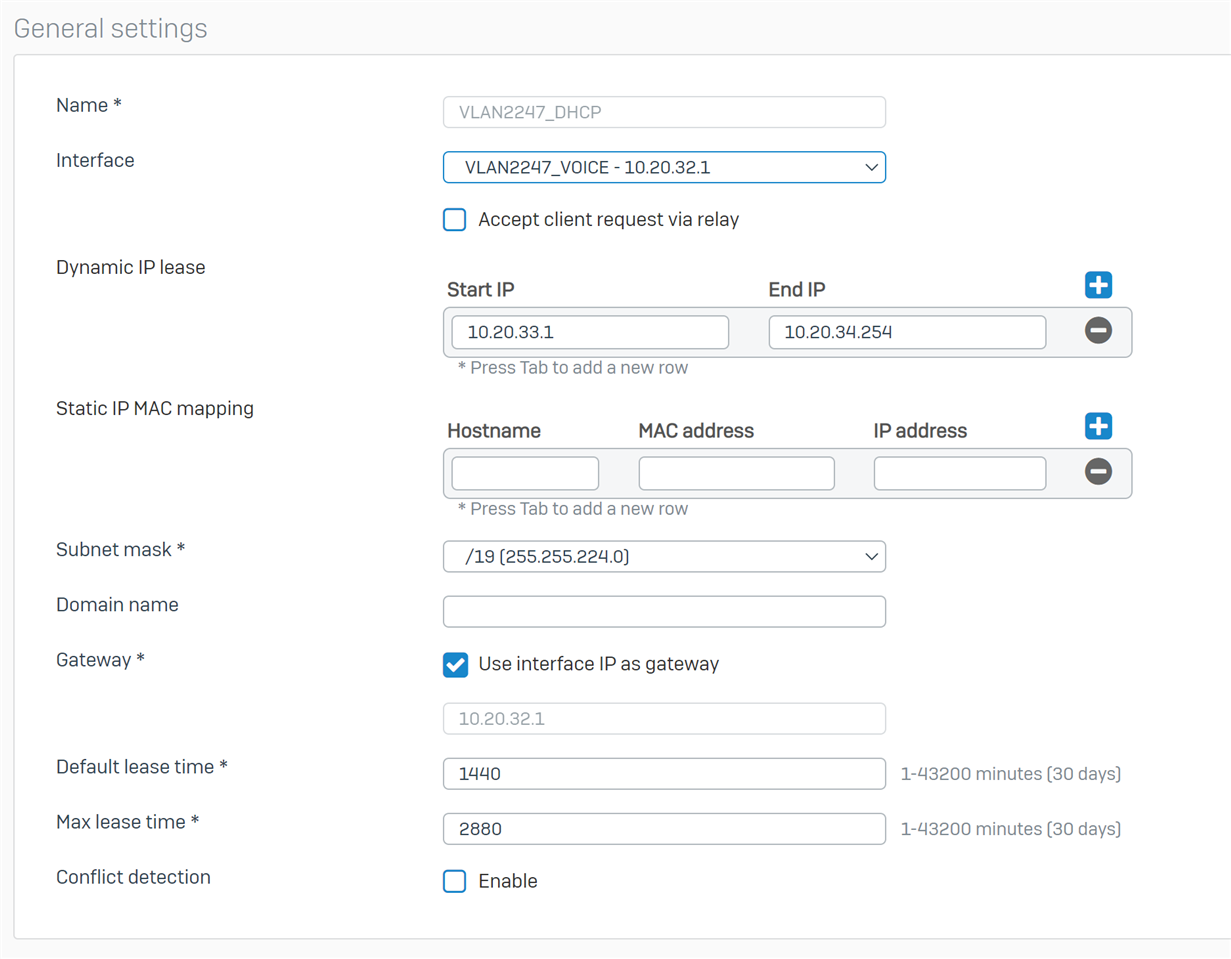
On the XG i added a new vlan interface on port 1 with a new subnet 10.20.32.1/19.
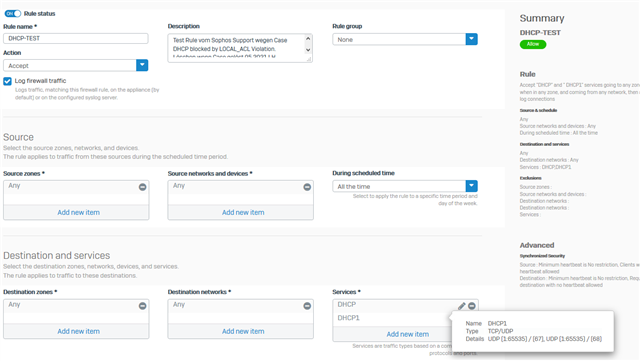
Then i created a dhcp scope for interface Port1.2247 and created a firewall-rule, allowing everything.
If the laptops have a static ip, they can reach the internet, the XG and the laptops themselves.
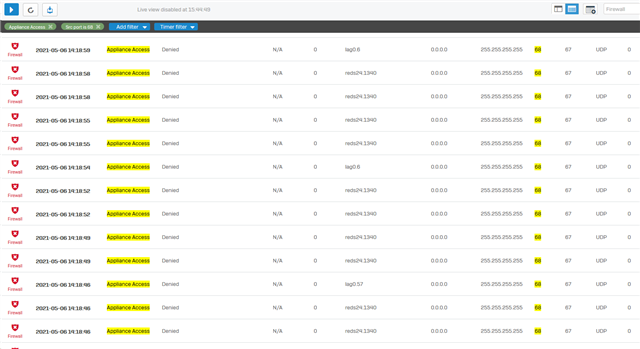
But they do not aquire a IP-Address through DHCP.
Am i missing something? Thank you
Chris
This thread was automatically locked due to age.