Hi Everyone,
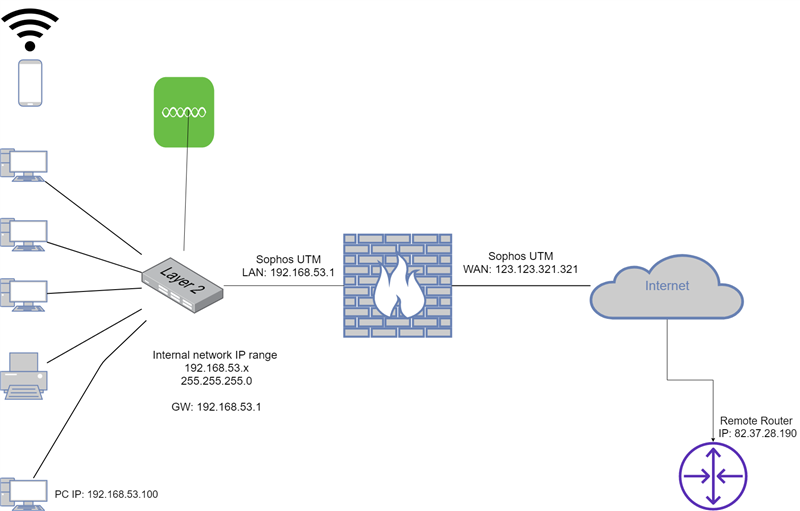
Been reading a lot of posts on here recently to assist me with setting up my Sophos UTM. All seems OK so far except one thing that I just can't work out. At present, I have my Sophos UTM filtering web traffic in transparent mode for both HTTP and HTTPS traffic. I also have the firewall enabled along with the IPS and TCP and UDP flood etc. I have web protection set up and all working as expected.
I also have remote access for L2TP users set up which allows me to connect to my Sophos UTM remotely, which also works and I can access any machine on the internal network.
Now, I need to access remote networks that aren't my own from my local network through the Sophos UTM, but for the life of me, I cannot get the connection to establish to the remote server. It just times out. I have set my machine's IP address to be whitelisted through the web filtering. I have also set up a rule that allows all traffic from the destination IP address and my Local machine's IP address to be allowed and for both L2TP and IPSEC traffic but it still doesn't connect. But here's the strange thing. Before I added the rule in the firewall, traffic was getting blocked. Now, there are no logs entered in the firewall, web filter or the Intrusion Prevention logs either. I cannot seem to find any logs that are blocking the traffic.
I also am not sure where else the traffic could be being blocked. I have temporarily disabled all UDP/TCP flooding and even switched off the IP and any other advanced options but still, the VPN doesn't connect.
What am I missing? Hope that you can help.
Thanks,
Mark.
This thread was automatically locked due to age.