Hello everyone,
I have a question that I don't seem to be able to solve.
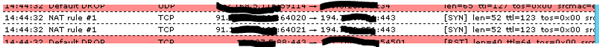
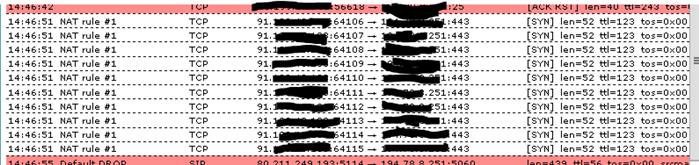
I want to redirect incoming traffic on the port 443 to an internal server port 3000
This is the DNAT rule I have configured.
Now when I go to the following HTTP://IPADDRESS:443 I get redirected to the correct page.
When I try to go to HTTPS://IPADDRESS I cannot make any connection? So the NAT rule is working but the HTTPS is not working.
My questions is this a firewall setting I need to adjust or is this something I need to adjust at the backend?
Kind regards,
Thomas
This thread was automatically locked due to age.