Hello All,
Hopefully this is the correct place for me to post this, if not i do apologize and please kindly inform me where i should be asking this question.
Before i get into my question i need to explain my current setup with you first
I live in a building where the network is managed. I have absolutely no access to the network, and the admins don't want to help out.
There are 14 apartments in this building and everyone is sitting on the same network, same VLAN.. yes that's correct
So when i moved in i just placed a consumer grade router (asus) but now I'm dealing with a double NAT.
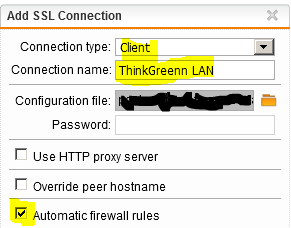
My dad lives 2 floors above me, and i have been trying to figure out a way to setup up a connection between us. This is where Sophos comes in.
To give an idea how the infrastructure in the building
ISP -> Building Router -> Building Switch -> My router -> devices.
I have an Intel NUC i7 with 32gb ram, and i was wondering if i could run Sophos UTM of ESXI.
The NUC only has ONE NIC, so i was wondering if creating 2 virtual NIC would work with LAN and WAN setup, this i'm not sure at all
With this in place the setup would look liks this
ISP -> Building Router -> Building Switch -> My router -> Intel NUC + devices.
I will let my router take care of DHCP.
Question being now, would i be able to use Sophos UTM in this way, and if yes can i use it with 1 NIC so my dad can get access to my internal network?
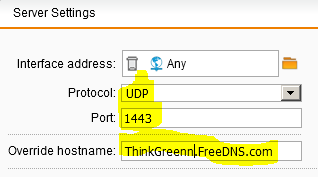
I can't port forward, so i'm not understanding how my dad can reach me if i would use SSL VPN
This thread was automatically locked due to age.