Hi I'am new to Sophos UTM,
I have a Web Filtering Policy blocking Categories including facebook and youtube.
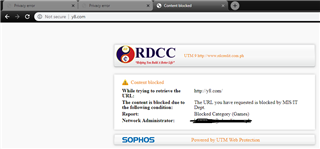
Some sites when blocked are showing the company's logo with web messages but there are also some sites especially facebook and youtube only showing this.
Your connection is not private
Attackers might be trying to steal your information from facebook.com (for example, passwords, messages, or credit cards). Learn more
Please help me fix this. Thank you
This thread was automatically locked due to age.