Hi,
I did a copy of the default live query: File access history
I'm only interested in new files that have been created in that timeframe.
The demand is a bit like the default "New applications deployed" query. But not only for applications.
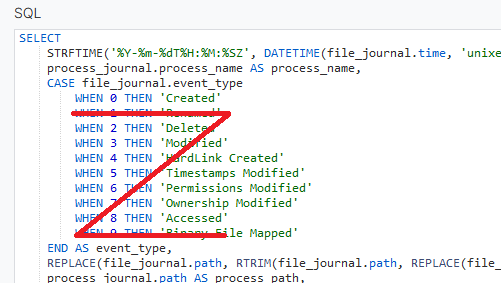
In the default code of "file access history" I removed everything except "created"
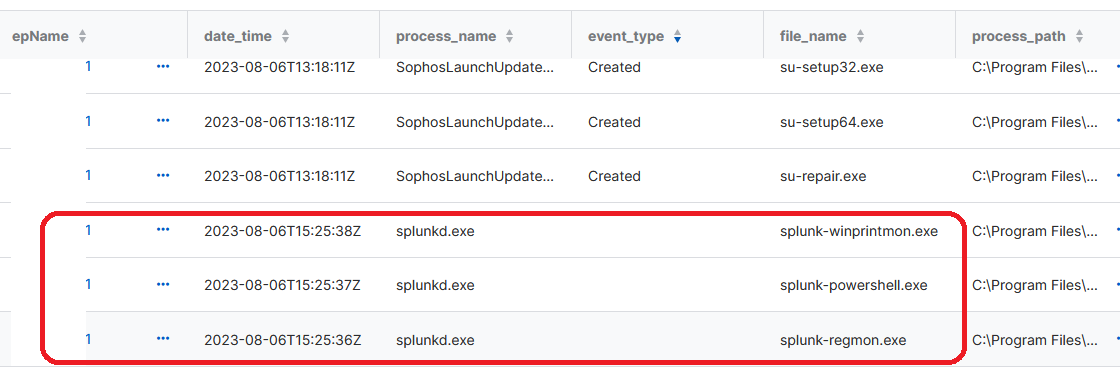
Unfortunately it shows a lot of undescribed file access logs like this when searching for .exe files as an example.
Any Idea how to modify the script that it only finds the "Created" events?
Regards
